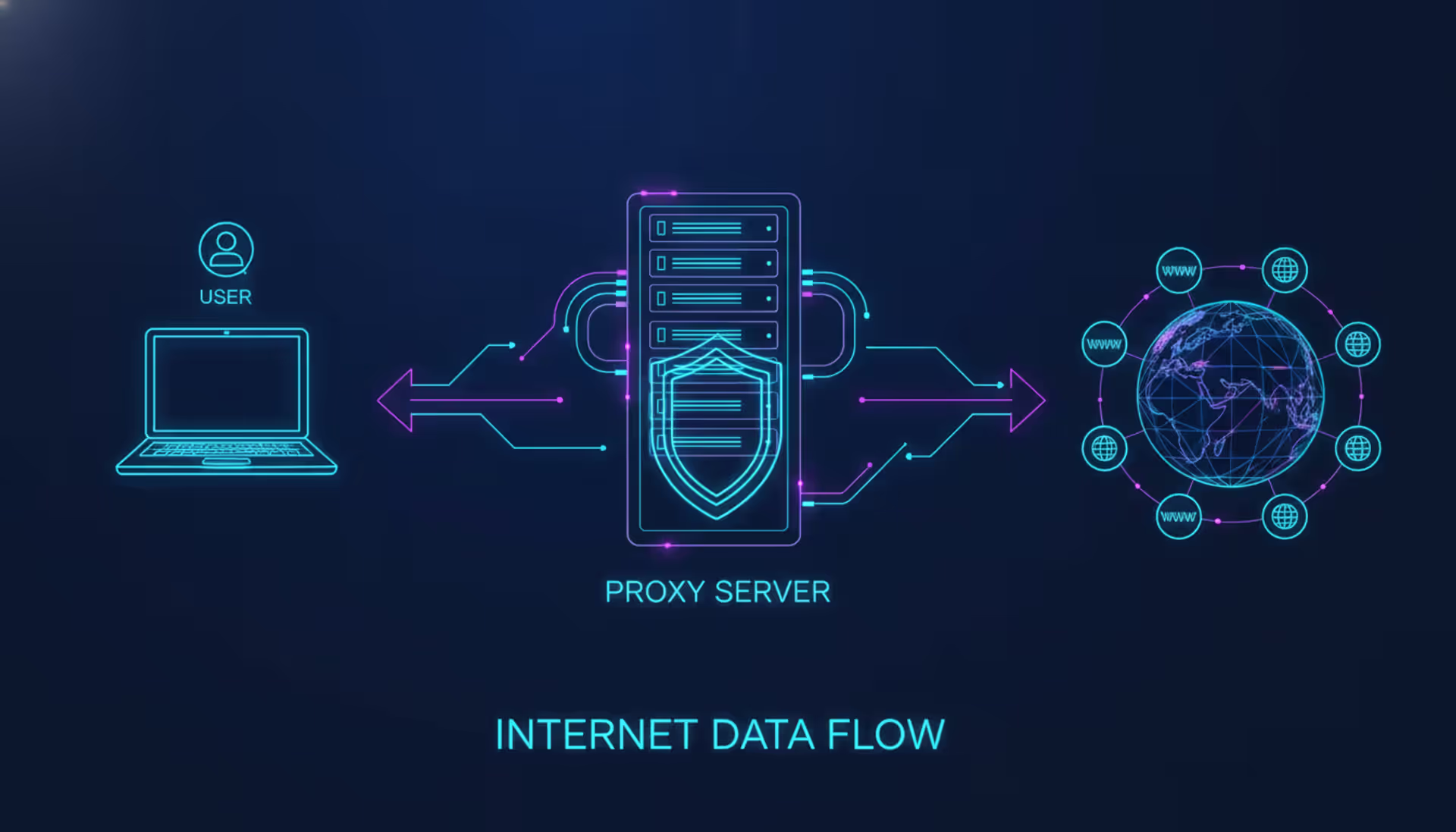
Laptop connecting to websites through a proxy server shown as a shield icon, with glowing data flow arrows on a dark blue background
What Is a Proxy Server?
