
Modern data center server racks with glowing blue network connection lines rising upward and transforming into cloud structures floating above the infrastructure
What Is Cloud Networking?
Remember when adding a new office location meant six months of vendor meetings, equipment orders, and circuit installations? Those days are gone. Modern businesses spin up complete network infrastructure in different continents faster than it used to take to provision a single MPLS circuit.
That's cloud networking in action—and it's not just faster. It completely changes the economics of IT infrastructure.
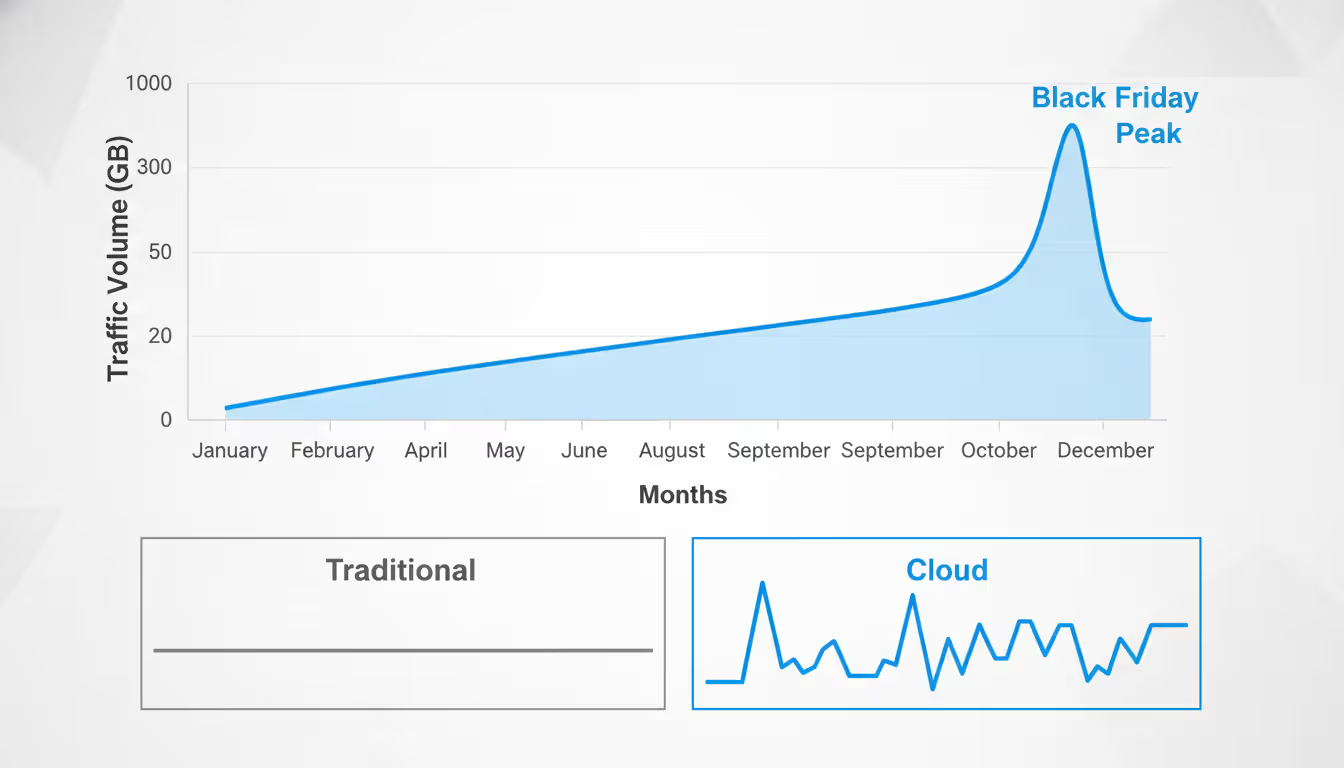
Companies no longer sink $50,000 into routers that sit at 30% utilization most of the year. Instead, they're paying for exactly what they use, when they use it. A retailer might consume 2 Gbps of bandwidth in July but 40 Gbps during Black Friday, paying proportionally for each. Try doing that with owned hardware.
But here's what nobody tells you upfront: cloud networking isn't "traditional networking, just hosted somewhere else." The architectural patterns, cost models, and troubleshooting approaches differ so radically that experienced network engineers often struggle during their first cloud projects. I've watched teams with decades of Cisco experience make $20,000 mistakes in their first month on AWS because they assumed data center networking principles would translate directly.
They don't. And understanding why matters if you're responsible for infrastructure decisions.
