Glowing network topology lines connecting server racks in a modern data center with blue and green neon lighting
Network Map Guide
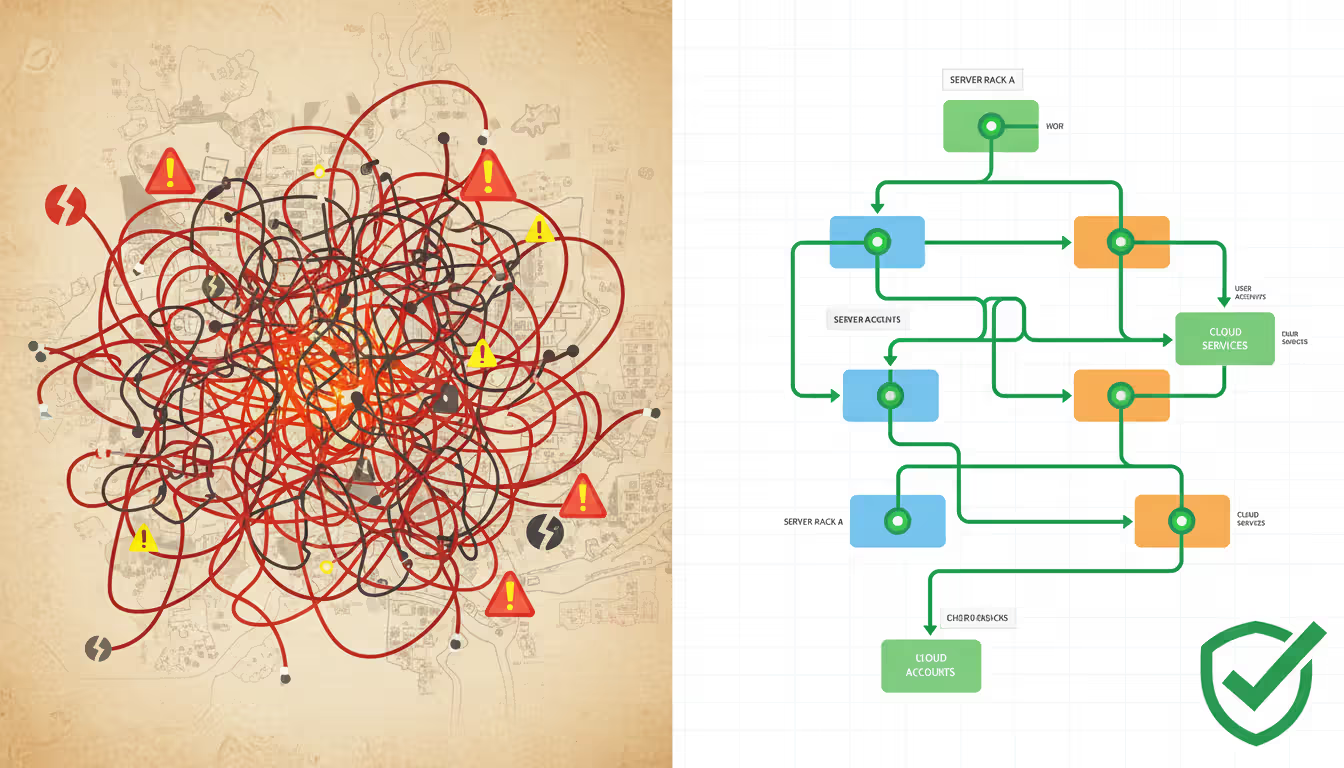
Network infrastructure visibility separates well-managed IT environments from chaotic ones. A network map provides that visibility, transforming abstract connections into concrete visual representations that help teams troubleshoot faster, plan upgrades intelligently, and maintain security posture.
What Is a Network Map and Why Does It Matter?
A network map is a visual representation of your IT infrastructure showing how devices, servers, routers, switches, and endpoints connect and communicate. Think of it as a blueprint for your digital environment—except this blueprint changes constantly as devices join, leave, or reconfigure themselves.
Network mapping serves multiple critical functions. IT administrators use maps to identify single points of failure before they cause outages. Security teams rely on them to spot unauthorized devices or unusual connection patterns. When a server goes offline at 3 AM, a current network map cuts diagnostic time from hours to minutes by showing exactly what depends on that server and what alternative paths exist.