Content
Content
Think of your internet connection like making a phone call, but through an operator who dials on your behalf. That's essentially what happens with a proxy server—it's a go-between computer that handles your web requests so you don't connect directly to websites. You ask for Facebook, the proxy fetches it using its own address, then hands you the page. Facebook never sees your actual IP address, just the proxy's.
Why bother with this roundabout route? Companies use proxies to block time-wasting websites during work hours, log what employees browse, and add extra security layers against threats. Regular folks? They've got different reasons: watching BBC shows that won't play outside the UK, browsing without leaving digital fingerprints everywhere, or getting around school network blocks. Knowing exactly what proxies can and can't do matters—otherwise you'll make privacy assumptions that leave you exposed.
How Proxy Servers Work
Here's what happens behind the scenes. Type in a web address and hit enter—your laptop sends that request to the proxy first, not to the actual website. The proxy then plays bouncer: checking if you're allowed to visit that site, seeing if it's on any blacklists, maybe writing down that you made this request. Once it's satisfied, the proxy creates its own separate connection to the website you want.
That website thinks it's talking to just another regular visitor. Your real IP address, location, device details—none of that gets through. The website prepares its response and shoots it back to the proxy. The proxy then relays everything to you. Every step of your interaction with that external site gets handled by this middleman.
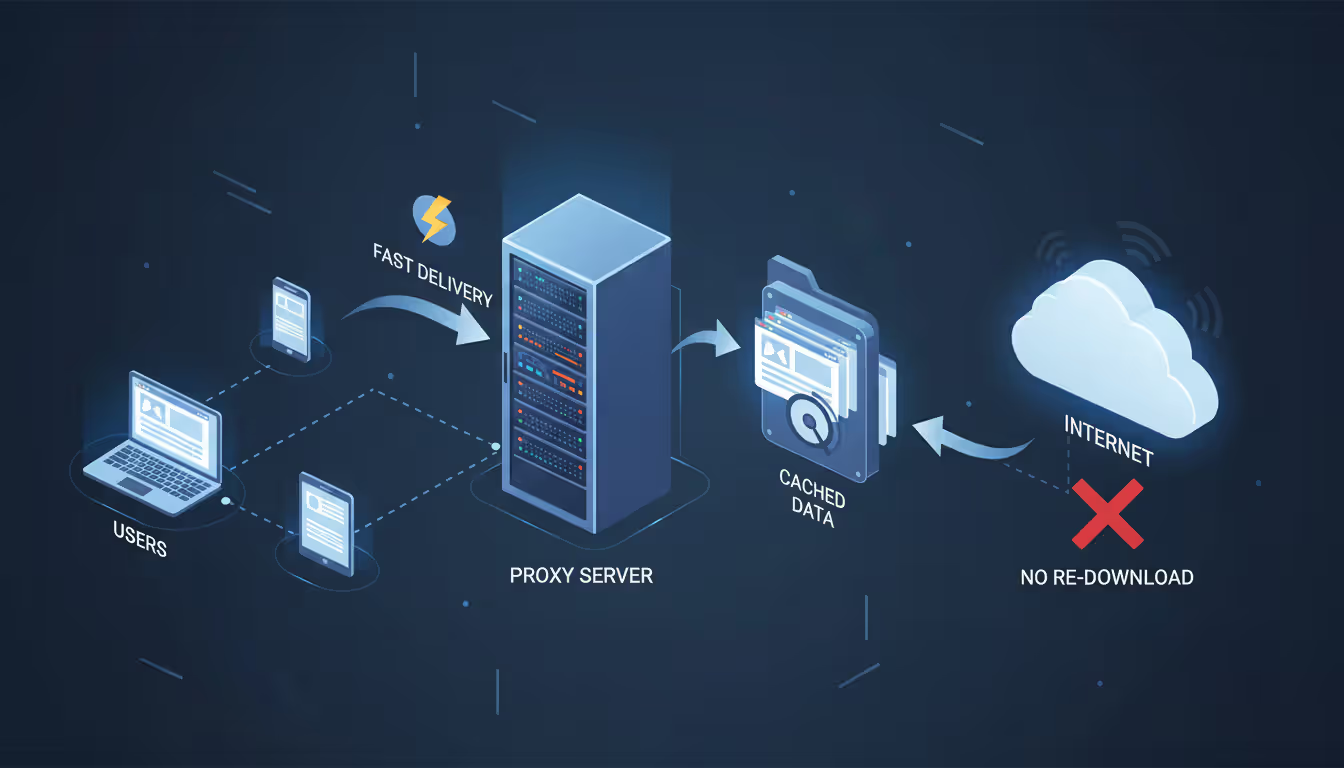
Better proxy systems do more than just relay traffic back and forth. They save copies of popular web pages, images, and videos on their own hard drives. When someone else requests that same BBC article you just read, the proxy grabs it from local storage instantly rather than downloading it from London again. This caching trick speeds things up dramatically and cuts bandwidth costs—especially valuable when you've got 500 students all trying to access the same assignment PDF at 11:45 PM before the midnight deadline.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Diagram suggestion: Show three boxes labeled "Your Computer," "Proxy Server," and "Target Website" with arrows indicating the request flowing right through all three, then the response flowing back left through the same path.