Cloud Networking Definition and Core Concepts
What is cloud networking? Strip away the marketing language, and here's what you're actually getting: network infrastructure—routing, switching, load balancing, firewalls—delivered as on-demand services instead of physical equipment you own and operate.
You're not buying a router. You're renting routing capability, configured through web consoles or API calls, billed hourly.
The cloud networking definition breaks down into a few key shifts from traditional approaches. Physical network devices become virtual constructs. You'll "create" a router, but there's no specific hardware box doing that routing—it's software running distributed across the cloud provider's infrastructure. Configuration happens through code or GUI instead of console cables and CLI. And most critically, you're sharing physical infrastructure with other customers while maintaining logical isolation through virtualization.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Here's a practical comparison: Building a traditional three-site WAN typically meant purchasing routers for each location ($5,000-$15,000 per site), ordering MPLS circuits from carriers ($800-$2,500 monthly per site), waiting 45-90 days for installation, then maintaining it all yourself. The upfront investment alone might hit $50,000 before seeing any value.
Cloud networking flips this completely. Create three virtual networks in different AWS regions—takes 10 minutes. Connect them via VPN or AWS Transit Gateway—another 30 minutes. Total upfront cost: $0. Monthly cost: maybe $200-$500 depending on data transfer volumes. Cancel anytime without penalties.
The architectural differences run deeper than deployment speed. Traditional networks use predetermined paths—your New York office routes to Chicago through specific physical links regardless of current conditions. Cloud networks route dynamically based on real-time metrics. Traffic from your application in AWS's Virginia region might flow through different paths depending on whether the user connects from Boston versus Bangkok, optimizing for latency automatically.
Static vs. dynamic. That distinction shapes everything from capacity planning to disaster recovery strategies.
Traditional network design provisions for peak capacity even during valleys. You buy enough bandwidth to handle your busiest hour, even though that might only occur during quarterly financial closes. The equipment sits underutilized 95% of the time. Cloud networking scales with actual demand—you're consuming more resources during peaks and fewer during troughs, with costs tracking proportionally.
How Cloud Networking Technology Functions
Three technologies make cloud networking possible: virtualization that creates logical networks on shared hardware, software-defined controls that centralize management, and globally distributed infrastructure that delivers local presence everywhere.
Virtualization creates network isolation without physical separation. A single server might host 50 virtual machines from 10 different customers. Each VM believes it has dedicated network interfaces, but they're all sharing the same physical network card. Overlay networks use encapsulation protocols—VXLAN and GENEVE are the popular choices—to tunnel isolated traffic across shared infrastructure. Your packets get wrapped in an additional header that routes them through the cloud provider's network, then unwrapped at the destination.
It's like sending a sealed envelope (your traffic) inside another envelope (the overlay protocol) through the postal system (cloud provider's physical network).
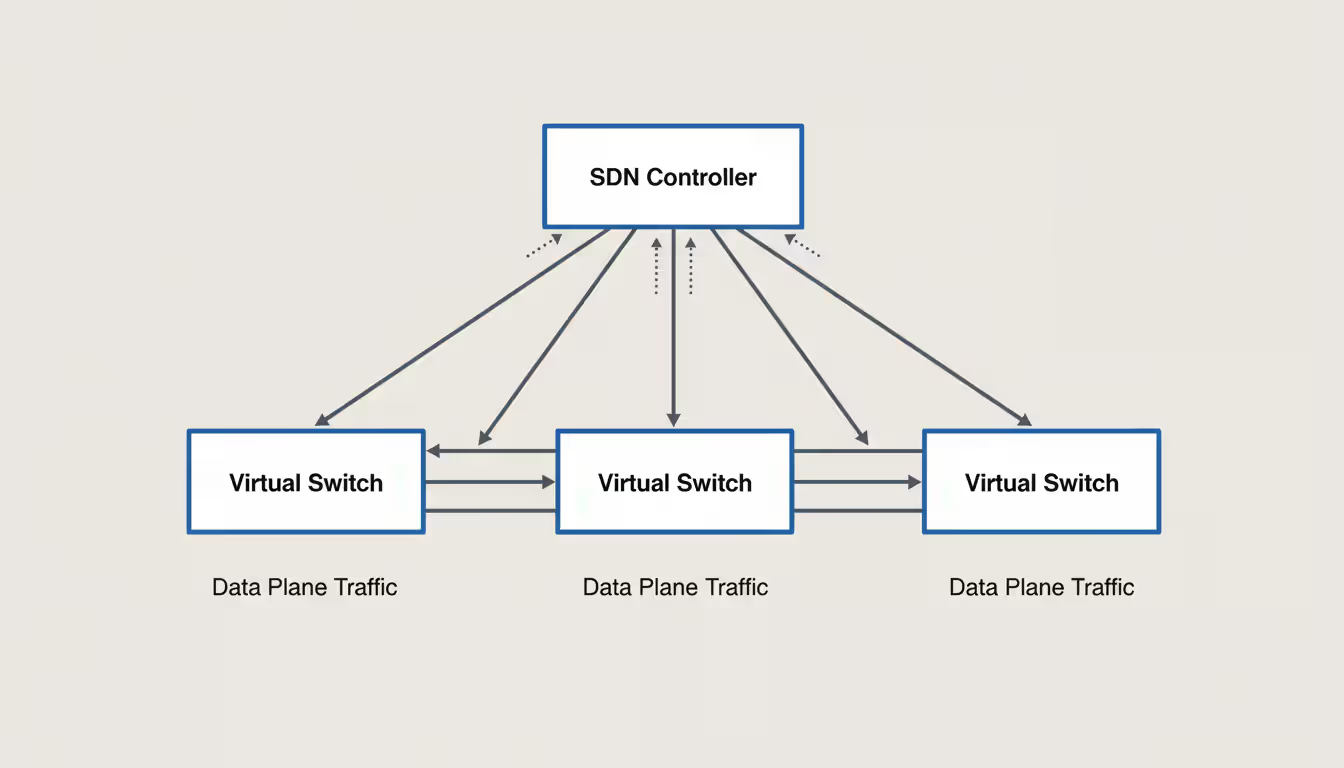
