
A modern home desk with an open laptop, smartphone, and WiFi router surrounded by faintly glowing outlines of smart home devices connected by light network lines in warm evening lighting
How to See All Devices on Network?
Ever wonder what's actually connected to your WiFi right now? I checked mine last week and found 23 devices—which seemed reasonable until I realized I could only account for 18. Those five mystery devices? Turned out to be an old Kindle I'd forgotten about, two smart plugs I didn't remember buying, and unfortunately, a neighbor's laptop that had been connected for God knows how long.
Here's the thing: if you're running a network in 2026 (and you are, even if it's just your home WiFi), you need to know what's using it. Not next month. Not when something goes wrong. Now.
Why You Should Monitor Devices on Your Network
Let's talk about why this actually matters instead of just being another tech chore on your to-do list.
Security isn't abstract anymore. Last year, my friend Sarah discovered someone had been using her network for three months. They weren't just stealing bandwidth—they'd accessed her shared photo folder. Every family picture from the past five years. That's not a scare tactic; that's what happens when you don't know who's connected. Could be a neighbor who guessed your password, could be that sketchy smart lightbulb you bought on sale, could be something worse.
Your internet feels slow because something's hogging it. You're on a Zoom call, everything's fine, then suddenly you're a pixelated mess. Meanwhile, nobody's streaming Netflix, nobody's gaming. What gives? In my case, it was a security camera I'd installed two years ago, quietly uploading 4K footage 24/7 to cloud storage I wasn't even using anymore. Found it by checking what was connected. Disabled cloud upload. Problem solved.
You've got more gadgets than you think. Quick—how many devices connect to your network? If you said a number, you're probably wrong. My household has four people. Before I checked, I guessed maybe 15 devices total. The actual count? Thirty-two. Two phones each (work and personal), laptops, tablets, three game consoles, smart TV, streaming stick, Ring doorbell, six Alexa speakers (how did we get six?), two smart thermostats, four security cameras, printer, NAS drive, and an assortment of smart home stuff I barely remember installing. You can't manage what you can't see.
Using Your Router's Admin Panel to See Connected Devices
Every router keeps a list. You just need to know where to look.
Accessing Your Router Settings
First, find your router's address. On a Windows PC, hit the Windows key, type "cmd" and press enter. In that black box that appears, type ipconfig and hit enter. Scan through the text for "Default Gateway"—that's your router. Usually looks like 192.168.1.1 or 192.168.0.1, sometimes 10.0.0.1.
Mac users: click the Apple menu, go to System Preferences, click Network, pick your connection (WiFi or Ethernet), hit Advanced, then click the TCP/IP tab. The router address is right there.
Take that number and punch it into Chrome, Firefox, Safari—whatever browser you've got. You'll hit a login screen. If you've never changed these credentials (most people haven't), flip your router over and check the sticker. Look for something like "admin/admin" or "admin/password." No sticker? Google your router model plus "default password."
Pro tip: if the page won't load, try adding "http://" before the address, or try "https://" instead. Some routers are picky about which one they want.

Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Locating the Device List
Now you're in, but every router company designed their interface like they've never seen another router interface. Here's where stuff usually hides:
Netgear models: Main dashboard usually shows "Attached Devices" right away. If not, try the Advanced section. You'll see device names (when available), IP addresses, and whether they're on WiFi or plugged in via cable.
TP-Link routers: Navigate through Advanced, then Network, then DHCP Server. Or try Wireless, then Wireless Statistics. They split wired and wireless into separate lists, which is actually helpful when you're trying to figure out if something's connected via cable or not.
Linksys devices: Status menu, then Local Network, then DHCP Client Table. The newer Smart WiFi models show a visual map that's honestly pretty slick—circles and lines connecting everything like a family tree.
Google Nest WiFi or Eero mesh systems: Forget the web interface. Download their apps. Open it, tap around until you find Devices or Network. Everything shows up there.
Fair warning: this method only shows what's connected right now. Your kid's phone that disconnected when they left for school? Not listed. Also, device names can be cryptic. Instead of "Living Room TV," you might see "Generic-Android-Device-2847392" and have zero clue what that is.
