https://en.wikipedia.org/wiki/Syslog
Network Configuration Management Guide
Content
Content
Network infrastructure underpins every digital operation, yet most organizations discover their configuration weaknesses only after an outage or breach. A single misconfigured router can expose sensitive data, while an undocumented firewall change can cascade into hours of downtime. Network configuration management addresses these risks by systematically controlling how network devices are configured, changed, and documented throughout their lifecycle.
What Is Network Configuration Management
Network configuration management encompasses the processes, tools, and policies used to track, control, and document the settings of routers, switches, firewalls, load balancers, and other network infrastructure devices. Unlike network monitoring—which observes performance metrics and availability—configuration management focuses on the actual parameters that define how devices operate: access control lists, routing tables, VLAN assignments, interface settings, and security policies.
The discipline serves three core functions. First, it maintains an authoritative record of every device's current configuration state. Second, it tracks who changed what settings, when, and why. Third, it provides mechanisms to restore previous configurations when changes cause problems or fail to meet requirements.
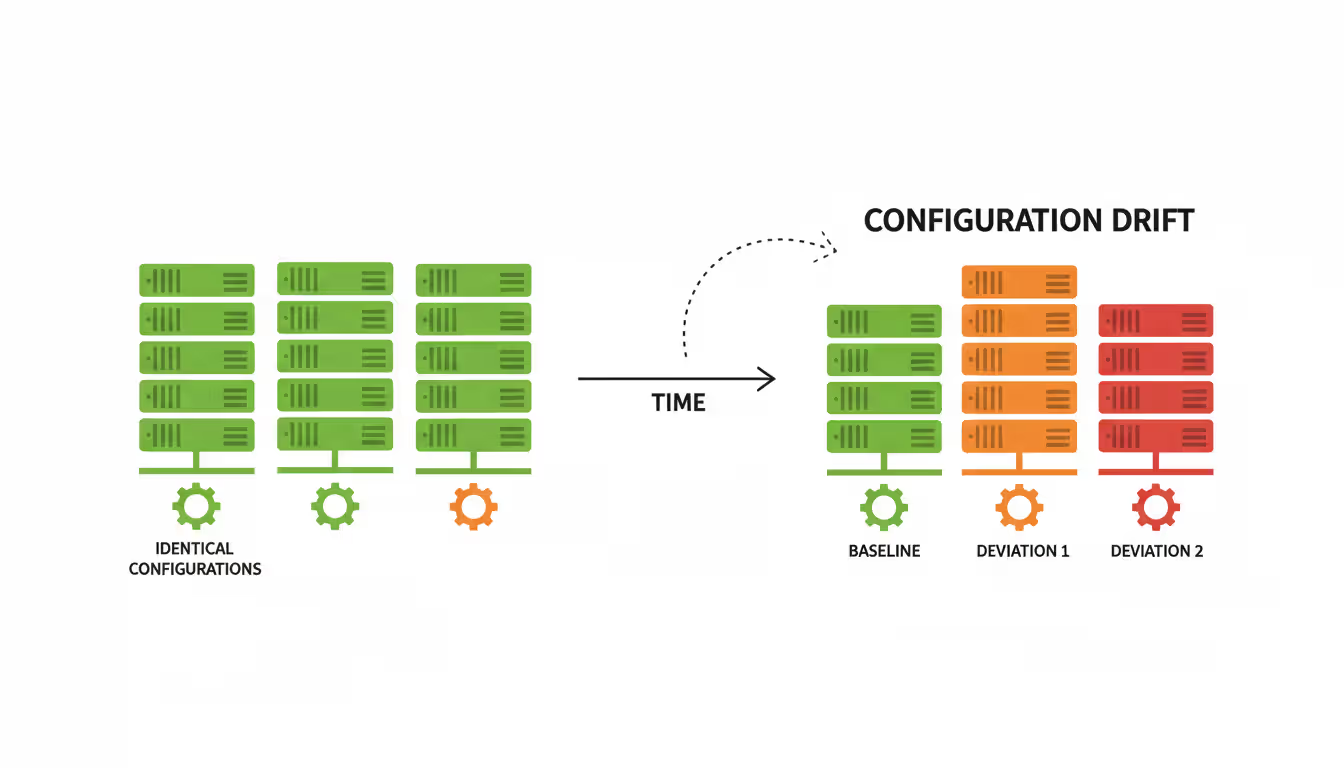
Organizations need structured configuration management because network complexity has grown exponentially. A mid-sized enterprise might operate 200+ network devices from multiple vendors, each with thousands of individual configuration parameters. Manual tracking becomes impossible at this scale. Without systematic management, configuration drift occurs—devices gradually diverge from intended standards, creating security gaps and operational inconsistencies.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
The business impact is measurable. Unplanned downtime costs enterprises an average of $9,000 per minute according to 2025 infrastructure reliability studies. Configuration errors account for roughly 60% of network outages, most resulting from unauthorized changes, typos in command-line entries, or forgotten modifications during troubleshooting sessions.