Software-defined control planes manage these virtualized networks. Traditional routers make forwarding decisions independently using protocols like BGP and OSPF. Cloud networking centralizes these decisions in controllers that program thousands of virtual switches simultaneously. When you create a new subnet in Azure, you're not manually configuring individual devices—a central controller pushes configurations to all relevant hypervisors in seconds.
This automation enables infrastructure-as-code practices. Network configurations live in Git repositories alongside application code. Changes go through code review and automated testing before deployment. A practice that would have seemed absurd in traditional networking becomes standard operational procedure in cloud environments.
Multi-cloud connectivity—connecting AWS, Azure, Google Cloud, and your data center into one cohesive network—introduces real complexity. Each provider uses different terminology, configuration methods, and underlying architectures. AWS calls them VPCs, Azure says Virtual Networks, Google Cloud also uses VPCs but implements them differently than AWS. Maintaining consistent security policies and optimal routing across this heterogeneity requires either deep expertise in each platform or third-party tools that abstract the differences (at additional cost and complexity).
Software-Defined Networking in the Cloud
SDN separates the "brains" (control plane) from the "muscle" (data plane) of networking. Traditional routers combine both—each device independently decides where packets go and physically forwards them. SDN extracts the decision-making into centralized controllers that program simple forwarding rules into distributed switches.
Why does this matter practically? Disaster recovery becomes dramatically faster.
Failing over an application from your primary data center to disaster recovery traditionally required updating DNS records, reconfiguring firewalls, adjusting load balancers, and modifying routing protocols. With human approvals and change control processes, you're looking at 2-4 hours minimum. I've seen it take eight hours for companies with complex environments.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
SDN-based cloud networks execute the same failover through policy updates pushed from controllers. The entire process—rerouting traffic, updating firewall rules, adjusting load balancers—completes in 5-10 minutes. Some organizations achieve sub-minute recovery times with proper automation.
But there's a trade-off: troubleshooting becomes exponentially harder.
When packets go missing in traditional networks, you trace hop by hop through physical devices using familiar tools—ping, traceroute, packet captures. Cloud SDN introduces multiple abstraction layers between your troubleshooting and the actual packet flow. You're dealing with virtual switches on hypervisors, overlay tunnels, the cloud provider's backbone routing (which you can't see), and software-defined firewall policies distributed across infrastructure you don't control.
Network engineers transitioning from traditional environments often struggle most with this diagnostic complexity. The mental model of "trace packet path through devices" doesn't work when there aren't discrete devices to trace through. You're troubleshooting distributed software systems as much as networks.
Isolated Environments Inside Shared Infrastructure
VPCs—Virtual Private Clouds—give you a logically separated network space within a cloud provider's shared infrastructure. Think of it as your own private data center, except you're defining IP ranges, creating subnets, and controlling routing through software rather than installing physical equipment.