Organizations of all sizes need network maps, but the complexity varies. A 20-person office with basic internet access and a few shared printers needs simple documentation. A hospital with medical devices, guest WiFi, administrative systems, and compliance requirements needs comprehensive mapping with security zone delineation. Manufacturing facilities often require maps that include both IT and operational technology (OT) networks, showing how production equipment connects to management systems.
The consequences of operating without accurate network maps are measurable. Troubleshooting takes three to five times longer when technicians must trace connections manually. Security audits fail when auditors cannot verify network segmentation. Insurance claims for cyber incidents face scrutiny when organizations cannot demonstrate basic infrastructure awareness.

Author: Adrian Keller;
Source: clatsopcountygensoc.com
How Network Mapping Works
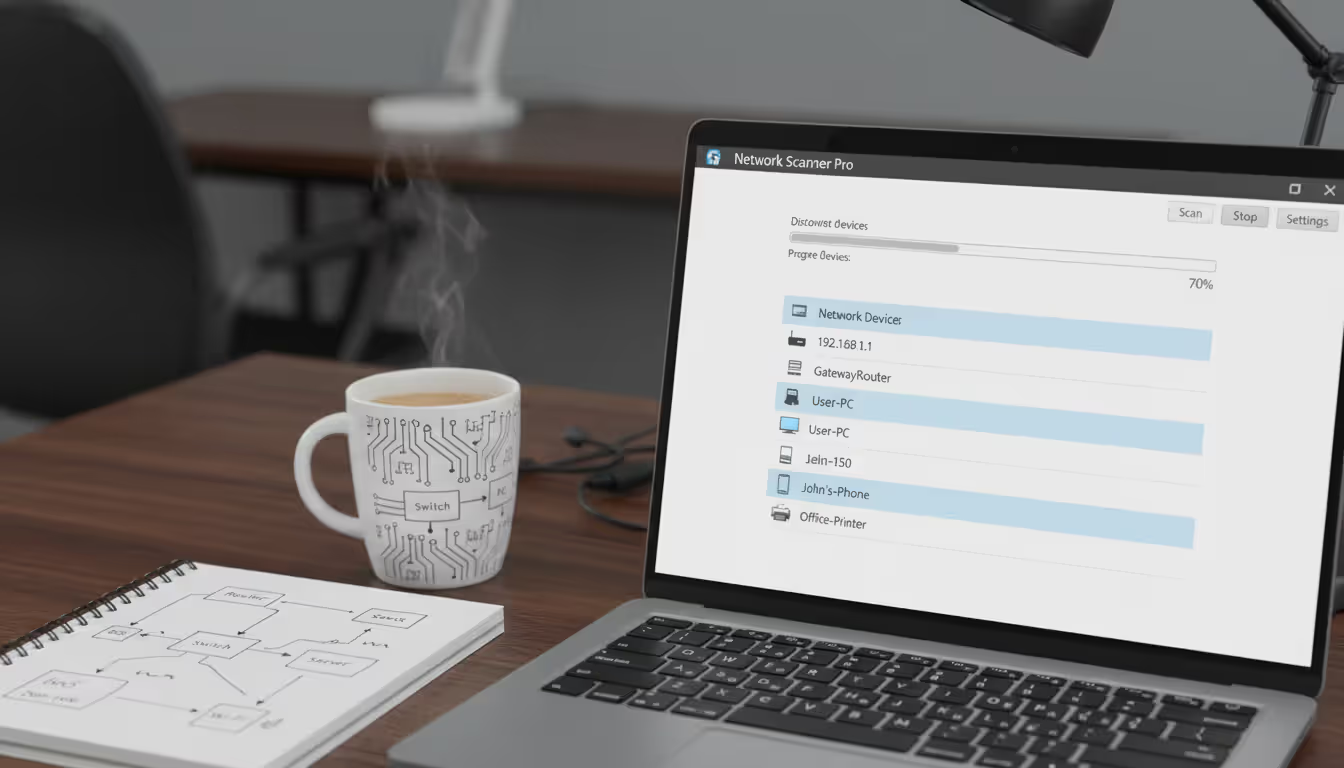
Network mapping combines automated discovery protocols with visualization algorithms to build infrastructure representations. The process starts with device discovery, where mapping tools send out queries using protocols like ICMP (ping), SNMP (Simple Network Management Protocol), or ARP (Address Resolution Protocol) to identify active devices on specified network segments.