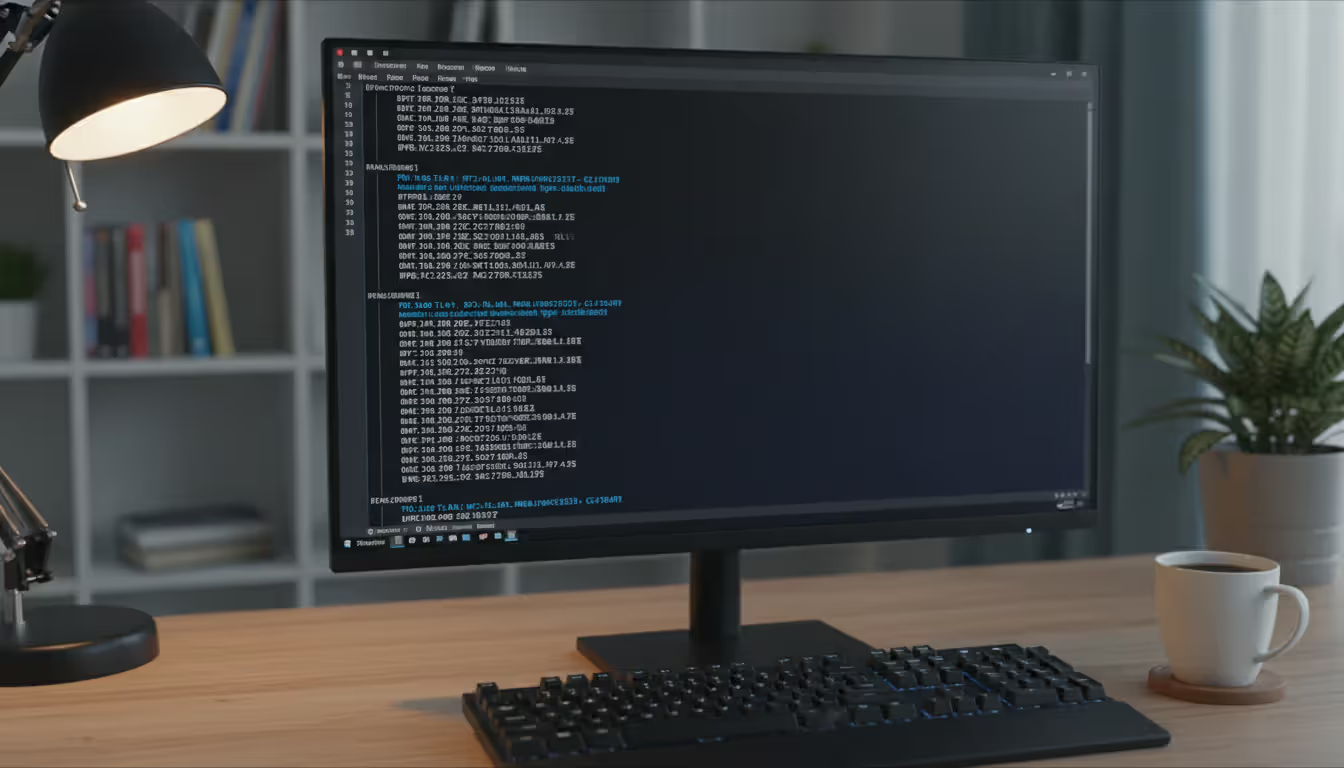
How to See All Devices on Network Using Windows Command Prompt
Sometimes you can't get into the router (forgot the password, router interface is broken, whatever). Command Prompt saves the day.
Using the ARP Command
ARP (Address Resolution Protocol) is how computers remember which devices they've talked to recently. Pull up Command Prompt again—Windows key, type "cmd," press enter—and type this:
arp -a
You get a list that looks something like:
Interface: 192.168.1.105 --- 0x4 Internet Address Physical Address Type 192.168.1.1 00-14-d1-2c-3e-4f dynamic 192.168.1.102 a4-83-e7-1a-2b-3c dynamic 192.168.1.110 dc-a6-32-4d-5e-6f dynamic
Internet Address = IP address. Physical Address = MAC address (permanent hardware ID). Type tells you if it's dynamic or static.
The catch: this only shows devices your computer has actually communicated with. If there's a smart plug in your bedroom that your computer never talks to, it won't appear here.
Using the Net View Command
Type this in Command Prompt:
net view
This lists Windows computers sharing files on your network. Used to be more useful back in the day. Now? It misses phones, tablets, smart TVs, IoT devices—pretty much everything except Windows PCs with specific sharing settings enabled. I include it here for completeness, but honestly, you'll probably get zero results unless you're in an office environment.