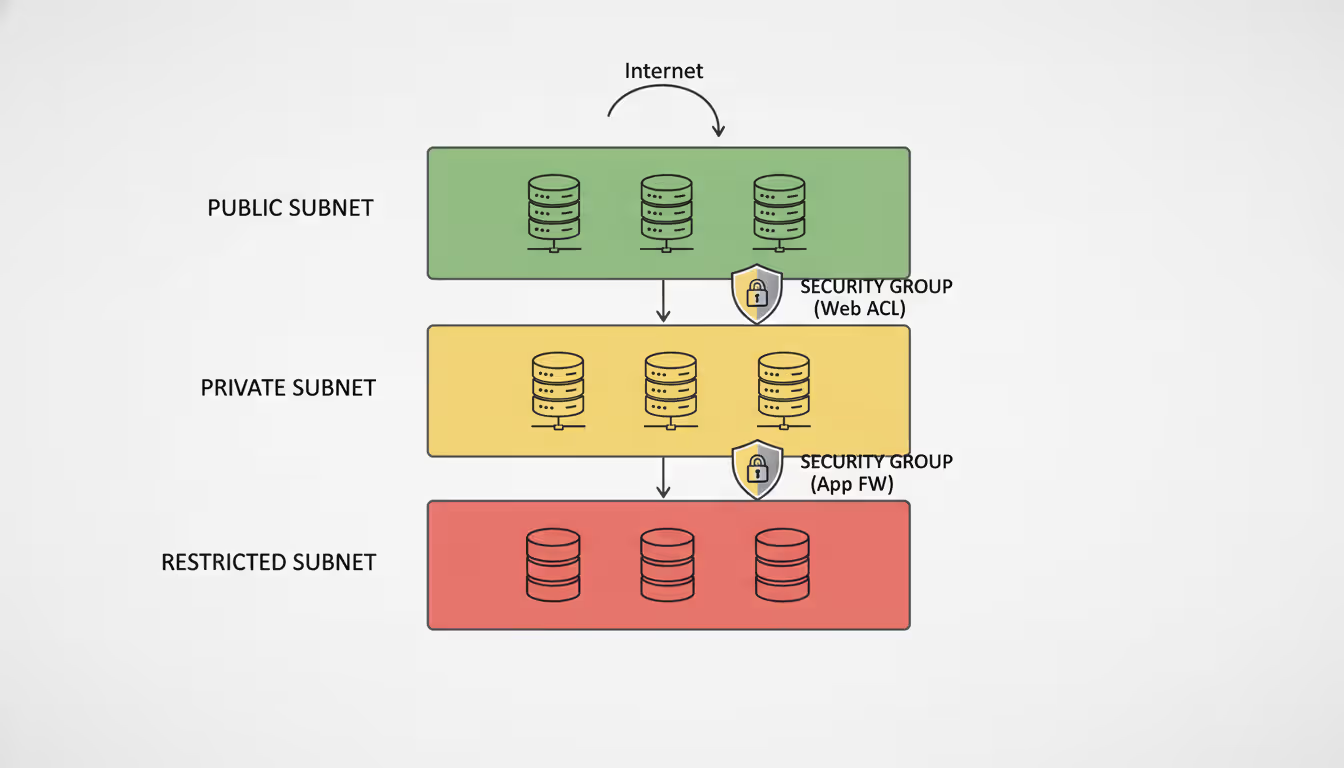
A typical three-tier web application architecture uses subnet segmentation for security. Web servers sit in public subnets with internet access. Application servers live in private subnets that can initiate outbound connections but aren't directly reachable from the internet. Database servers occupy even more restricted subnets with no internet access whatsoever—they can only receive connections from application servers.
Security groups (stateful firewalls) and network ACLs (stateless packet filters) enforce traffic rules between these tiers. This implements defense-in-depth: an attacker compromising a web server doesn't automatically gain database access because network policies block that communication path.
Microsegmentation extends this principle to individual workloads. Rather than permitting all application servers to communicate freely, microsegmentation allows only specific services to interact through defined APIs. Your payment processing service can call the inventory service, but the email service cannot. This limits lateral movement—a critical defense given that recent cloud breaches consistently involved attackers moving sideways through environments after initial compromise.
The most common mistake? Allocating subnet IP ranges without planning for growth.
I've watched organizations exhaust their VPC address space within a year by creating /20 subnets (4,096 addresses) when they only needed /24 (256 addresses). You can't easily expand VPC ranges in most cloud platforms—it requires creating new VPCs and migrating workloads. Plan for 3-5x growth in each subnet from day one, and reserve large blocks of unused space for future expansion that you haven't even imagined yet.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Types of Cloud Networking Models
Three architectures dominate: public cloud (shared infrastructure), private cloud (dedicated infrastructure), and hybrid (some combination). Each solves different problems at different price points.