The type of proxy protocol makes a huge practical difference. HTTP proxies understand web traffic specifically—they read and sometimes modify the headers that browsers send. SOCKS proxies work at a lower technical level, simply forwarding whatever data you throw at them without caring whether it's a web page, email, or video game. That flexibility makes SOCKS the go-to choice when you need to proxy something besides Chrome. Want your Spotify traffic routed through a different country? Email client connections anonymized? BitTorrent downloads hidden from your ISP? SOCKS handles all of that. HTTP proxies only work for web browsing.
Types of Proxy Servers
Proxy architecture varies depending on what problem you're trying to solve.
Forward vs Reverse Proxy
Forward proxies work for the users behind them—people like you trying to access the internet. When your school requires you to authenticate before browsing, that's a forward proxy intercepting your traffic. Schools and offices put these at their network edge to block sketchy websites, catch malware downloads before they hit actual computers, and generate reports on who's watching YouTube during business hours. The proxy represents you, hiding your identity while controlling what you can reach.
Reverse proxies flip the script—they protect the servers instead of the users. Almost every major website you visit actually uses reverse proxies sitting in front of their real servers. These systems spread incoming traffic across maybe 50 or 100 backend servers, keep copies of images and stylesheets ready to serve instantly, and prevent anyone from attacking the actual infrastructure directly. Cloudflare runs one of the world's biggest reverse proxy networks. You're never really connecting to the website's actual server—the reverse proxy handles everything.
Transparent and Anonymous Proxies
Transparent proxies don't hide the fact that they're proxies. They include your real IP address in technical headers and explicitly announce themselves. Network admins love these because your phone or laptop needs zero configuration—the network just automatically routes everything through the proxy using behind-the-scenes rules. You might not even realize you're going through a proxy until you try visiting Instagram and get a "blocked by network policy" message.
Anonymous proxies strip out your IP address but still admit they're proxies in their headers. Websites can't trace the traffic back to you personally, but they know someone's using a proxy. Elite proxies (also called high anonymity proxies) delete all identifying details while pretending to be regular direct connections. Websites think you're just another normal visitor browsing from home. This total stealth becomes crucial for things like scraping product prices or serious privacy situations.
Common Proxy Server Uses and Examples
Real businesses and regular people deploy proxies to solve actual problems they're facing.
Take a university with 5,000 students connected to campus WiFi. Every single web request flows through centralized proxy servers that throttle Netflix during class hours, automatically block malware-serving domains, and cache operating system updates for the entire campus. When a student loads CNN.com, the proxy checks whether someone else accessed CNN in the last 20 minutes—if yes, it instantly serves that stored copy. Multiply those bandwidth savings across thousands of students checking the same news sites and you're saving serious money on internet costs.
Testing teams and market research companies rely heavily on location-specific proxy access. Say Netflix is launching in Brazil and needs to verify that Brazilian subscribers see Portuguese subtitles with correct pricing in reais. Their QA engineers route test accounts through Brazilian proxy servers to experience exactly what actual customers in São Paulo will see. Marketing agencies do similar research—a firm analyzing Coca-Cola's advertising runs their browsers through French proxies to view the specific ads that French audiences encounter, since Facebook shows completely different campaigns based on your location.