Want a fuller picture using just Command Prompt? Try this trick: ping your entire network range, then check ARP again. Type:
for /L %i in (1,1,254) do @ping -n 1 -w 100 192.168.1.%i | find "Reply"
Replace "192.168.1" with whatever matches your network. This pings every possible address from 192.168.1.1 through 192.168.1.254. Takes a couple minutes. When it's done, run arp -a again. Now your ARP table includes everything that responded, giving you a much more complete device list.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
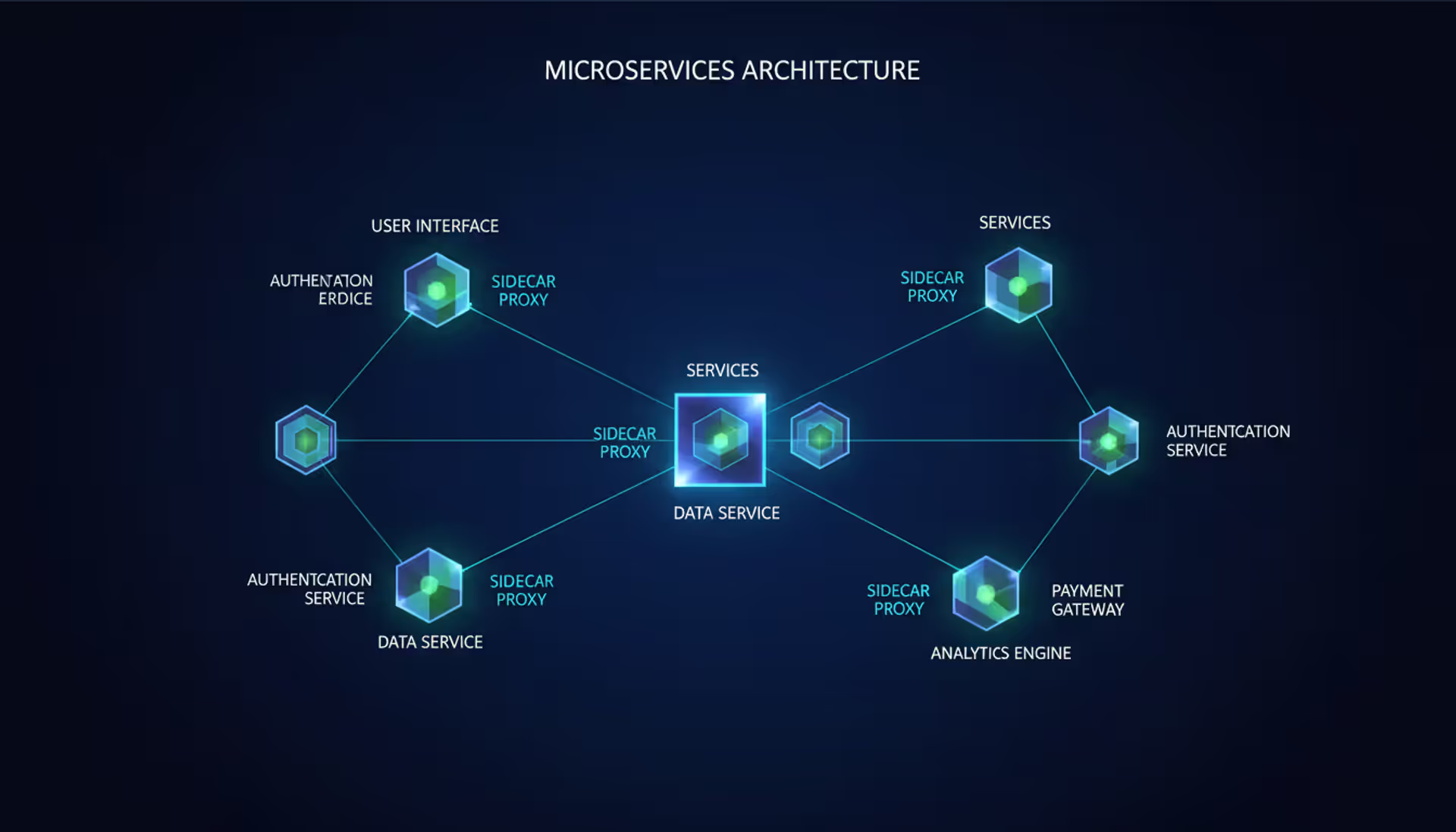
Network Scanning Software and Apps for Device Discovery
Command-line stuff not your thing? These tools do the heavy lifting for you.