Public cloud networking uses infrastructure shared among thousands of customers. Your VPC runs on the same physical servers as Netflix, Airbnb, and millions of startups. Logical isolation through virtualization keeps your traffic separated, but you're sharing underlying hardware, network switches, and fiber connections.
The economics are compelling. Spin up networks across 20 global regions without capital investment. Pay only for consumed resources. Scale capacity instantly during demand spikes. A gaming company launching a new title can provision infrastructure for 10 million players, then scale down post-launch without being stuck with owned equipment.
Startups building SaaS products almost universally choose public cloud networking. The alternative—purchasing routers, negotiating carrier contracts, leasing data center space—would consume their entire seed funding before writing a line of application code. Public cloud lets them focus resources on product development rather than infrastructure procurement.
Trade-offs exist. You're accepting less control over physical infrastructure and network paths. Latency varies based on provider backbone routing and current network conditions. Some regulated industries face compliance challenges running on shared infrastructure—though this has lessened as cloud providers achieve various certifications.
Private cloud networking dedicates infrastructure to a single organization. Either you're building it on-premises using platforms like VMware or OpenStack, or you're leasing dedicated hardware from providers like IBM Cloud Private or Oracle Cloud at Customer.
Financial services, healthcare, and government agencies often require private clouds. Regulatory frameworks sometimes mandate physical infrastructure separation. Security policies may prohibit shared tenancy. Performance requirements might need guaranteed capacity without "noisy neighbor" interference from other cloud users.
The cost model completely differs. You're paying upfront capital expenses for hardware regardless of utilization. A private cloud supporting 1,000 virtual machines costs roughly the same whether you're running 200 or 900 workloads. There's no elastic pricing—you've provisioned the capacity, you're paying for it.
Organizations choose private clouds when compliance requirements or risk tolerance outweigh economic considerations. A regional bank might determine that regulatory certainty justifies the additional expense compared to navigating shared infrastructure compliance questions.
Hybrid cloud networking connects public and private environments into unified infrastructure. Core banking systems run on private infrastructure for compliance while customer-facing mobile apps use public cloud for global reach and scalability. Data analytics workloads burst into public cloud during month-end processing but run on-premises the rest of the month.
Technical implementation gets complicated. You need consistent networking, unified identity management, and seamless workload portability across radically different environments. Tools like AWS Transit Gateway, Azure Virtual WAN, and Cisco SD-WAN provide connectivity, but implementing consistent security policies, managing data transfer costs, and maintaining operational expertise across platforms requires significant investment.
Many hybrid architectures emerge accidentally rather than through intentional design. Companies acquire competitors running different cloud platforms. Legacy systems can't easily migrate. Shadow IT purchases SaaS applications that don't integrate cleanly. Suddenly you're managing an accidental hybrid cloud that nobody planned for, struggling to connect disparate environments securely.
The reality for most mid-size and larger organizations: you'll end up with hybrid networking whether you plan for it or not. Better to architect intentionally than manage reactively.
Leading Cloud Networking Companies and Platforms
Cloud networking companies split into two categories: hyperscale providers offering integrated platforms (AWS, Azure, Google Cloud) and specialized vendors selling connectivity, security, or management tools that span platforms (Cisco, VMware, Palo Alto Networks).
Amazon Web Services (AWS) operates the largest cloud infrastructure—33 geographic regions with 105 availability zones as of 2026. That global reach matters if you're serving international customers or need disaster recovery across continents.
AWS networking services include VPC for isolated networks, Transit Gateway connecting multiple VPCs in hub-and-spoke topologies, Direct Connect providing dedicated fiber connections to AWS data centers, and Route 53 for DNS management. The breadth is AWS's strength—virtually any networking requirement has a corresponding service. The weakness? That breadth creates complexity. You'll stitch together 5-8 different services for enterprise networking architectures, each with its own configuration quirks and pricing model.
Organizations succeeding on AWS either build deep in-house expertise or partner with AWS-specialized consultants. The learning curve is steep enough that treating AWS networking casually typically leads to expensive misconfigurations.
Microsoft Azure integrates tightly with existing Microsoft infrastructure—Active Directory, Windows Server, System Center. Enterprises with significant Microsoft investments often prefer Azure because the operational model feels familiar. ExpressRoute (Azure's dedicated connection service) integrates with your corporate MPLS network in ways that feel more "enterprise networking" and less "cloud-native."