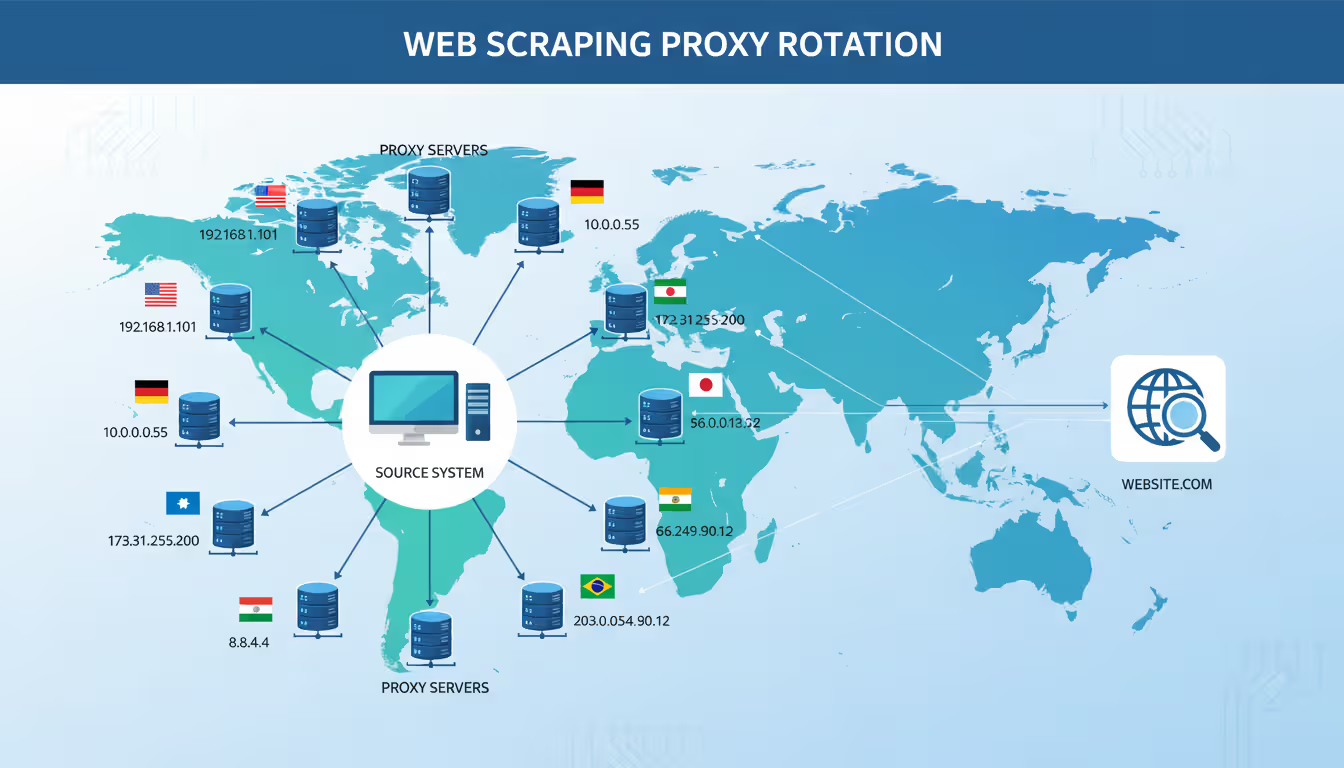
Web scraping operations simply can't function without rotating through different proxy IPs. A flight comparison site checking prices on Expedia, Kayak, Priceline, and 30 other booking platforms generates maybe 50,000 automated requests per hour. Without proxies, Expedia's systems would instantly recognize thousands of connections from one IP address and block it as bot traffic. The scraper rotates through a pool of perhaps 3,000 different proxy addresses, making each request look like it's coming from a different regular consumer in various cities. This distributed pattern flies under the radar of anti-bot systems.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Major e-commerce sites depend on reverse proxy load balancing to stay online during traffic spikes. When Apple announces a new iPhone, their reverse proxy layer sits upstream from maybe 200 application servers, constantly monitoring which ones have capacity and routing new visitors accordingly. If three servers crash under the load, the proxy detects those failures within seconds and redirects all traffic to the remaining healthy servers. Customers never see error messages—the proxy invisibly handles infrastructure problems.
