
Modern server room with network racks and glowing LED indicators, laptop displaying automation interface in foreground, blue and purple ambient lighting
Network Automation Guide
Content
Content
Here's something most network engineers won't admit publicly: they're drowning in busywork. A typical week? Forty percent goes to mind-numbing repetitive tasks. Configuring the same settings on switch after switch. Updating firmware manually. Checking compliance boxes. Troubleshooting the same connectivity problems that popped up last month.
This isn't just inefficient—it's actively dangerous. Manual processes breed errors. A single typo in a router configuration can take down an entire branch office. Inconsistent security policies across devices create vulnerabilities. And while engineers are stuck in the weeds doing grunt work, strategic projects that could actually transform the business sit in the backlog gathering dust.
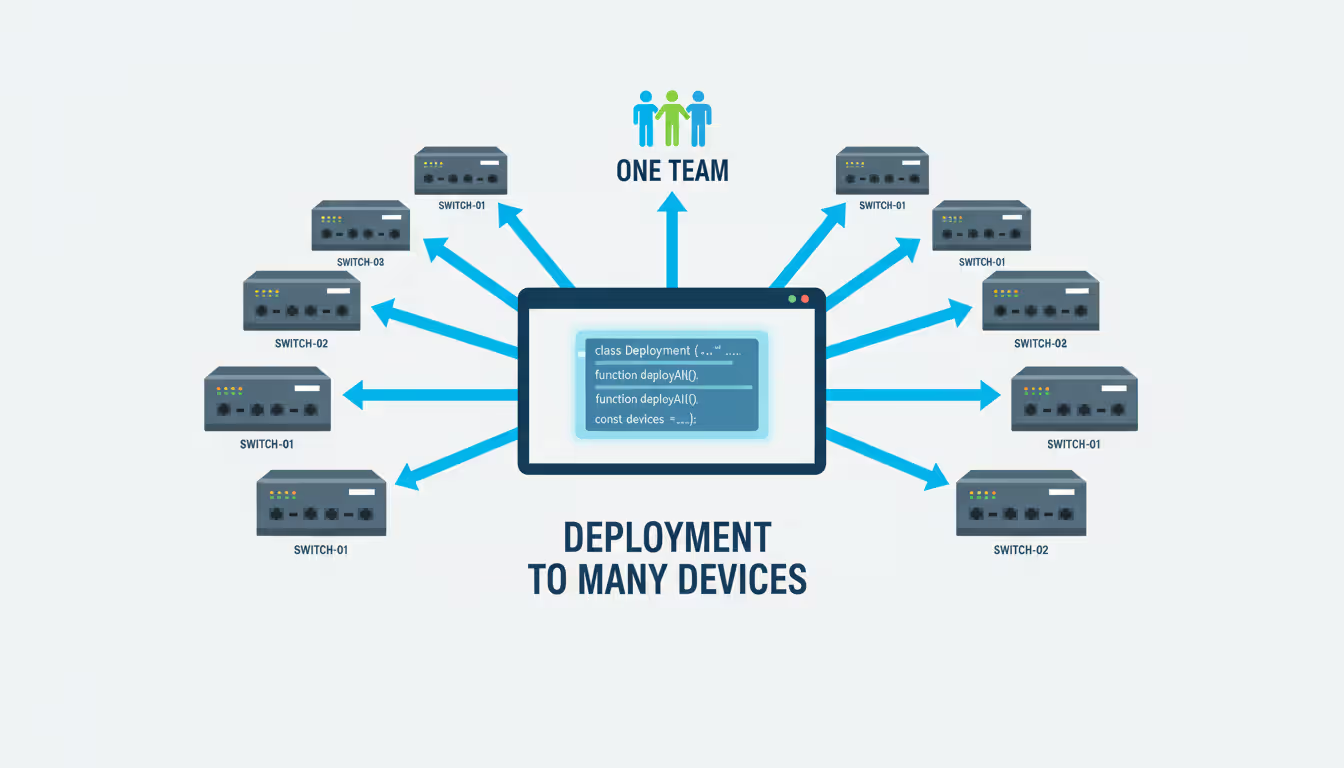
Network automation flips this script. Instead of touching every device individually, you define what the network should look like and let software handle the implementation. Need to update NTP servers on 200 switches? Write it once, deploy everywhere. Same configuration every time, documented automatically, rolled out in minutes instead of weeks.