How Network Configuration Works in Practice
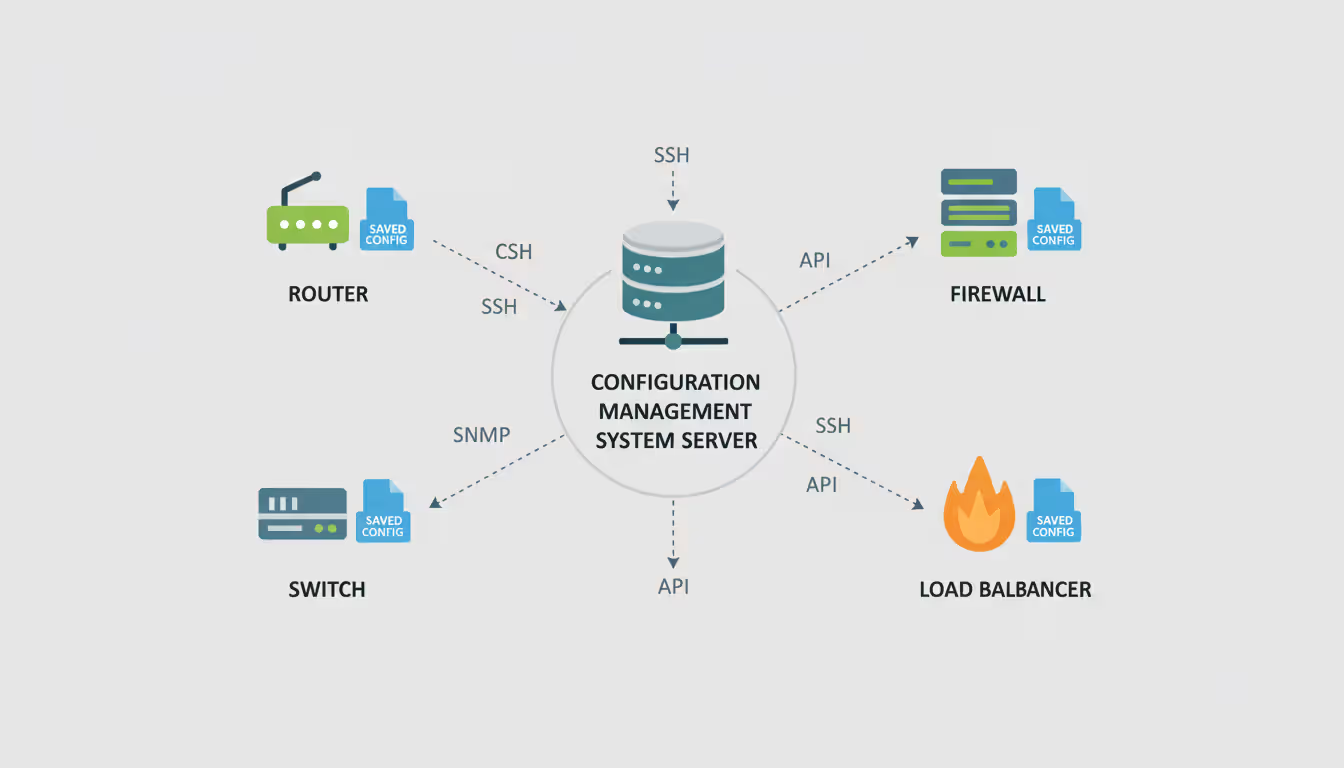
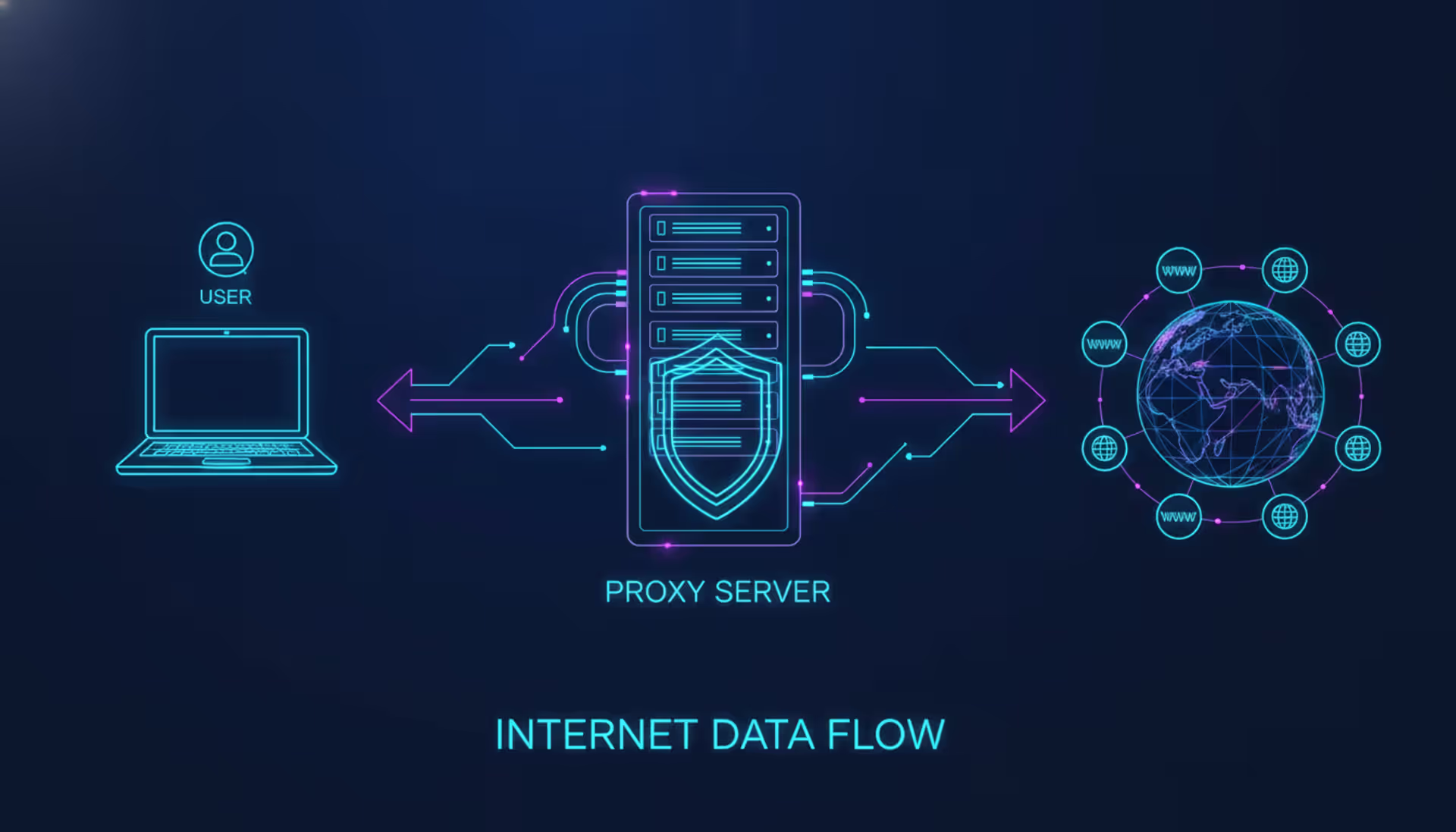
The technical workflow begins with network discovery. Configuration management systems scan IP ranges or query existing network management databases to identify active devices. Modern solutions use SNMP, SSH, API calls, or vendor-specific protocols to establish communication channels with discovered equipment.