Once devices respond, the tool collects identifying information: IP addresses, MAC addresses, hostnames, device types, and operating systems. Managed switches and routers provide additional detail through SNMP queries, revealing which physical ports connect to which devices and what VLANs (Virtual Local Area Networks) segment the traffic.
Topology identification comes next. The software analyzes routing tables, switch port mappings, and traceroute data to determine how devices interconnect. This phase distinguishes between devices that communicate directly versus those that route through intermediaries. Advanced tools detect redundant paths and identify spanning tree configurations that prevent network loops.
Visualization transforms this raw data into comprehensible graphics. Most network map generators offer multiple layout algorithms: hierarchical views that show clear parent-child relationships, radial layouts that emphasize a central core device, or geographic layouts that match physical office locations. The software applies icons representing device types—routers get one symbol, servers another, endpoints a third—and draws connection lines with annotations showing bandwidth, protocol types, or link status.
Real-time monitoring capabilities distinguish basic mapping tools from comprehensive solutions. Instead of creating static snapshots, sophisticated software maintains persistent connections to network devices, updating maps automatically when changes occur. A new laptop joining the WiFi appears within seconds. A failed switch port triggers an alert and visual indicator.
The entire process can complete in minutes for small networks or require hours for enterprise environments with thousands of devices across multiple sites. Network map generators automate most steps, but human validation remains important—especially for identifying device purposes and documenting connections that automated discovery might miss, like out-of-band management interfaces or air-gapped security systems.
Types of Network Maps You Can Create
Physical topology maps document the actual hardware layout and cable connections. These maps show where equipment physically resides: which rack, which room, which building. They include cable types (fiber, copper, wireless), cable runs through walls and conduits, and patch panel connections. Facilities teams use physical maps when planning renovations or investigating cable damage. Data center managers rely on them to optimize cooling and power distribution.
Logical topology maps illustrate how data flows regardless of physical location. These maps emphasize IP subnets, VLANs, routing domains, and firewall zones. A server in Building A and a workstation in Building C might appear as neighbors on a logical map if they share a VLAN, even though they're physically distant. Network engineers prefer logical maps for troubleshooting routing issues, configuring access control lists, or planning subnet expansions.
Hybrid maps combine physical and logical elements, offering context-appropriate detail. You might see physical locations at the top level, with drill-down views showing logical segmentation within each location. These maps work well for organizations with multiple sites that need both perspectives—understanding that the Chicago office connects to headquarters via MPLS circuits (physical) while sharing the same Active Directory domain (logical).
Wireless network maps specialize in WiFi and other radio-frequency connections. They display access point locations, coverage areas, channel assignments, and client associations. Heat maps overlay signal strength data onto floor plans, revealing dead zones or interference problems. With wireless networks now carrying majority traffic in most offices, dedicated wireless maps have become essential rather than optional.
Application dependency maps represent a newer category focused on software rather than hardware. These maps show which applications depend on which servers, databases, and external services. When planning to patch a database server, an application dependency map instantly reveals which business systems will be affected and when maintenance windows make sense.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Choosing the Right Network Map Software
Selecting appropriate network map software requires matching capabilities to your specific requirements rather than chasing feature lists. Auto-discovery functionality ranks as the most critical capability. Manual network documentation fails because it's tedious and immediately outdated. Look for tools that support multiple discovery protocols and can traverse multiple network segments without requiring agents on every device.
Real-time monitoring separates documentation tools from management platforms. If your map only updates when you manually run scans, you're always looking at stale data. Continuous monitoring detects changes within minutes—new devices, failed links, configuration modifications. This capability matters most in dynamic environments where devices frequently join and leave the network.
Customization options determine whether maps remain useful as your network grows. Can you create custom device icons? Define color coding schemes that match your documentation standards? Group devices by department, function, or security zone? The best network map tools let you tailor visualizations to your team's mental models rather than forcing you into the vendor's preferred layout.