Azure Virtual Network provides VPC-equivalent functionality. Azure Virtual WAN simplifies branch office connectivity, combining SD-WAN capabilities with cloud networking. The platform excels in hybrid scenarios—extending corporate networks into cloud while maintaining consistent identity and policy management.
A Fortune 500 with 200 branch offices and heavy Microsoft infrastructure will likely find Azure's hybrid story more compelling than AWS's "cloud-first" approach.
Google Cloud Platform (GCP) differentiates through network performance. Google's private fiber network interconnects regions, often delivering 20-40% lower latency than routing across public internet. VPCs in GCP span globally by default rather than being region-specific like AWS and Azure, simplifying multi-region deployments.
GCP makes sense for workloads where network performance drives user experience—real-time gaming, video streaming, financial trading platforms. The platform's smaller market share (roughly 10% compared to AWS's 32% and Azure's 23%) means fewer third-party integrations and a smaller community for troubleshooting help.
Cisco approaches cloud from the enterprise networking angle. Cisco SD-WAN connects branch offices to cloud applications with intelligent path selection across MPLS, broadband, and LTE. Cisco Cloud ACI extends data center networking policies into AWS and Azure. Enterprises with millions invested in Cisco infrastructure often prefer extending existing architectures rather than adopting cloud-native tools.
The strategy makes sense until it doesn't—you're maintaining operational consistency but potentially missing cloud-native capabilities that could deliver better performance or lower costs.
VMware positions itself as the hybrid cloud specialist. NSX provides network virtualization and microsegmentation across VMware environments whether on-premises or in cloud. VMware Cloud on AWS and Azure VMware Solution let organizations run VMware stacks directly in public cloud, maintaining exact operational parity with on-premises environments.
This approach suits organizations wanting to "lift and shift" workloads to cloud without re-architecting applications or retraining staff. You're getting cloud benefits (elasticity, global reach) while keeping familiar operational models. The trade-off: you're paying premium prices compared to cloud-native alternatives, and you might not be taking full advantage of cloud platform capabilities.
| Provider | Key Features | Pricing Model | Best Use Case | Certification Offerings |
| AWS | Deepest service catalog, 33 regions globally, largest partner ecosystem | Pay-as-you-go, data transfer fees, committed use discounts available | Digital-native companies, applications needing global scale, developers comfortable with complexity | AWS Certified Advanced Networking - Specialty |
| Azure | Native Microsoft integration, strong hybrid capabilities, ExpressRoute for dedicated connectivity | Similar to AWS pricing, savings plans for committed usage | Microsoft-heavy enterprises, hybrid deployments, organizations using Office 365 | Azure Network Engineer Associate |
| Google Cloud | Superior backbone latency, global-by-default VPCs, sustained use discounts | Per-second billing, automatic sustained use discounts | Performance-critical applications, global services, companies valuing simplicity | Google Cloud Professional Cloud Network Engineer |
| Cisco | SD-WAN optimization, extends existing Cisco investments, enterprise-familiar approach | License plus subscription, higher upfront costs | Branch connectivity, Cisco-standardized enterprises, gradual cloud adoption | Cisco CCNP Cloud, Cisco SD-WAN specialists |
Benefits and Challenges of Cloud Networking
Cloud networking delivers real advantages—but it introduces complexities that catch organizations off-guard if they're not prepared.
Scalability means adding capacity without procurement cycles. A video platform's content goes viral—they provision additional bandwidth and launch new geographic POPs within two hours. Traditional networking would require budget approvals, vendor quotes, equipment delivery, and installation. You're looking at 8-12 weeks minimum, which is approximately forever in internet time.
During Black Friday 2025, one retail client scaled from 5 Gbps baseline to 80 Gbps peak capacity, then back down post-holiday. Their cloud networking bill reflected actual usage. Had they owned that infrastructure, they would have paid for 80 Gbps capacity year-round to handle two weeks of peak traffic.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Cost efficiency materializes when you avoid overprovisioning. Traditional networking forces buying for peak capacity that sits idle most of the time. Cloud networking bills for consumption—higher during peaks, lower during valleys.
But here's the catch: cost optimization requires active management, and it's easier to overspend in cloud than with owned infrastructure.
Data transfer charges accumulate silently. Cross-region transfers cost $0.02-$0.08 per GB depending on direction and regions involved. I've seen development teams replicate databases across regions for every test environment, generating $15,000 monthly in unnecessary data transfer charges. In traditional networking, internal data transfer was "free" (already paid for), so nobody thought about minimizing it.