Once devices are cataloged, the system performs initial configuration backup. This involves connecting to each device, extracting its running configuration (the active settings currently in memory) and often its startup configuration (settings loaded at boot time). The backup process repeats on a schedule—hourly for critical infrastructure, daily for standard equipment, weekly for stable edge devices.
Version control forms the backbone of effective management. Each configuration backup becomes a versioned artifact stored in a repository, similar to how software developers track code changes. When an engineer modifies a firewall rule at 2:47 PM on Tuesday, the system captures the before-and-after states, timestamps the change, and ideally records who made it and through what mechanism.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Change tracking operates through multiple methods. Agent-based systems install lightweight software on network devices to detect configuration modifications in real-time. Agentless approaches poll devices periodically, comparing current configurations against the last known good state. Some advanced platforms integrate with network device syslog streams, triggering immediate backups when configuration-change events appear in system logs.
The practical workflow for a routine change looks like this: An engineer needs to add a new VLAN to three distribution switches. Before making changes, the management system automatically backs up current configurations. The engineer applies changes through the management platform or directly on devices. Within minutes (or seconds, depending on detection method), the system identifies the configuration differences, archives the new versions, and generates a change report highlighting exactly what parameters were modified. If the change causes problems, the engineer can revert to the previous version with a few clicks rather than manually reconstructing settings from memory or scattered documentation.
Network Configuration Software and Tools
The solution landscape divides into open-source frameworks and commercial platforms, each with distinct trade-offs. Open-source tools like RANCID (Really Awesome New Cisco confIg Differ) and Oxidized provide basic backup and version control functionality at no licensing cost. These work well for organizations with strong in-house scripting capabilities and homogeneous network environments. The limitation: they require significant customization, offer minimal user interfaces, and provide limited support for change automation or compliance reporting.
Commercial platforms—including SolarWinds Network Configuration Manager, ManageEngine Network Configuration Manager, and Auvik—deliver comprehensive feature sets with vendor support. These solutions typically include web-based dashboards, automated compliance scanning, change approval workflows, and pre-built integrations with ticketing systems. The cost ranges from $2,000 to $50,000+ annually depending on device count and feature tier.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Key features to evaluate when selecting software include multi-vendor support (can it manage Cisco, Juniper, Palo Alto, Arista, and other equipment in your environment?), backup frequency options, change detection speed, rollback mechanisms, role-based access controls, and compliance reporting capabilities. Less obvious but critical factors include configuration search functionality (can you quickly find all devices with a specific ACL entry?) and configuration template support for standardizing new device deployments.
Cloud-based versus on-premises deployment represents another decision point. Cloud solutions eliminate infrastructure management overhead and enable remote access but require trust in the vendor's security controls since configuration files contain sensitive network topology information. On-premises deployments provide complete control but demand dedicated server resources and maintenance effort.
Integration capabilities matter for mature operations. The configuration management system should connect with change management platforms (ServiceNow, Jira), SIEM solutions for security event correlation, and orchestration tools for automated remediation workflows.