Fing is what I recommend to literally everyone. Got versions for Windows, Mac, iPhone, Android—everything. Scan completes in maybe ten seconds. It not only shows you every device but actually figures out what they are based on MAC addresses. That cryptic "dc-a6-32" suddenly becomes "Raspberry Pi Foundation," and you remember you set up a Pi-hole ad blocker last year. Free version works great. Pro version ($49.99 yearly) adds security scanning and keeps history, which is nice for tracking when devices connect and disconnect. The mobile app is clutch when you're lying in bed wondering if you should get up to check something.

Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Advanced IP Scanner (Windows only, totally free) scans fast and shows shared folders, which is handy if you're trying to access files on other computers. Lets you remote control machines via RDP if you're into that. Interface looks like it's from 2010 (because it basically is), but functionality's solid. IT folks love it.
Angry IP Scanner runs on everything—Windows, Mac, Linux. It's open-source, free, and super customizable. Export results to spreadsheets, scan specific port ranges, integrate with other tools. More of a learning curve than Fing, but if you like tweaking settings, this is your jam.
Wireless Network Watcher from NirSoft is tiny, portable (no installation required), and focuses only on WiFi. It auto-refreshes every few seconds, so you can just leave it running in a corner of your screen. Looks extremely basic—think Windows 95 aesthetic—but for monitoring WiFi connections specifically, it's perfect.
SolarWinds Network Device Scanner (free up to 100 devices) brings enterprise-level scanning to home users. Identifies operating systems, shows open ports, gives you way more detail than casual users need. If you actually understand networking concepts beyond the basics, you'll appreciate what this shows you. If not, it might be overwhelming.
Personal take: Install Fing on your phone for quick checks anywhere in the house. If you want something running constantly on a PC, go with Wireless Network Watcher. Need deep technical details? Advanced IP Scanner or Angry IP Scanner.
How to See Devices on Network Using Mac or Linux
Mac and Linux users get powerful built-in tools that Windows users have to download separately.
Mac Terminal Commands
Open Terminal (Applications folder, then Utilities folder, then Terminal). Same ARP command works here:
arp -a
Output format looks slightly different than Windows but contains identical information. For active network scanning, try this:
arp -a -d && for ip in 192.168.1.{1..254}; do ping -c 1 -t 1 $ip > /dev/null 2>&1 & done; sleep 5; arp -a
This monster command clears your ARP cache, simultaneously pings every address on your network (much faster than Windows' sequential approach), waits five seconds for responses, then displays the updated cache. It's actually quite elegant once you understand what's happening.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Linux Network Discovery Tools
Linux usually includes nmap, which is legitimately the most powerful network scanner that exists. If it's not installed, grab it:
sudo apt install nmap # for Debian/Ubuntu
sudo yum install nmap # for CentOS/RHEL
Basic scan:
sudo nmap -sn 192.168.1.0/24
The -sn flag does a ping scan without checking every port, making it faster and less aggressive. Shows active hosts, MAC addresses, often identifies manufacturers.
Want more details?
sudo nmap -O 192.168.1.0/24
Adding -O enables OS detection. Nmap analyzes how each device responds to network probes and makes educated guesses about operating systems. Helps distinguish between your Windows laptop, your iPhone, and your Roku when names aren't clear.
There's also arp-scan:
sudo arp-scan --localnet
Simpler than nmap for basic device discovery. Faster scan, cleaner output, perfect when you just want to know what's connected without diving into technical details.
What Information You Can See About Each Device
Network scans reveal several identification markers that help you figure out what's what.
IP addresses show each device's current network location. Most home devices get dynamic addresses from your router's DHCP server, meaning they can change over time. Your router usually sits at .1 (like 192.168.1.1), and other devices get numbered sequentially. You can assign static addresses to important devices so they never change, which makes remote access easier.
MAC addresses are permanent hardware identifiers burned into network cards during manufacturing. Unlike IP addresses that change, MACs stay constant (unless someone deliberately spoofs them, which is rare on home networks). The first six characters identify who made it—"00:14:D1" means TRENDnet, "A4:83:E7" means Apple, "DC:A6:32" means Raspberry Pi. Lookup tools like macvendors.com translate these codes, helping you identify mystery devices.