Scalability concerns affect organizations planning for growth. A tool that handles 100 devices smoothly might choke on 1,000. Enterprise-grade solutions manage tens of thousands of devices across global networks, but they cost accordingly. Consider your three-year growth projection when evaluating options.
Integration capabilities extend mapping value beyond visualization. Can your network map software feed data to your ticketing system, configuration management database (CMDB), or security information and event management (SIEM) platform? APIs and webhooks enable automated workflows—like creating tickets when new unauthorized devices appear or updating your CMDB when network changes occur.
Free vs. Paid Network Map Tools
Free open-source network map tools offer legitimate capabilities for budget-conscious organizations. Tools like Nagios, Zabbix, and NetXMS provide discovery, monitoring, and basic mapping without licensing costs. The tradeoffs involve steeper learning curves, limited support options, and responsibility for maintaining the software yourself. Small IT teams comfortable with Linux and scripting can build robust mapping solutions around open-source foundations.
Paid commercial software delivers polish, support, and advanced features. Vendors provide regular updates, security patches, and technical support when problems arise. User interfaces typically require less training. Advanced capabilities like automated compliance reporting, change detection with rollback, or integration with major cloud platforms justify costs for organizations where network downtime carries significant business impact.
The decision point isn't always budget-driven. A three-person IT department might find that the time saved by intuitive commercial software outweighs licensing costs. Conversely, a university with skilled student workers might leverage open-source tools effectively while building valuable experience.
Cloud-Based vs. On-Premise Solutions
Cloud-based network map generators offer quick deployment and automatic updates. You access the interface through a web browser, and the vendor handles infrastructure, backups, and scaling. These solutions work particularly well for organizations with multiple locations or remote IT staff who need access from anywhere. Subscription pricing converts capital expenses to operational expenses, simplifying budgeting.
Security considerations complicate cloud adoption for network mapping. Your network topology represents sensitive information—exactly what attackers want to understand your infrastructure. Sending this data to external servers requires trust in the vendor's security practices and compliance with your data governance policies. Healthcare organizations subject to HIPAA or defense contractors with ITAR requirements often cannot use cloud-based mapping tools.
On-premise solutions keep all data within your control. The software runs on your servers, behind your firewalls, with access controlled by your authentication systems. This approach demands more IT resources for installation, maintenance, and updates but provides complete data sovereignty. Hybrid models are emerging where the software runs on-premise but optionally synchronizes anonymized data to cloud services for analytics or vendor support.
How to Create a Network Map Step-by-Step
Start with an inventory of known devices and network segments. List your routers, switches, servers, and critical infrastructure even before selecting software. Document IP ranges, VLAN assignments, and any network segmentation already in place. This preliminary inventory helps you configure discovery tools correctly and provides validation data—if your discovery process finds significantly more or fewer devices than expected, investigation is warranted.
Select your network map tool based on the criteria discussed earlier. For initial mapping projects, consider starting with trial versions of commercial software or free tools to understand what works for your environment before committing budget. Download or provision the software and complete basic configuration: SNMP community strings for device queries, credentials for managed devices, and IP ranges to scan.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Run discovery scans during maintenance windows when possible. Discovery processes generate network traffic and device queries that might trigger security alerts or impact performance on older equipment. Start with a small network segment to verify configuration before scanning your entire infrastructure. Monitor the discovery process—most tools provide real-time feedback showing devices as they're found.
Customize the layout once initial discovery completes. Auto-generated layouts rarely match your mental model of the network. Drag devices into logical groupings. Apply labels that match your naming conventions. Color-code by function, department, or security zone. Add annotations explaining non-obvious connections or documenting planned changes. The goal is creating a map that team members can understand at a glance without requiring the creator to explain it.
Document connections with appropriate detail. Connection lines should indicate bandwidth, connection type (wired, wireless, VPN), and status (active, standby, failed). Note which connections are critical single points of failure versus redundant paths. For complex networks, create multiple map views at different detail levels—an overview for executives and detailed technical maps for engineers.
Maintain updates through scheduled automated scans and manual reviews. Configure your network map software to run discovery scans daily or weekly depending on how frequently your environment changes. Establish a review schedule where someone validates map accuracy monthly, verifying that recent changes appear correctly and removing decommissioned equipment. Treat your network map as living documentation, not a one-time project.