Proxy Server vs VPN
Both technologies route your traffic through intermediary servers, but they work quite differently under the hood.
| Feature | Proxy Server | VPN |
| Encryption | Usually none—only your HTTPS connections stay encrypted | Encrypts everything from your device to the VPN server |
| Speed | Faster since there's no encryption processing | Usually 5-15% slower from encryption overhead |
| Cost | Lots of free options; paid services run $5-50/month | Decent providers charge $5-15 monthly |
| Anonymity Level | Moderate—hides your IP but data travels unencrypted | Better—hides IP and encrypts all traffic and metadata |
| Best Use Case | Bypassing regional blocks, scraping websites, content filtering | Protecting sensitive data, securing public WiFi, complete privacy |
| Setup Difficulty | Configure each browser or app individually | Install once, protects everything automatically |
Proxies work at the application level, which means configuration gets granular—but also tedious. Set up a proxy in Chrome? Your browser uses it, but Discord, Steam, Dropbox, and everything else still connects directly through your regular internet connection. This selective routing gives you control—maybe you want to proxy web traffic but let Steam download game updates at full speed—but you'll need to configure each program separately.
VPNs operate at the operating system level by creating encrypted tunnels for absolutely everything. Install a VPN client once and every program on your computer automatically routes through it. The encryption protects your data from your internet provider, coffee shop WiFi operators, or anyone else snooping on your connection. The tradeoff? Encryption processing adds a small speed penalty.
Go with a proxy when you need selective routing for specific apps, maximum speed for heavy downloads, or quick access to geo-blocked content. A researcher comparing Google search results across different countries doesn't need device-wide encryption—a browser proxy accomplishes the goal while other programs run at full speed.
Go with a VPN when security trumps convenience. A consultant accessing client databases from hotel WiFi absolutely needs the encryption VPNs provide. Anyone worried about their internet provider tracking every website they visit—not just cookies from the websites themselves—benefits from VPN's comprehensive protection. The slight speed hit becomes worthwhile when data security takes priority.
Some situations call for both simultaneously. A penetration tester might run a VPN for baseline privacy while routing specific reconnaissance traffic through rotating proxies. The VPN encrypts everything, while proxies provide IP diversity for testing without triggering rate limits on target systems.
How to Set Up a Proxy Server
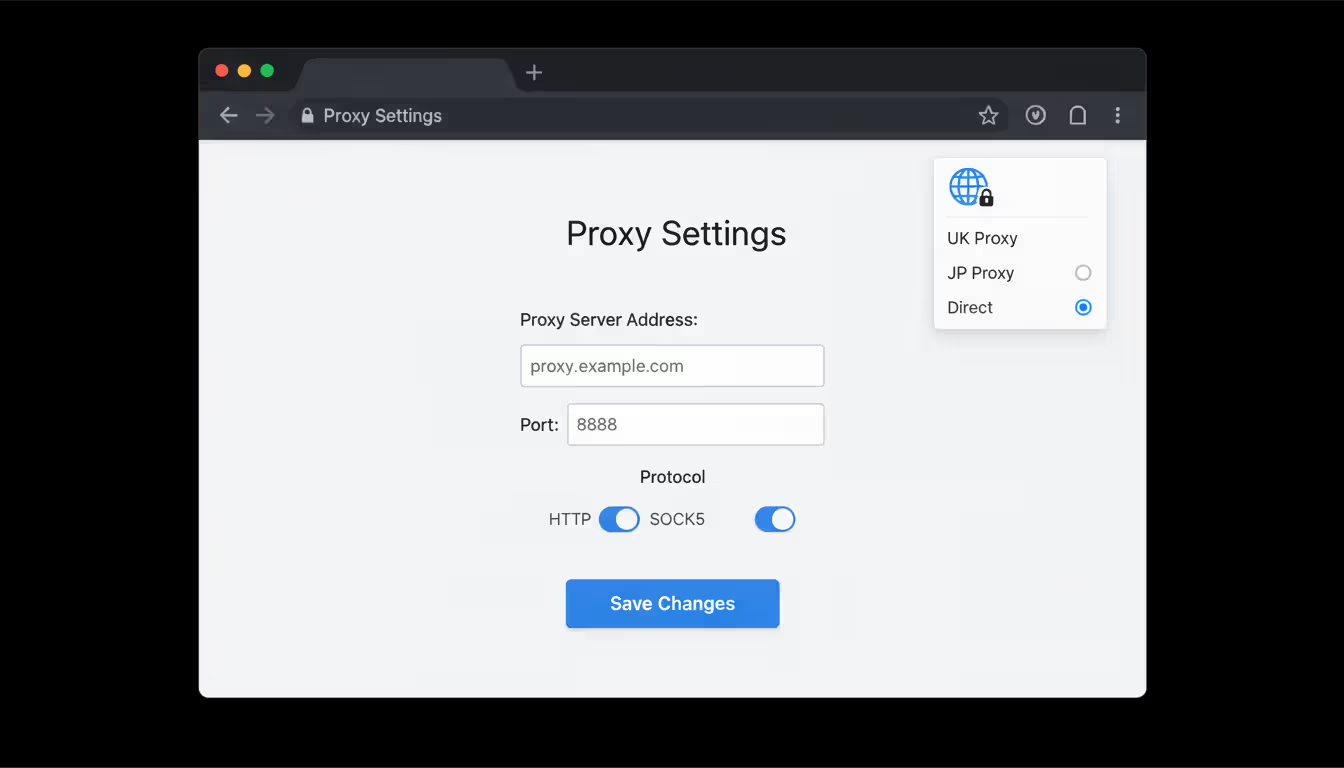
Proxy configuration requires three core pieces of information: the proxy server's address, which port it's listening on, and login credentials if it requires authentication.
Browser Proxy Configuration
Browsers let you control web traffic routing without affecting other programs on your computer.