Architecture for data locality. Keep communicating services in the same region whenever possible. Use content delivery networks for static assets rather than serving from origin. Design applications assuming data transfer costs money, because in cloud, it does.
Agility transforms development workflows. Developers provision complete network environments through infrastructure-as-code templates, test configurations, destroy everything, repeat. This self-service capability eliminates waiting for network team provisioning—development cycles accelerate from weeks to days.
The flip side: without governance, you'll face sprawl and runaway costs. I've audited AWS accounts with 200+ VPCs created by well-intentioned developers who didn't clean up after testing. Each consumed resources and generated costs. Implement tagging policies, automated cleanup of resources older than X days, and spend alerts before giving teams self-service access.
Security shifts responsibility rather than eliminating risk. Cloud providers secure physical infrastructure, network isolation, and the virtualization layer. You're responsible for configuring security groups, managing access controls, implementing encryption, and monitoring for threats.
This shared responsibility model confuses organizations. Executives assume "we're in the cloud now, so security is their problem." Wrong. Misconfigured security groups exposing databases caused 32% of 2025 cloud breaches. The cloud platforms were secure—customer configurations weren't.
Treat cloud networking security as equal partnership. The provider locks the data center doors and patches hypervisors. You configure who can access what and encrypt sensitive data. Neither party alone provides complete security.
Migration complexity exceeds most planning estimates. Applications designed for traditional networks make assumptions that break in cloud. Low latency? Variable in cloud. Free internal bandwidth? Metered in cloud. Static IP addresses? Dynamic in cloud. Multicast support? Often unavailable in cloud.
Legacy applications frequently require re-architecting to function optimally in cloud networks. A client spent six months preparing a "simple" SAP migration only to discover their custom add-ons relied on multicast communication that AWS VPCs don't support. They needed to rewrite portions of the application—adding unexpected cost and timeline.
Plan for the unexpected. Budget 30-40% more time and money than initial estimates for cloud migrations. The "gotchas" will get you otherwise.
Skills gaps persist despite cloud's mainstream adoption. Network engineers trained on physical infrastructure struggle with cloud-native concepts. The mental models differ enough that experience becomes a double-edged sword—veterans try to replicate familiar patterns rather than embracing cloud-native approaches.
Organizations underestimate this learning curve. They assign talented traditional network engineers to cloud projects, assuming expertise transfers directly. It doesn't. The first 6-12 months involve unlearning old patterns as much as learning new ones.
Budget time and resources for proper training. The $5,000 you spend on certifications and courses saves $50,000 in misconfigurations and do-overs.
Cloud Networking Courses and Certification Paths
Building cloud networking expertise requires combining conceptual knowledge with hands-on practice. Cloud networking courses range from vendor-neutral foundations to platform-specific deep dives, each serving different career stages.
Vendor-neutral training establishes fundamentals that transfer across platforms. CompTIA Cloud+ covers basic cloud concepts including networking, though it stays fairly high-level. The Cloud Credential Council's Professional Cloud Network Engineer certification provides deeper networking content without tying to specific vendors. These suit professionals early in cloud careers or those supporting multi-cloud environments who need broad understanding rather than platform-specific depth.
AWS networking certifications progress from foundational to advanced. AWS Certified Solutions Architect - Associate includes networking but covers AWS broadly. AWS Certified Advanced Networking - Specialty dives deep—VPC design, Transit Gateway architectures, Direct Connect configurations, hybrid DNS, network troubleshooting. This certification requires real production experience. Don't attempt it with just book learning—you'll fail.
Preparation typically takes 3-6 months including AWS training courses ($600-$2,000), hands-on labs through platforms like A Cloud Guru or Cloud Academy ($50-$100 monthly), and exam fees ($300). The investment pays off—AWS Advanced Networking certified professionals command $130,000-$180,000 salaries in the US market, often $20,000-$30,000 above non-certified peers.
Microsoft Azure offers the Azure Network Engineer Associate certification focusing on Virtual Networks, Azure Firewall, load balancing, and hybrid connectivity. The certification aligns well with enterprises using Azure for hybrid strategies. Microsoft Learn provides genuinely useful free training content (surprisingly good quality), though most candidates supplement with paid courses from Pluralsight ($29-$45 monthly subscriptions) or individual Udemy courses ($15-$100, frequently on sale).
Google Cloud Professional Cloud Network Engineer certification emphasizes GCP's unique architecture—global VPCs, Cloud Interconnect, VPC Network Peering. The certification currently has less market demand than AWS or Azure simply due to GCP's smaller market share, but certified professionals command premium salaries because of scarcity. If your organization uses GCP or you're targeting companies in that ecosystem, the investment makes sense despite smaller overall demand.