Network Configuration Automation Benefits and Use Cases
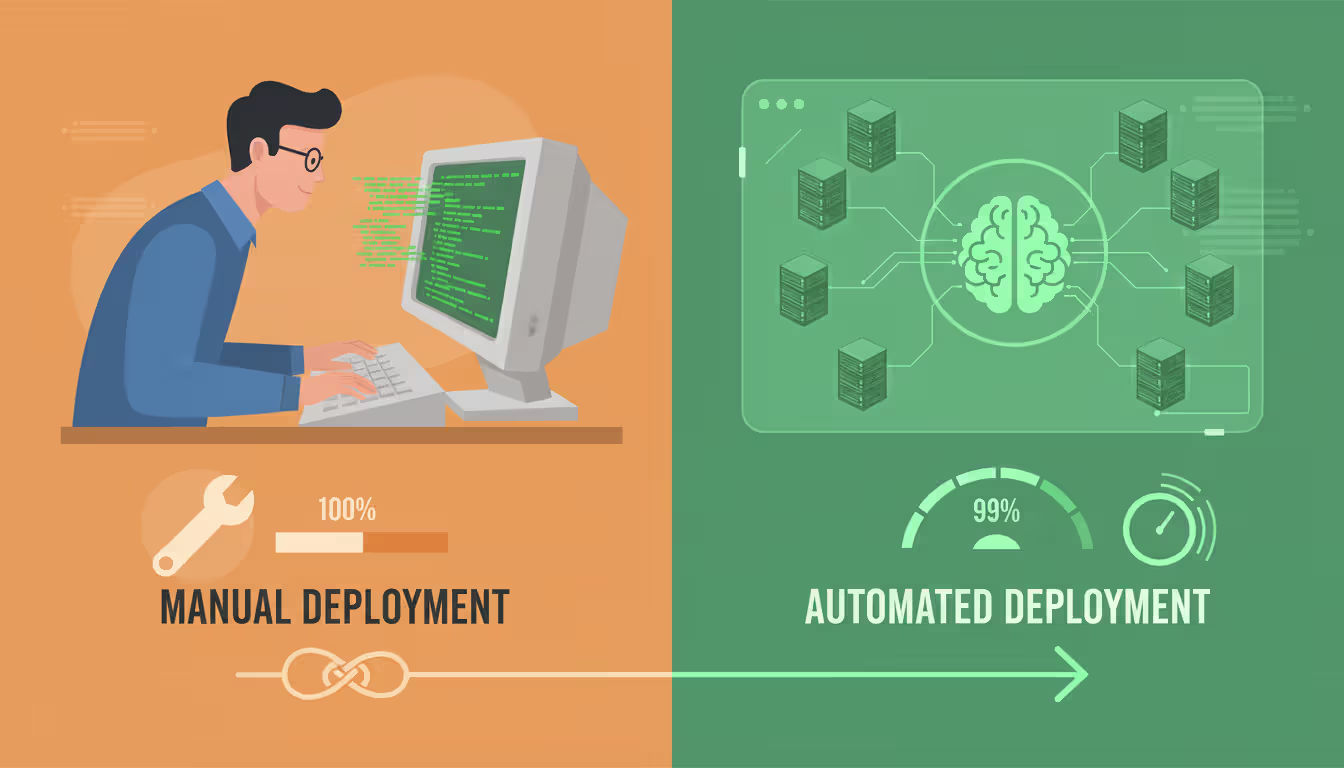
Automation transforms configuration management from a reactive documentation exercise into a proactive control mechanism. Time savings are immediate: tasks that consumed 30 minutes per device when performed manually—connect via SSH, enter commands, save output, compare against documentation—complete in seconds when automated across hundreds of devices simultaneously.
Error reduction provides even greater value. Human operators make typos, forget syntax requirements, and occasionally apply changes to the wrong device. Automated systems execute changes exactly as programmed, every time. A pharmaceutical company reduced configuration-related incidents by 73% within six months of implementing automated change deployment, according to a 2025 case study.
Compliance support becomes manageable through automation. Rather than manually auditing device configurations against security baselines before each audit, automated systems continuously scan for deviations. When a router configuration drifts from the approved template—perhaps an engineer disabled logging during troubleshooting and forgot to re-enable it—the system flags the violation within hours instead of months.
Real-world scenarios demonstrate practical applications. A retail chain with 300 branch locations needs to update firewall rules across all sites to block a newly discovered threat. Manual implementation would require days and carry high error risk. Automated deployment pushes the change to all devices within two hours, with automatic verification that changes applied correctly and rollback triggers if any device becomes unreachable post-change.
Another example: A healthcare network must prove to auditors that no unauthorized configuration changes occurred in systems handling protected health information. Without automation, this requires manually comparing configuration files across multiple backup dates for dozens of devices. Automated change tracking provides a complete audit trail with timestamps, change content, and user attribution—generated in minutes rather than days of manual effort.