Since 2024, adoption has exploded. Hybrid cloud environments demand it. The relentless growth in network complexity requires it. And frankly, there aren't enough skilled network professionals to do everything manually anymore. Leading IT teams now manage infrastructure the same way developers write software—version control, automated testing, continuous delivery.
What Is Network Automation and How Does It Work
At its core, network automation means using software to handle network management tasks without someone babysitting the process. Rather than SSH-ing into routers and switches to type commands one by one, you write instructions that interact with devices programmatically.
The fundamental shift is from imperative to declarative thinking. You stop telling the network "run this command, then this command, then check that output." Instead, you declare "VLAN 100 should exist on these ten switches with these exact parameters." The automation system figures out what commands to run, in what order, and handles the edge cases.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Here's how a typical automation workflow actually plays out:
First, the system catalogs your environment—every router, switch, firewall, and load balancer, along with their current state and what management protocols they support. Then you create instructions (scripts, playbooks, whatever format your tool uses) describing changes you want. The automation platform connects to devices using SSH, APIs, NETCONF, or similar protocols and makes those changes happen. After implementation, validation checks confirm everything worked correctly. Finally, detailed logs capture exactly what changed, when it happened, and who triggered it.
Under the hood, several technologies make this possible. APIs let software talk to network devices in structured ways. Modern protocols like NETCONF, RESTCONF, and gNMI enable programmatic configuration. Data formats like YAML and JSON represent network configurations in ways both humans and machines can understand easily.
Now, people constantly mix up automation and orchestration, so let's clarify. Automation tackles individual tasks: backup a config file, apply an access list, collect performance stats. These are discrete actions with clear boundaries. Orchestration strings together multiple automated tasks into sophisticated workflows. Provisioning a new application environment might orchestrate network automation (create VLANs), security automation (update firewall rules), and verification automation (test connectivity)—all sequenced correctly with proper error handling at each step.
Network automation isn't about replacing network engineers—it's about amplifying their capabilities. Organizations that embrace automation see 60-70% reductions in configuration errors and can provision new services in minutes instead of weeks
— Rachel Martinez
Common Network Automation Use Cases
Most organizations start their automation journey by tackling repetitive tasks that deliver obvious value quickly.
Configuration management is usually the first win. Teams store approved configurations as code in Git or similar version control systems. When organizational standards change—maybe updating DNS servers, adjusting SNMP settings, or tightening security policies—you modify the template once and push it to hundreds of devices simultaneously. Need to roll back a problematic change? Revert to yesterday's configuration version. One command, done.
Compliance monitoring runs continuous validation that devices match security policies and operational requirements. Automated checks scan configurations regularly, looking for disabled unnecessary services, correct ACLs, approved routing protocols, proper logging configuration. When something drifts—maybe someone made an unauthorized manual change during an outage—the system either alerts the team or automatically corrects the deviation depending on your policies.
Incident response becomes dramatically faster with automation on two fronts. First, diagnostic data collection happens instantly. Users complain about connectivity issues? Automation immediately pulls interface status, routing tables, traffic patterns, and relevant logs from every device in the path. What took 30 minutes of manual data gathering happens in 30 seconds. Second, automated remediation handles routine issues without waking anyone up. Interface error-disabled at 2 AM? Automation identifies the cause, clears the condition if appropriate, re-enables the port, and documents everything in a ticket.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Network provisioning goes from multi-day marathons to fire-and-forget operations. Business units request new network segments for applications? Automation creates VLANs across distribution layers, configures trunk ports, updates routing protocols, modifies firewall rules, and validates connectivity end-to-end. A regional bank cut their provisioning time from three days (72 hours) to under 15 minutes using this approach. Same reliability, 99% less effort.
Proactive troubleshooting catches problems before users notice them. Continuous monitoring tracks health metrics—CPU usage, memory consumption, interface errors, even temperature sensors in equipment rooms. When thresholds get exceeded or patterns suggest developing issues, automated workflows gather detailed diagnostics, create incident tickets, and can even implement temporary workarounds while engineers dig into root causes during business hours.