Chrome and Edge don't have their own proxy settings—they use whatever your operating system is configured to use. Click Settings, scroll to System, then select "Open your computer's proxy settings," which launches your OS configuration panel. For Chrome-specific proxies, install an extension or launch Chrome with special command-line flags.
Firefox maintains its own proxy configuration separate from system settings. Open the menu, select Settings, scroll down to Network Settings, and click the Settings button. Choose "Manual proxy configuration" and type in your HTTP Proxy address plus port number (commonly 8080, 3128, or 8888). Check "Use this proxy server for all protocols" unless you're routing different traffic types through different proxies. The "No Proxy for" field takes comma-separated domains for sites that should bypass the proxy—useful for accessing your router's admin page at 192.168.1.1 or internal company resources.
Extensions make proxy management way more convenient. FoxyProxy and Proxy SwitchyOmega let you define multiple proxy configurations and switch between them with toolbar buttons. Set up separate profiles for your UK proxy, Japanese proxy, and direct connection, then toggle based on what content you're accessing. No more diving through settings menus every time you need different routing.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Operating System Setup
System-level configuration affects all programs that respect proxy settings (though plenty of applications ignore these and connect directly anyway).
For Windows configuration, launch Settings, navigate to Network & Internet, and select the Proxy section. Find the Manual proxy setup area, flip the switch to "On" for using a proxy server, then fill in the address and port fields. The bypass list accepts semicolon-separated entries like localhost;127.0.0.1;*.local for addresses requiring direct connections. Power users can write PAC (Proxy Auto-Config) scripts with complex routing logic based on destination URLs or network conditions.
For macOS configuration, launch System Preferences, select Network, click Advanced, and switch to the Proxies tab. Check boxes for traffic types you want proxied: "Web Proxy (HTTP)" for regular web traffic, "Secure Web Proxy (HTTPS)" for encrypted connections, "SOCKS Proxy" for SOCKS5 traffic. Enter server details for each selected protocol. The "Bypass proxy settings for these Hosts & Domains" field works like Windows exceptions. Changes take effect immediately for new connections.
Command-line programs use environment variables for proxy configuration. Add these lines to your shell profile (.bashrc, .zshrc, or whatever your shell uses):
export http_proxy="http://proxy.example.com:8080"
export https_proxy="http://proxy.example.com:8080"
Tools like curl, wget, and git automatically honor these variables. Authenticated proxies need credentials embedded in the URL: http://username:password@proxy.example.com:8080. Just remember these credentials become visible in process listings and potentially log files.
