
Modern enterprise server room with organized network rack equipment, switches with LED indicators, neatly routed fiber and copper cables, cool blue ambient lighting
Network Infrastructure Guide
Content
Content
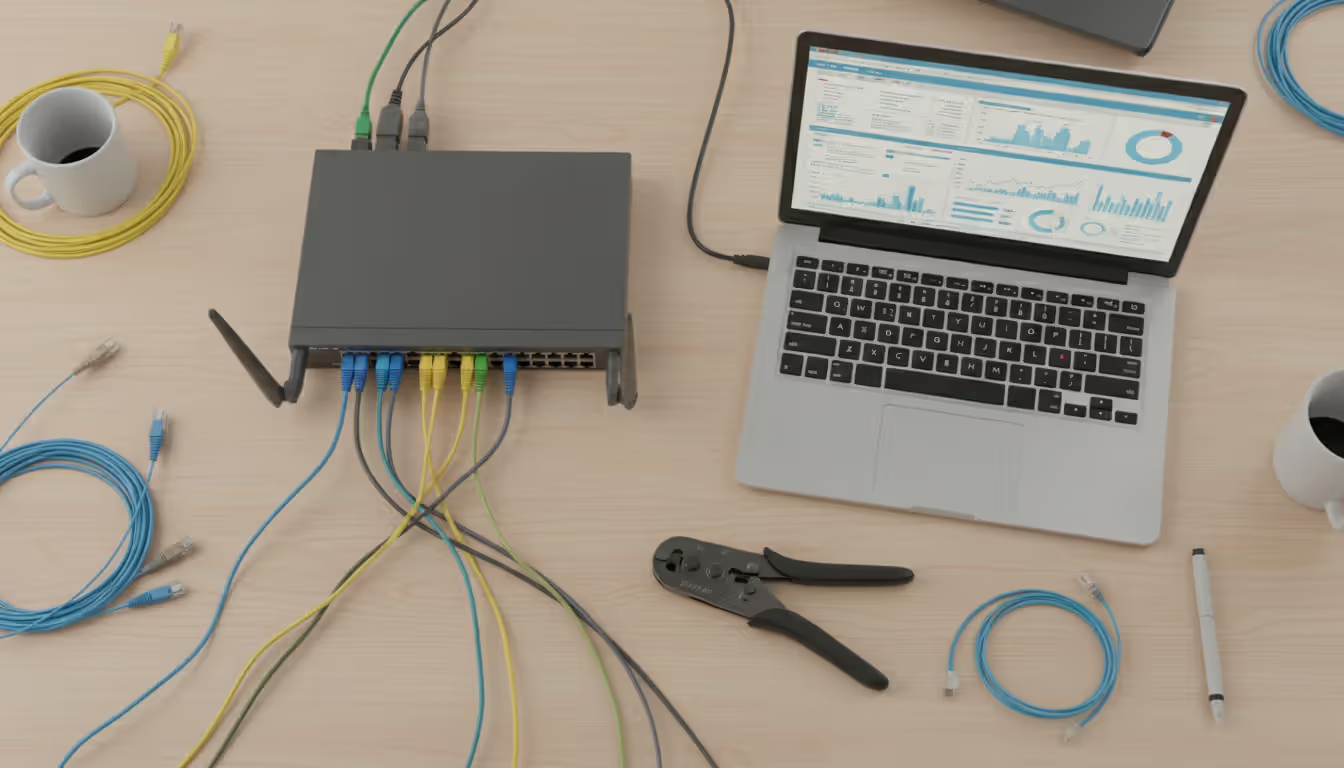
Think of network infrastructure as the nervous system of your organization—it's what lets different parts of your business actually talk to each other. You've got physical equipment like routers and switches, cables running through walls, wireless signals bouncing around your office, plus all the software that makes these pieces work together.
Here's what actually makes up network infrastructure: routers directing traffic between networks, switches connecting devices in your office, fiber and copper cables carrying data, servers hosting applications, firewalls blocking threats, and wireless access points eliminating cable clutter. On the software side, you're looking at operating systems running on these devices, management platforms that let you control everything, and increasingly, virtual components that exist only as software.
Why should you care? When your network works well, nobody notices. Employees send emails, access cloud apps, join video calls—all without thinking twice. But when something breaks? Everything stops. Your e-commerce site goes down. Your point-of-sale systems freeze. Customer service can't access account information.
We've seen companies with solid network infrastructure experience 40-60% fewer unexpected outages than businesses piecing things together as they grow. That difference shows up in your bottom line fast. One retail client calculated that each hour of network downtime cost them $47,000 in lost transactions alone—not counting frustrated customers who might shop elsewhere next time.