Types of Network Automation Solutions and Tools
The network automation tool landscape breaks down into several distinct categories, each with different strengths and tradeoffs.
Script-based approaches use programming languages—usually Python—to interact directly with network gear. You write custom code that connects via SSH or APIs, sends commands, parses output, and makes intelligent decisions based on what comes back. Maximum flexibility, zero licensing fees, but you need solid programming chops and ongoing maintenance as your environment changes.
Configuration management platforms like Ansible, Puppet, and Chef originally automated Linux servers but added network device support over time. These tools use declarative formats where you describe desired end states in straightforward text files. The platform handles all the messy details of connecting to devices, implementing changes, and verifying results. Ansible dominates network automation specifically because it doesn't require agents on network devices and includes extensive pre-built modules for common tasks.
Intent-based networking platforms sit at the sophisticated end of the spectrum. Products like Cisco DNA Center, Juniper Apstra, and Arista CloudVision accept high-level business requirements—"ensure the finance department has secure, reliable connectivity"—and automatically translate that into specific device configurations, policies, and monitoring rules. These platforms continuously verify the network delivers intended outcomes and can self-heal issues automatically.
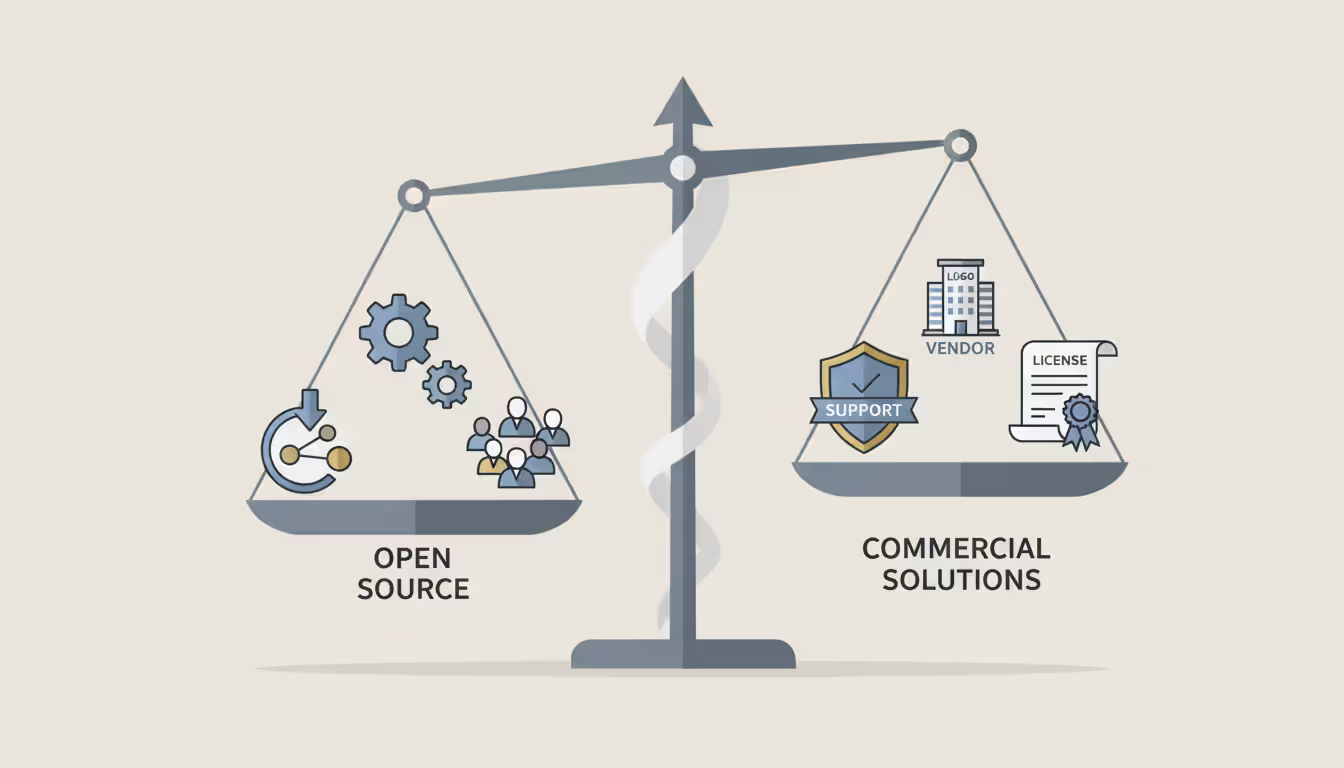
Open-source versus commercial presents the classic build-versus-buy decision. Open-source tools (Ansible, NAPALM, Nornir) provide serious capabilities without licensing costs, but implementation requires more internal expertise. Commercial platforms bundle vendor support, polished interfaces, and pre-built integrations, trading subscription fees for faster deployment and ongoing assistance.