Standardization across environments becomes achievable. Configuration templates define approved baseline settings for device roles (data center core switch, branch office router, DMZ firewall). When deploying new equipment, engineers apply the appropriate template rather than building configurations from scratch, ensuring consistency and reducing deployment time from hours to minutes.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Network Configuration for CUI and Compliance Requirements
Organizations handling Controlled Unclassified Information face specific network configuration requirements under NIST SP 800-171 and the Cybersecurity Maturity Model Certification framework. These standards mandate documented configuration management processes, baseline configurations for information systems, and change control procedures.
NIST 800-171 requirement 3.4.2 specifically addresses establishing and enforcing security configuration settings. For network infrastructure, this translates to documented baseline configurations that disable unnecessary services, implement approved encryption protocols, enforce authentication requirements, and configure logging to security standards. Configuration management systems provide the mechanism to define these baselines, detect deviations, and maintain compliance evidence.
CMMC Level 2—required for most defense contractors by late 2025—demands that organizations not only establish configuration baselines but also track, review, and approve configuration changes. This requires formal change management workflows where proposed modifications undergo security review before implementation, and all changes are documented with business justification.
Practical implementation for CUI environments involves several technical controls. First, configuration baselines must explicitly address NIST security requirements: disabling SNMP v1/v2 in favor of v3 with encryption, enforcing SSH instead of Telnet, configuring session timeouts, and enabling comprehensive logging. Second, the configuration management system itself must be secured—stored configurations contain network topology details and security settings that adversaries could exploit. Access controls, encryption at rest, and audit logging for the management platform become critical.
Third, change detection must be immediate rather than periodic. A daily backup schedule means unauthorized changes could persist for 24 hours before detection. For CUI environments, real-time change detection provides faster response to potential security incidents.
Configuration standards for controlled environments typically prohibit certain settings: default administrative passwords, unnecessary open ports, unauthenticated management protocols, and weak encryption ciphers. Automated compliance scanning continuously verifies these prohibitions remain enforced. When a device fails compliance checks, automated workflows can trigger remediation: alert security teams, create incident tickets, or in some implementations, automatically revert the non-compliant configuration.
Documentation requirements are substantial. Auditors expect to see approved baseline configurations, change approval records, evidence that implemented configurations match approved baselines, and procedures for emergency changes. Configuration management platforms generate most of this documentation automatically, transforming compliance from a manual documentation burden into an automated reporting function.
Network Configuration and Change Management Best Practices
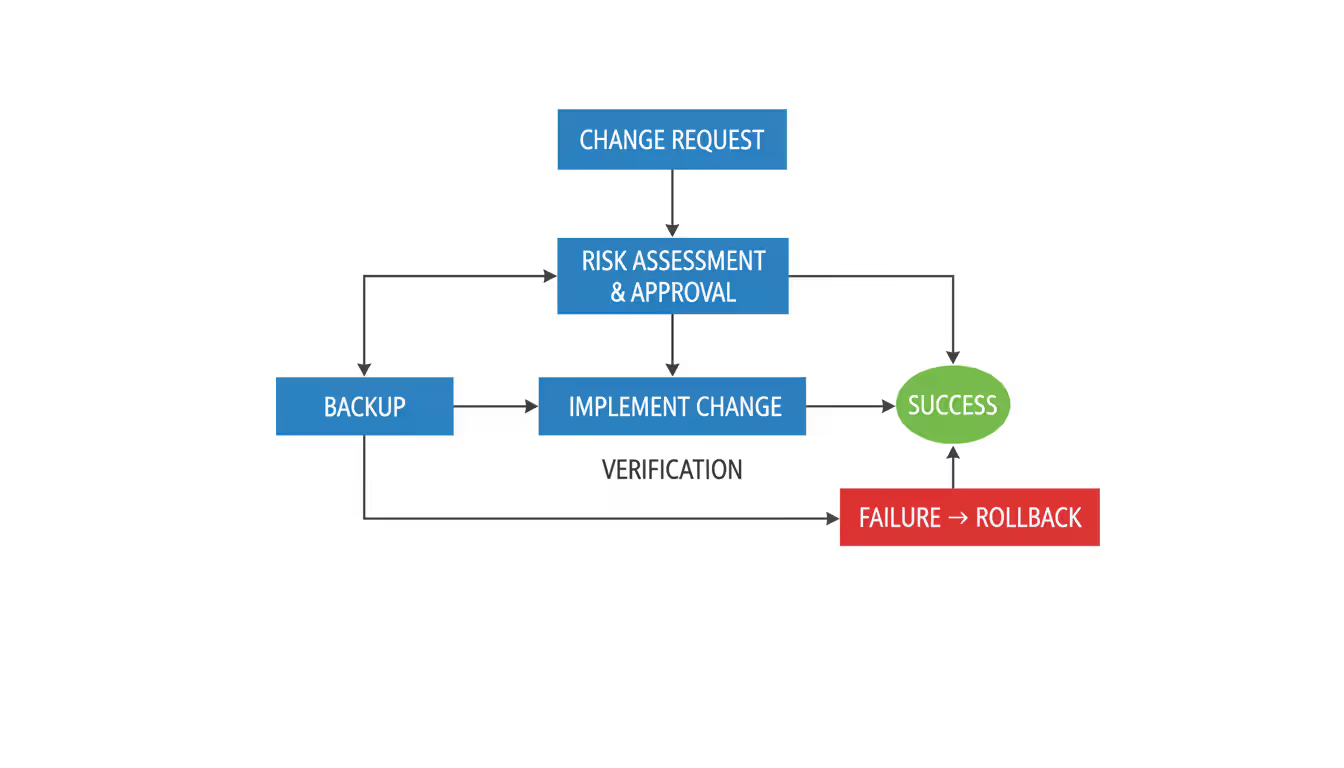
Effective change management begins before modifications are made. Change approval workflows should require documented business justification, risk assessment, and technical review for non-emergency changes. The workflow complexity should match change risk: adding a single static route might need only supervisor approval, while modifying firewall rules for production database servers should require security team review and change advisory board approval.