Device names (hostnames) appear when gadgets broadcast them. Your phone might show as "Dave's iPhone," computers display whatever name you configured, IoT devices often show model numbers like "TP-Link-Smart-Plug-2947." Some devices stay silent and don't broadcast names at all, appearing blank or showing only their MAC address.
Connection type tells you wired versus wireless. Shows up in router interfaces and some scanning tools. If something's wired, it's probably stationary—desktop computer, game console, TV. Wireless means phones, tablets, laptops, or any smart home devices.
Open ports reveal running services, but you need tools like nmap to see them. Port 80 or 443 means web server, port 22 is SSH, port 3389 is Remote Desktop. Only scan ports on your own network—doing it elsewhere ranges from rude to illegal.
Modern wrinkle: privacy features mess with tracking. iPhones since iOS 14 use randomized MAC addresses that change for each network. Android 10 and up does similar stuff. These privacy measures protect you on public WiFi but make managing your home network more annoying since the same device appears as multiple "different" devices over time.
How to Identify and Remove Unknown Devices from Your Network
I've responded to hundreds of home network breaches, and the pattern is always the same—weak passwords combined with zero monitoring.The compromises I investigate rarely involve sophisticated attacks. Usually it's neighbors sharing your connection without permission, or vulnerable IoT devices nobody remembered they owned. Networks that get breached are networks where users never looked at what was connected. Regular device audits—literally just checking your list once a week—stops most attacks before they escalate into actual problems. It's the lowest-effort, highest-impact security measure anyone can implement
— Jennifer Martinez
Found something you don't recognize? Don't panic yet. Work through this systematically.
Step one: Look up the MAC address. Sites like maclookup.app translate MAC addresses into manufacturer names. See "Nest Labs" and remember you installed a thermostat last year? Mystery solved. See "Shenzhen Generic Electronics Co." and don't recognize it? Time to dig deeper.
Step two: Check the hostname if there is one. Device names often include hints. "ESP8266" means WiFi microcontroller (maybe you have a DIY project?), "BRAVIA" is Sony TV, "Ring" is probably a doorbell. Google anything you don't immediately recognize.
Step three: Compare IP addresses with timing. Check when your router assigned each address. If an unknown device appeared the same day you brought something new home, they're probably related.
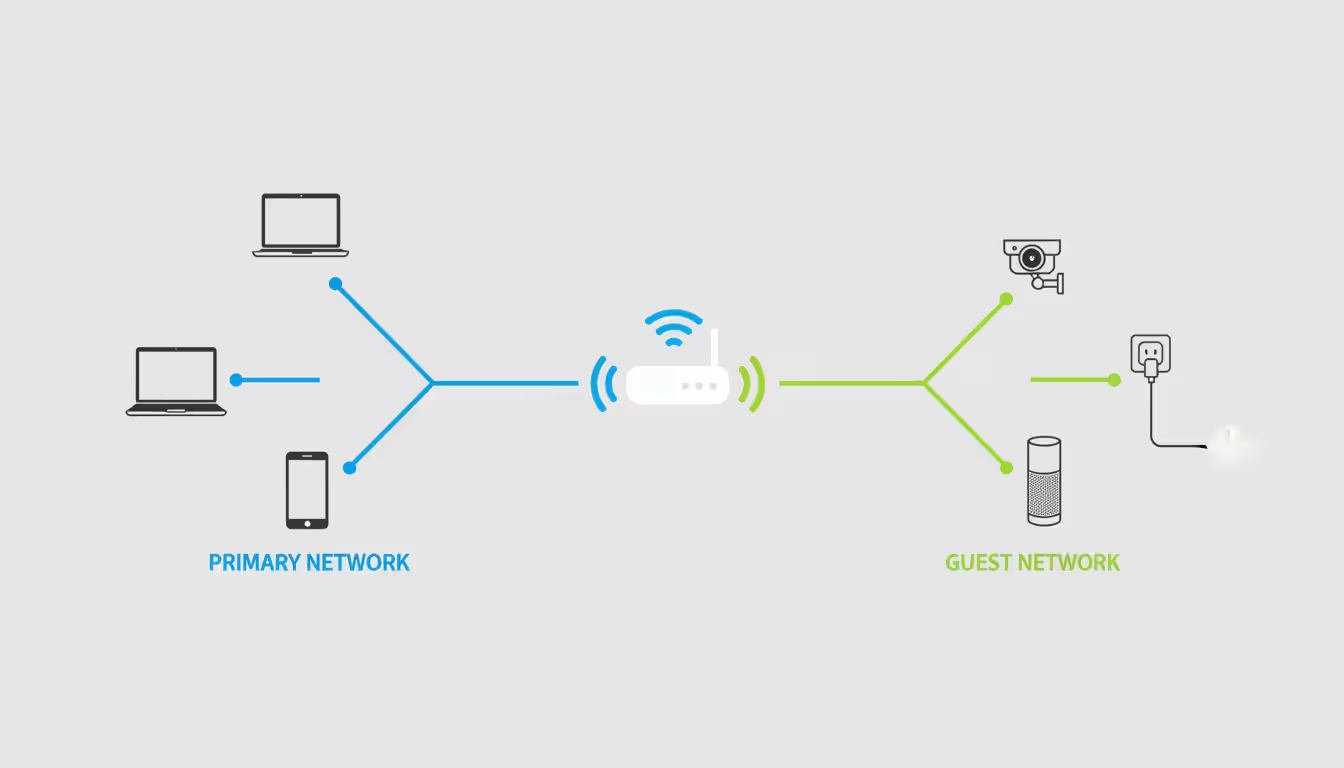
Still can't identify it? Now you act. Change your WiFi password immediately. Use WPA3 if your router supports it, WPA2 if not. Never touch WPA or WEP—they're completely broken. When you change the password, every device gets kicked off, and you'll need to reconnect legitimate devices manually. Annoying but necessary.
Turn on MAC filtering. Most routers let you create a whitelist of approved MAC addresses. Only listed devices can connect. It's not bulletproof—MAC addresses can be spoofed—but it stops casual unauthorized access.