| Tool/Platform | Where It Runs | How You Use It | What It Does Best | Who Should Use It | How You Pay |
| Ansible | Your datacenter or cloud | Write YAML playbooks | Managing configs across multiple vendors | Teams comfortable with YAML and basic scripting | Free core version (paid Red Hat support optional) |
| Python with Netmiko | Runs on your systems | Write Python code | Building custom workflows for unique needs | Engineers who already know Python | No cost (open-source libraries) |
| Terraform | On-prem or cloud hosted | Use HCL config language | Treating network and cloud as unified infrastructure code | DevOps teams managing hybrid environments | Free basics (paid enterprise features) |
| Cisco DNA Center | On-prem or cloud | Web interface plus APIs | Intent-based automation in Cisco networks | Organizations heavily invested in Cisco | Per-device subscriptions |
| SolarWinds NCM | Your choice of hosting | Graphical interface | Config backups and compliance for operations teams | Teams wanting low-code solutions | License per managed device |
How to Automate Network Tasks Step by Step
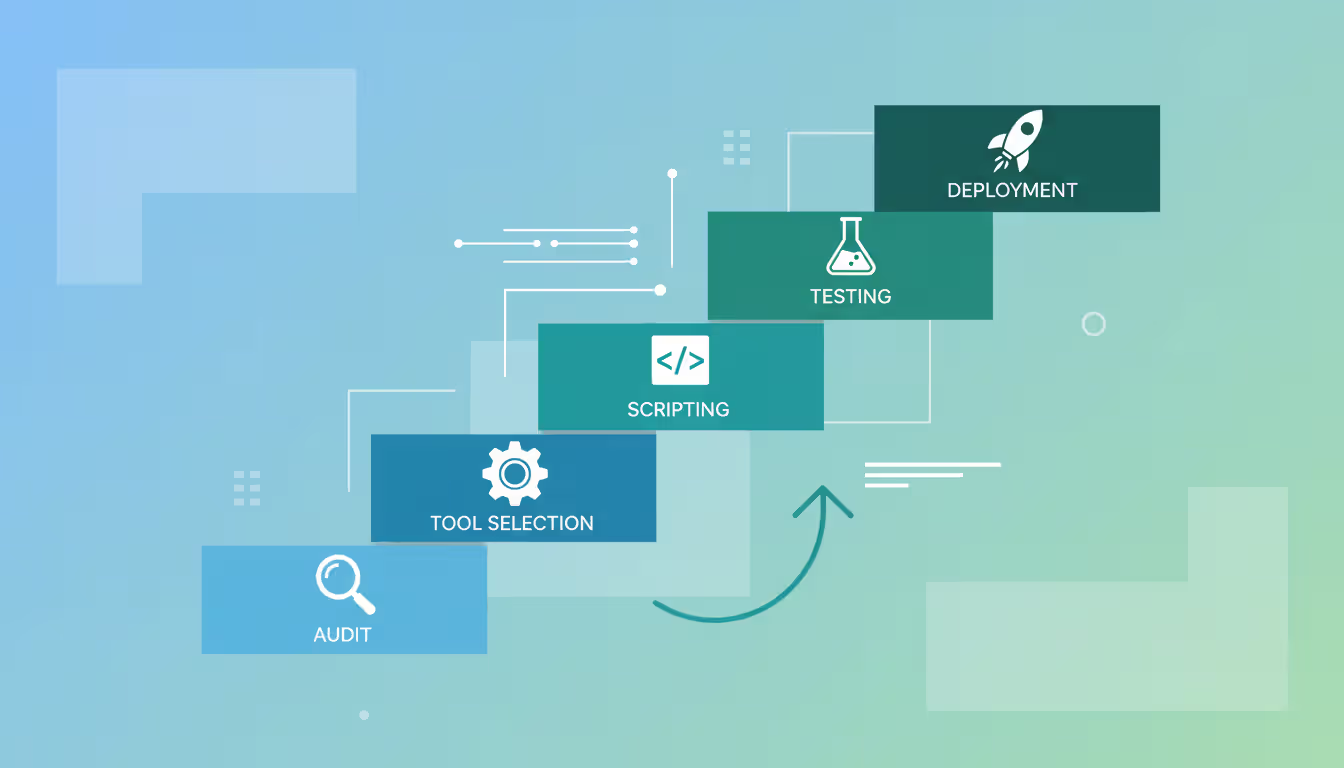
Jumping into automation without planning is a recipe for failure. You need structure.