Pre-change backups are non-negotiable. Immediately before applying modifications, the system should capture current configurations. This creates a known-good restoration point if changes cause problems. Equally important: verify the backup completed successfully before proceeding. An empty backup file provides no recovery path.
Testing procedures prevent most change-related incidents. For significant modifications, implement changes in test environments first, validate expected functionality, and verify no unintended side effects occurred. When test environments aren't available or practical, schedule changes during maintenance windows with technical staff available to address issues.
Rollback procedures must be defined before changes begin, not improvised during an outage. Document exactly how to revert changes: which configuration version to restore, what commands to execute, how to verify successful rollback. Time pressure during incidents leads to mistakes; pre-defined procedures reduce that risk.
Documentation requirements extend beyond what changed to include why changes were made, who approved them, what testing occurred, and what rollback procedures exist. Future engineers troubleshooting issues need this context. Six months later, when investigating a performance problem, understanding that a routing change was implemented to work around a hardware issue provides critical troubleshooting context.
Audit trails must be tamper-evident and comprehensive. Every configuration modification should generate an immutable record including timestamp, user identity, change content, and ideally the mechanism used (management platform, direct CLI access, API call). These trails support security investigations, compliance audits, and operational troubleshooting.
Peer review adds a quality control layer. Before implementing complex changes, have another engineer review the planned modifications. Fresh eyes catch errors the change author missed: wrong IP addresses, incorrect subnet masks, ACL entries that are too permissive.
Change windows establish predictable patterns. Rather than allowing changes anytime, designate specific maintenance windows for routine modifications. This concentrates risk into periods when support staff are prepared and users expect potential disruptions, rather than introducing changes during business-critical hours.
Emergency change procedures must exist but should be tightly controlled. True emergencies—active security breaches, complete service outages—justify bypassing normal approval processes. However, emergency procedures should still require post-incident documentation and retroactive review to ensure the emergency classification was appropriate.
Common Network Configuration Management Mistakes
Organizations that treat network configuration management as an optional documentation exercise rather than a core security control are fundamentally misunderstanding modern threat landscapes.We've analyzed breach post-mortems across 200+ incidents, and unauthorized or poorly controlled configuration changes appear in the attack chain for approximately 40% of successful network intrusions. Automated configuration management with real-time change detection and approval workflows isn't a luxury—it's a foundational security requirement that directly reduces both attack surface and incident response time
— Marcus Chen
The most damaging mistake is treating configuration management as a backup tool rather than a change control system. Organizations implement automated backups, store configuration files, but never review changes or enforce approval workflows. This provides disaster recovery capability but misses the primary value: preventing problems through controlled change processes.