Common Network Mapping Mistakes to Avoid
The network map isn't just documentation—it's your first line of defense during incidents. When systems go down, you don't have time to figure out what connects to what. Teams with current, accurate network maps restore service in a fraction of the time compared to those working blind. I've seen outages extended by hours simply because nobody could quickly identify which systems depended on a failed component
— Marcus Chen
Incomplete inventories undermine mapping accuracy from the start. Teams often focus on servers and network infrastructure while ignoring IoT devices, printers, security cameras, HVAC controllers, and other embedded systems. These "invisible" devices create security risks and can cause mysterious network problems. Comprehensive discovery requires scanning all subnets including guest networks, management networks, and any isolated segments.
Ignoring security devices creates dangerous blind spots. Firewalls, intrusion detection systems, and network access control appliances often require special configuration for discovery tools to query them properly. Without these devices properly mapped, you cannot verify security zone segmentation or trace traffic flows across security boundaries. Document firewall rules and access control policies as annotations on your network maps.
Failing to update maps renders them worthless within weeks. Networks change constantly—new employees get laptops, servers get patched and rebooted, switches get reconfigured. A six-month-old network map provides false confidence that's worse than no map at all. Automated monitoring addresses this problem, but only if someone reviews alerts and investigates discrepancies between expected and actual topology.
Over-complicating visuals defeats the purpose of visualization. Some administrators try to show every detail on a single map, creating cluttered diagrams that nobody can interpret. Use hierarchical mapping instead: a high-level view showing major network segments and critical infrastructure, with drill-down maps providing detail for each segment. Match detail level to audience—executives need simplified views, engineers need comprehensive technical detail.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Neglecting documentation beyond the visual map leaves critical context missing. Why does this server connect to that network segment? What application uses this particular connection? When was this device last verified as necessary? Annotations, notes fields, and linked documentation transform simple topology diagrams into comprehensive infrastructure documentation.
Using network map tools without considering their security implications creates new vulnerabilities. Discovery tools with excessive privileges could be exploited by attackers. Storing network maps without encryption exposes your infrastructure design. Granting broad access to mapping tools gives too many people detailed knowledge of security architecture. Apply least-privilege principles: limit discovery tool permissions to what's necessary, encrypt map storage, and restrict access to personnel who genuinely need infrastructure visibility.
Comparison of Network Map Software Types
| Software Type | Best For | Key Features | Typical Cost Range | Examples |
| Free open-source tools | Small networks, budget-constrained organizations, teams with technical expertise | Basic discovery, manual layout, community support, customizable through scripting | Free (staff time required) | Nagios, Zabbix, NetXMS |
| Mid-tier commercial software | Growing businesses, departments within larger organizations, standard network environments | Automated discovery, template-based layouts, vendor support, scheduled scanning | $500–$5,000/year | Network Notepad, LANsurveyor, OpManager |
| Enterprise solutions | Large organizations, complex multi-site networks, compliance-driven industries | Advanced analytics, integration APIs, change detection, application dependency mapping | $10,000–$100,000+/year | SolarWinds, PRTG Enterprise, Cisco Prime |
| Cloud-based generators | Multi-location organizations, remote IT teams, rapid deployment needs | Browser-based access, automatic updates, collaboration features, subscription pricing | $50–$500/month | Lucidchart with network discovery, Auvik, Datadog Network Monitoring |
FAQ
Network maps transform abstract infrastructure into concrete visual documentation that accelerates troubleshooting, improves security, and enables informed planning. The investment in network map software and processes pays dividends every time an outage occurs, an audit happens, or expansion gets planned.
Success requires more than just running discovery tools once. Establish processes for regular updates, assign responsibility for map accuracy, and integrate mapping into your broader IT management practices. Choose tools that match your technical capabilities and network complexity rather than chasing features you won't use.
Start simple if you're new to network mapping. Document your core infrastructure first—routers, switches, servers, and critical connections. Expand coverage gradually to include endpoints, IoT devices, and detailed connection information. Even an incomplete map provides more value than no map at all, and you can refine accuracy over time.
Your network map should answer the fundamental question every IT team faces during incidents: what connects to what, and what depends on what? When you can answer that question instantly with visual clarity, you've achieved the core purpose of network mapping.
Related Stories
Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.