Cisco certifications adapted to cloud through CCNP Cloud and SD-WAN specializations. These suit network engineers with traditional Cisco backgrounds transitioning to cloud. Training costs align with historical Cisco certification patterns—$3,000-$5,000 for instructor-led courses plus $400 exam fees. The audience is narrower (Cisco-standardized enterprises) but valuable within that segment.
Hands-on practice matters more than watching videos. All major cloud providers offer free tiers—limited resources for experimentation without charges. Build VPCs, configure site-to-site VPNs, implement load balancing, deliberately break things and fix them. This practical experience proves invaluable during certification exams and especially during job interviews where you'll discuss real implementation challenges.
Online learning platforms democratized access. Coursera partners with cloud providers for specialization tracks ($39-$79 monthly). Udemy hosts thousands of individual courses ($10-$200, though $15 during frequent sales). LinkedIn Learning includes cloud content in subscriptions ($30-$40 monthly). Quality varies dramatically—prioritize courses updated within the past year (cloud platforms change fast) and filter by student reviews from verified purchasers.
University programs increasingly include cloud networking, though academic institutions lag industry practice by 2-3 years typically. Carnegie Mellon, MIT, and University of Washington offer cloud computing concentrations, but supplement formal education with vendor certifications and practical experience if you want employable skills immediately after graduation.
We're seeing the biggest infrastructure shift since organizations moved from mainframes to client-server architectures in the 1990s.Companies that treat cloud networking as just 'networking with someone else's routers' miss the transformation entirely and usually face painful lessons. The organizations thriving in cloud completely rethink their network architectures around cloud-native patterns—dynamic routing, consumption-based capacity, software-defined controls
— Jennifer Martinez
Frequently Asked Questions About Cloud Networking
Cloud networking represents more than a technology upgrade—it's a completely different approach to infrastructure architecture and operations. Organizations that recognize this distinction and adapt accordingly unlock meaningful advantages in agility, global reach, and cost efficiency. Those treating it as "traditional networking in someone else's data center" typically struggle with unexpected costs, security incidents, and performance issues.
Success requires understanding cloud networking's unique characteristics—software-defined everything, consumption-based economics, dynamic behavior—and designing architectures that leverage these rather than fighting them. Accept different operational patterns. Invest in developing new skills across your teams. Carefully manage the security responsibilities that shift to you under shared responsibility models.
The cloud networking market keeps evolving. Multi-cloud connectivity tools mature, making hybrid architectures more practical each year. Security capabilities integrate more tightly with network services through offerings like AWS Network Firewall and Azure Firewall. Edge computing pushes network functions closer to users, reducing latency for applications where milliseconds matter.
For IT professionals, cloud networking expertise has become essential rather than optional. Traditional networking knowledge remains foundational—TCP/IP, routing, security principles don't disappear. But cloud-specific capabilities like VPC design, hybrid connectivity architecture, and infrastructure-as-code increasingly determine career advancement opportunities and compensation levels.
Businesses evaluating cloud networking should start with specific problems rather than technology exploration. What are you actually trying to solve? Geographic expansion without capital expenditure? Handling variable workload demands? Faster deployment cycles? Clear objectives guide architectural decisions better than "let's try cloud because everyone else is."
Pilot projects in non-critical environments build organizational expertise before migrating production workloads. Start with development and test environments. Learn the cost models, security patterns, and operational differences on systems where mistakes don't impact customers. Partner with experienced cloud professionals—whether consultants or strategic hires—to avoid expensive lessons during initial implementations.
Cloud networking's trajectory points toward continued abstraction and automation. Network configurations increasingly deploy through CI/CD pipelines alongside application code. Routing policies adapt automatically to application requirements. The organizations embracing these operational shifts—rather than merely replicating legacy patterns—position themselves to capitalize on cloud networking's full potential.
The technology has matured beyond early-adopter phase. Cloud networking isn't experimental or risky when implemented thoughtfully with appropriate expertise. It's become the default infrastructure approach for new projects, with traditional networking reserved for specific scenarios requiring it (high-frequency trading, specialized industrial applications, heavily regulated environments with physical infrastructure mandates).
Whether your organization is beginning cloud adoption or optimizing existing cloud deployments, cloud networking will shape your infrastructure's capabilities, costs, and security posture for the next decade. Worth understanding deeply rather than superficially.
Related Stories

Read more
Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