Specialized client software forces stubborn applications through proxies. Proxifier (available for Windows and macOS) uses system hooks to force non-compliant programs through your proxy regardless of their individual settings. Commercial proxy providers often bundle custom clients that handle authentication, automatic IP rotation, and failover without manual configuration.
Proxy Server Security and Limitations
Proxies boost privacy in some ways but fall short of comprehensive security protection.

Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Standard proxy connections don't encrypt traffic between you and the proxy server. Your ISP, company network admin, or anyone sniffing your WiFi can observe which domains you're visiting and capture any unencrypted data. HTTPS connections maintain end-to-end encryption to the destination website, but the proxy still sees which domain you're accessing through SNI (Server Name Indication) during the TLS handshake. Page content stays private, but your browsing history doesn't.
Logging creates a fundamental trust problem. Free proxy services need to make money somehow—often by recording all user activity and selling that behavioral data to advertisers, market researchers, or whoever's buying. You're trading one watcher (your ISP) for another (the proxy operator), potentially with worse privacy practices or subject to different legal jurisdictions. Commercial proxy services sometimes publish transparency reports and get third-party audits, but you can't really verify their claims independently.
The biggest mistake people make with proxies is assuming they provide the same security as VPNs.A proxy changes your IP address, but without encryption, your data remains vulnerable to interception. For true privacy, you need both—or just use a VPN from the start
— Marcus Chen
Malicious proxy operators represent real security threats. An attacker running a "free public proxy" can inject malicious JavaScript into unencrypted pages, swap legitimate downloads with malware-infected files, harvest login credentials, or redirect banking sessions to convincing fake sites. Even legitimate proxy services occasionally get compromised by sophisticated attackers. Never send sensitive stuff—passwords, credit card numbers, Social Security numbers—through proxies you haven't thoroughly vetted and completely trust.
Performance problems affect everyday usability. Each proxied request adds network latency from the extra routing hop. Overcrowded proxy servers suffer congestion slowdowns. Geographically distant proxies (routing through Singapore when you're in New York) add hundreds of milliseconds to every request. Shared proxy IPs might already be flagged by fraud detection systems, triggering constant CAPTCHA challenges or outright blocks from banking sites, Netflix, and other services actively fighting proxy usage. Residential proxy networks avoid this issue but cost 10-50 times more.
Application compatibility stays inconsistent across different programs. Browsers and HTTP-based tools universally support proxy configuration, but countless other applications don't. Online games, desktop streaming apps, proprietary business software—many establish direct internet connections regardless of system proxy settings. This creates privacy gaps if you assume your proxy protects all traffic when half your programs bypass it entirely.
Proxies don't stop all tracking methods websites use. Sites implement browser fingerprinting, canvas tracking, and dozens of other identification techniques that work independently of IP addresses. Rotating IPs through proxies doesn't clear cookies, eliminate browser fingerprints, or disable tracking pixels. Real privacy requires layered defenses: cookie isolation, fingerprint randomization, tracker blocking, plus proxies or VPNs—not any single tool by itself.
Frequently Asked Questions
Proxies remain useful networking and privacy tools despite VPNs dominating consumer privacy conversations. They excel at application-specific traffic routing, corporate content filtering, load distribution, and scenarios prioritizing speed over encryption. Grasping different proxy architectures—forward versus reverse, transparent versus anonymous—helps you pick the right technology for specific needs.
The proxy versus VPN decision hinges on your threat model and specific use case. Proxies deliver better speeds and simpler per-application configuration for tasks like accessing geo-restricted content or implementing corporate access controls. VPNs provide comprehensive encryption and privacy protection essential for securing sensitive information and operating in hostile network environments.
When implementing proxy solutions, stick with trustworthy providers, understand the security limitations, and configure exceptions for services needing direct connections. Combined with solid browser hygiene and awareness that IP masking doesn't prevent all tracking, proxies become one component of a comprehensive privacy and network management strategy rather than a complete solution by themselves.
Related Stories

Read more
Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