Start with assessment. Document what you're working with: device makes and models, OS versions, which management protocols they support. Then identify pain points—specifically, which manual tasks eat the most time, cause the most mistakes, or create the biggest bottlenecks in delivering services. Rank potential automation candidates by impact versus difficulty. Daily config backups? High value, low risk, perfect first project. Automated failover procedures? Huge value when you need them, but requires extensive testing before you trust it in production.
Find your repetitive tasks by actually tracking how the team spends time. Shadow engineers for a full week and document every task that follows a predictable pattern. Configuration changes, credential rotations, certificate renewals, monthly capacity reports, compliance audits—these typically top everyone's list. Look specifically for tasks that happen frequently (daily, weekly) or touch many devices at once.
Pick the right tool based on your reality, not marketing materials. Running a single-vendor network where you're already deep in their ecosystem? Their proprietary tools might deliver value fastest. Multi-vendor shop? You need vendor-neutral platforms like Ansible. Got strong developers on the team? Python-based frameworks offer maximum control. Be brutally honest about skill levels—choosing tools that exceed your team's capabilities just creates expensive shelfware.
Build workflows incrementally. Pick one well-understood task and automate it completely before touching anything else. Config backups make a great starting point: script connects to devices, grabs running configs, stores them in version control with timestamps. Test exhaustively in a lab with devices mirroring production. Run it manually a dozen times, scrutinizing results each time, before you even think about scheduling it.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Test thoroughly, deploy cautiously. Build a lab environment that replicates production topology and configurations. Hammer your automation against lab devices first—not just happy path testing, but error conditions, edge cases, network failures during execution. Roll out in phases: start with non-critical devices, expand to a larger subset after a week of successful runs, then go broad. Keep manual procedures handy as backup during initial deployment. A healthcare IT team almost learned this the hard way—their automation script had a typo that would've disabled management access on 300 switches simultaneously. Caught it in lab testing, disaster averted.
Watch out for these mistakes: automating broken processes (fix the process first, then automate), skimping on error handling (automation must fail safely), inadequate logging (you need audit trails for everything), and no rollback plan (always have an undo button ready).
Network Automation and Orchestration: Key Differences
People use "automation" and "orchestration" interchangeably in conversations, but they're actually distinct concepts that complement each other.
Network automation executes specific, narrowly-defined tasks. Apply a configuration template. Collect interface statistics. Update an access control list. Restart a service. Each automated task stands alone with clear inputs and expected outputs. Think of automation as individual power tools—each one does its job really well.
Orchestration conducts multiple automated tasks like a symphony, coordinating them into complex workflows that accomplish business objectives. Deploying a new application? Orchestration sequences these steps: provision VLANs on distribution switches first, then configure routing between segments, update firewall rules to allow necessary traffic, modify load balancer pools to include new servers, finally verify end-to-end connectivity. Orchestration manages dependencies (you need routing before testing connectivity works), handles conditional logic (if firewall updates fail, roll back the network changes), and implements error recovery procedures.
When should you use each? Deploy automation for operational tasks that repeat frequently—daily backups, weekly compliance scans, routine changes. Bring in orchestration for complex, multi-step processes that span technology domains—provisioning new services, executing disaster recovery failover, responding to security incidents. Most teams start with straightforward automation and gradually layer in orchestration as their automation library matures.