Consider splitting your network. Most modern routers support guest networks that isolate devices from your main network. Put all your IoT stuff—smart plugs, cameras, speakers, the works—on the guest network. If one gets compromised, attackers can't pivot to your computers or phones. I moved all my smart home devices to a separate network last year, and honestly, I sleep better.
If you're really paranoid (or have good reason to be), enable logging on your router and review connection attempts. Logs timestamp when devices connect, disconnect, and fail authentication. Patterns of failed logins mean someone's trying to brute-force your password.
Comparison of Network Scanning Methods
| Scanning Method | How Hard Is It? | What You'll Discover | Works Best For | Price |
| Router Admin Panel | Beginner-friendly | IP addresses, MAC addresses, device names (when broadcast), wired vs. wireless status | Quick spot-checks, people who want simple answers | Already included with router |
| Windows CMD (ARP) | Moderate technical knowledge needed | IP addresses, MAC addresses only | Situations where router access isn't possible | Already included with Windows |
| Network Scanning Apps | Beginner-friendly | IP addresses, MAC addresses, manufacturer identification, device types, open ports, connection history | Ongoing monitoring, detailed analysis, visual interfaces | Free versions available, premium features $50 annually |
| Mac Terminal | Moderate technical knowledge needed | IP addresses, MAC addresses only | Mac users who prefer command-line tools | Already included with macOS |
| Linux Tools (nmap) | Advanced technical knowledge helpful | IP addresses, MAC addresses, operating system detection, port scanning, comprehensive network analysis | Technical troubleshooting, security auditing, professional diagnostics | Already included with most Linux distributions |
Frequently Asked Questions About Network Device Monitoring
Look, I get it—adding another tech task to your life isn't fun. But here's the reality: you've got dozens of devices connected to your network right now, and you probably can't name half of them. That's not a sustainable situation in 2026.
Start simple. Log into your router tonight and just look at the device list. Bookmark that login page so you don't have to hunt for the address next time. Check it next Sunday. Then the Sunday after that. Install Fing on your phone—it's free and takes two minutes to scan. Do that occasionally when you're bored.
The goal isn't becoming a network security expert. The goal is knowing what belongs on your network and spotting what doesn't. You've got your family's phones, laptops, tablets, game consoles, streaming devices, smart home stuff. When something new appears that you don't recognize, you'll notice immediately instead of discovering it six months later after who knows what damage.
I'm not trying to scare you. Most people never have serious security incidents. But most people also never check their networks until something goes horribly wrong. The fifteen minutes you invest learning these tools and the five minutes weekly for monitoring prevent hours of frustration and potential security breaches.
You lock your doors. You probably have a password on your phone. This is the same category of basic precaution—not paranoia, just sensible self-protection.
Related Stories

Read more
Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