Security gaps emerge when configuration files are stored without adequate protection. These files contain SNMP community strings, enable passwords, VPN pre-shared keys, and network topology details. Storing them in unencrypted file shares or emailing them through unencrypted channels creates significant security exposures. Configuration repositories require encryption, access controls, and audit logging comparable to other sensitive data stores.
Lack of automation limits effectiveness and creates operational bottlenecks. Organizations that manually back up configurations struggle to maintain consistent schedules as device counts grow. Manual processes also can't provide real-time change detection—by the time weekly backups reveal an unauthorized change, the modification has been active for days.
Poor documentation practices undermine the entire discipline. Configuration files without context—no notes about why settings exist, what dependencies exist, or what changes were made when—provide limited value during troubleshooting or audits. Every non-standard configuration element should include comments explaining its purpose.
Inadequate testing before production deployment causes preventable outages. Engineers sometimes apply changes directly to production devices without validation, assuming configurations will work as intended. Complex changes—routing protocol modifications, firewall policy restructuring, VLAN redesigns—should be tested in lab environments or pilot deployments before broad rollout.
Scope creep during change implementation introduces risk. An engineer scheduled to update ACLs on three firewalls notices an unrelated configuration inconsistency and decides to fix it simultaneously. Now two unrelated changes are deployed together, making it difficult to isolate which modification caused problems if issues arise.
Ignoring vendor-specific configuration nuances creates problems in multi-vendor environments. A configuration management approach that works well for Cisco equipment might not translate directly to Juniper, Palo Alto, or Fortinet devices. Syntax differences, feature variations, and vendor-specific best practices require tailored approaches.
Insufficient access controls on configuration management platforms create security and compliance risks. If all engineers have full rights to view, modify, and deploy configurations across the entire network, the principle of least privilege is violated. Role-based access should limit configuration visibility and modification rights based on job responsibilities.
Failure to integrate configuration management with broader IT processes creates information silos. When the configuration management system operates independently from change management platforms, incident management systems, and security tools, valuable correlation opportunities are lost. A firewall configuration change should automatically link to the change ticket that authorized it, appear in the timeline when investigating subsequent incidents, and trigger security scans to verify compliance.
Comparison of Network Configuration Management Approaches
| Approach | Time Required | Error Rate | Scalability | Compliance Support | Cost |
| Manual | High (hours per week for small networks) | High (15-20% of changes contain errors) | Poor (breaks down beyond ~50 devices) | Minimal (requires extensive manual documentation) | Low initial cost, high labor cost |
| Semi-Automated | Medium (automated backups, manual change control) | Medium (5-10% error rate) | Moderate (handles 100-300 devices) | Moderate (automated reporting with manual review) | Medium ($5K-$25K annually) |
| Fully Automated | Low (minutes per week for routine operations) | Low (1-3% error rate) | High (scales to thousands of devices) | High (continuous compliance monitoring and automated reporting) | Higher initial cost ($25K-$100K+ annually), lower operational cost |
Frequently Asked Questions
Network configuration management has evolved from a recommended practice to an operational necessity. The combination of growing network complexity, increasing security threats, and stringent compliance requirements makes systematic configuration control indispensable for organizations of all sizes.
Effective implementation requires more than just deploying software. Organizations must establish clear change control processes, define configuration standards appropriate to their security requirements, implement automation where it provides value, and integrate configuration management with broader IT governance frameworks.
The investment pays dividends through reduced downtime, faster incident response, improved security posture, and streamlined compliance processes. As networks continue to grow in complexity and security stakes rise, organizations that master configuration management gain significant operational and security advantages over those that treat it as an afterthought.
Starting points for organizations new to formal configuration management: document current configurations, implement automated backups, establish basic change approval workflows, and gradually expand automation as processes mature. For organizations with existing programs, focus on integration with security tools, real-time change detection, and automated compliance validation to maximize value from configuration management investments.
Related Stories
Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.