Real-world integration shows the power of combining both approaches. A regional ISP uses orchestration to provision customer VPN services end-to-end: their orchestration platform receives orders from the billing system, kicks off network automation to configure PE routers, invokes security automation for firewall policy updates, triggers monitoring automation to establish service-level checks, and updates the CMDB—all without anyone touching a keyboard. Total time from order to active service: under five minutes, with complete audit trails automatically generated.
Modern orchestration platforms (StackStorm, ServiceNow, BMC Helix) integrate with network automation tools through APIs, calling Ansible playbooks, Python scripts, or vendor tools based on events, schedules, or service requests.
Choosing the Right Network Automation Tool
Selecting automation tools requires balancing technical requirements, organizational readiness, and where you want to be in three years.
Scalability matters more than teams initially expect. A tool that handles 50 devices smoothly might choke on 5,000. Evaluate how platforms manage large inventories, execute tasks in parallel across hundreds of devices, and perform under heavy load. Cloud-based platforms generally scale more gracefully than on-premises installations, though you're trading dependency on internet connectivity and vendor uptime for that convenience.
Support and community dramatically impacts long-term success. Commercial platforms bundle formal support contracts, guaranteed response times, professional services for implementation help. Open-source tools depend on community forums, available documentation, and third-party consultants you hire yourself. Gauge your team's troubleshooting independence honestly—strong technical teams love open-source flexibility, but smaller teams often need vendor support safety nets.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
Integration capabilities determine whether automation actually fits your existing operational workflows or creates isolated islands. The tool needs to play nicely with your CMDB, ticketing system, monitoring platform, and identity management. API quality matters enormously. Can it receive webhooks for event-driven automation? Can other systems call it programmatically? Is the API actually documented, or just theoretical?
Required skills kill more automation projects than technical limitations. Python-based frameworks demand programming expertise traditional network engineers typically lack. YAML-based tools like Ansible lower barriers but still require understanding data structures, conditional logic, and loops. GUI-driven platforms are most accessible but sacrifice flexibility for complex scenarios. Assess current team capabilities realistically and their willingness to learn new approaches. Budget training time—three to six months isn't unusual. Consider hiring or contracting specialized expertise for initial implementation to accelerate time-to-value.
Total cost extends way beyond sticker price. Calculate everything: software licenses or subscriptions, hardware or cloud resources to run automation platforms, training and certifications for staff, consulting services for implementation, ongoing maintenance effort. Open-source tools cost zero for licenses but demand more internal expertise. Commercial platforms charge subscription fees but reduce implementation time substantially. A mid-sized enterprise found that despite paying significantly higher licensing costs, a commercial platform delivered faster ROI because their team became productive in weeks rather than spending months building expertise.
Run proof-of-concept pilots before making commitments. Take 30-60 days and implement a representative use case—config backups plus compliance checking work well—fully with your top two or three candidates. Measure implementation time, ease of use, performance, and environmental fit. Critically, involve the engineers who'll actually use it daily in evaluation; their buy-in determines whether adoption succeeds or the tool gets abandoned six months after purchase.
Frequently Asked Questions About Network Automation
Network automation has crossed the line from "nice to have efficiency boost" to "operational necessity" for any IT team managing modern infrastructure. The combination of exploding network complexity, escalating security requirements, and chronic skills shortages makes purely manual management approaches unsustainable.
What works: starting with clear objectives, realistic scope boundaries, and tool selection that matches actual team capabilities rather than aspirational ones. Automate repetitive, high-frequency tasks first to build momentum and demonstrate value. Configuration management, compliance monitoring, and backup automation deliver quick wins that justify investment in more ambitious capabilities later.
Technical barriers have dropped significantly—tools now accommodate everyone from beginners wanting GUI-driven platforms to advanced practitioners needing powerful frameworks for custom solutions. The harder challenge is usually cultural: transitioning from manual, reactive operations to programmatic, proactive management demands changes in processes, skills development, and fundamental mindset shifts.
Organizations embracing network automation position themselves to deliver services faster, operate more reliably, and redirect engineering talent toward innovation instead of endless maintenance cycles. The real question isn't whether to automate network operations anymore—it's how quickly you can build automation capabilities before operational complexity grows faster than your team's capacity to manage it manually.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