The companies doing this right treat their network as a strategic asset, not just another IT expense. They plan for growth, build in redundancy, and monitor everything continuously. The ones struggling? They're usually running equipment until it literally dies, then scrambling to fix things while their business bleeds money.
Author: Vanessa Norwood;
Source: clatsopcountygensoc.com
Hardware Components
Routers decide where data should go next. Your enterprise router looks at destination addresses and picks the fastest path to get packets where they need to go. Modern routers handle NAT (network address translation), prioritize important traffic over bulk file transfers, and increasingly pack security features that used to require separate appliances. A good router costs $800-$5,000 depending on how many sites you're connecting and how much traffic you're pushing.
Switches connect computers, printers, phones, and servers within your building. Unmanaged switches just forward traffic—plug and play, nothing fancy. Managed switches let you segment networks into VLANs, mirror ports for security monitoring, and aggregate links for more bandwidth. The price difference? An 8-port unmanaged switch runs $30. A comparable managed switch costs $200-$400. Worth it? Absolutely, once you pass 15-20 employees.
Firewalls decide what traffic gets through and what gets blocked. Traditional firewalls checked basic packet information—source address, destination port, protocol type. Modern firewalls dig deeper. They inspect application data, identify suspicious patterns, and block known malware signatures. A next-gen firewall examines packet contents alongside threat intelligence feeds, catching attacks that simple packet filtering misses entirely.
Servers run your applications and store your data. Physical servers still dominate when you need predictable performance or have compliance rules requiring dedicated hardware. One manufacturing company we worked with runs their ERP system on physical servers because their insurance underwriter requires it. Most everyone else is shifting to virtual servers or cloud instances.
Cabling creates the physical connection between devices. Cat6A cable handles 10 Gbps over 100 meters—plenty for most offices. Fiber optic runs faster and farther. Single-mode fiber easily covers 40 kilometers without signal loss. When should you use fiber? Between buildings, definitely. Within buildings, when you need more than 10 Gbps or runs longer than 100 meters. A structured cabling installation for a 50-person office typically costs $15,000-$25,000 including labor.
Wireless access points extend your network without cables. Consumer routers from Best Buy work okay at home. For business? You need enterprise APs with centralized management. Wi-Fi 6E operates in the 6 GHz band, which means less interference from neighboring networks. One client upgraded from consumer gear to proper enterprise access points and cut wireless support tickets by 80%. Users stopped complaining about dropped connections in conference rooms.

Author: Vanessa Norwood;
Source: clatsopcountygensoc.com
Software and Virtual Components
Network operating systems run on your routers and switches. Cisco IOS dominates enterprise networking, but you'll also see Juniper Junos, Arista EOS, and open-source options like VyOS. Each has different command syntax and capabilities. Standardizing on one or two platforms makes life easier—your team doesn't need to remember five different configuration languages.
Virtual networking moves routing and switching functions into software. VMware NSX creates virtual switches and routers on top of your hypervisor. Cisco ACI does similar things. Why virtualize? You can spin up new network segments in minutes instead of days. Configure everything through APIs instead of command-line interfaces. The learning curve is steep though—expect 3-6 months before your team gets comfortable.
Management platforms give you visibility across all your gear. SNMP (Simple Network Management Protocol) has been around forever—devices send trap messages when something breaks. Newer platforms use REST APIs, pulling data programmatically and integrating with ticketing systems. A good monitoring setup shows you bandwidth usage, errors, CPU load, and configuration changes across hundreds of devices from one dashboard.
Authentication systems control who can access what. RADIUS servers verify credentials when users connect to Wi-Fi or VPN. TACACS+ does the same for network device administration. 802.1X prevents unauthorized devices from joining your network—someone plugs in their laptop, switch asks for credentials before granting access. These systems seem like overkill until an ex-employee's laptop tries connecting six months after termination.
How to Design Network Infrastructure for Your Organization
Good network design starts with understanding what you actually need, not what vendors want to sell you.
Figure out your requirements first. How many users at each location? What applications do they run? A law firm pushing documents around needs different bandwidth than a video production studio moving 4K footage. One medical practice we worked with thought they needed 1 Gbps internet. Turned out their actual usage peaked at 80 Mbps. We saved them $800/month by right-sizing their circuit.
What about latency? Video calls get choppy above 150ms. VoIP needs under 100ms. Stock trading systems demand single-digit milliseconds. An accounting firm can tolerate 300ms without anyone noticing. Know your latency budget before designing anything.
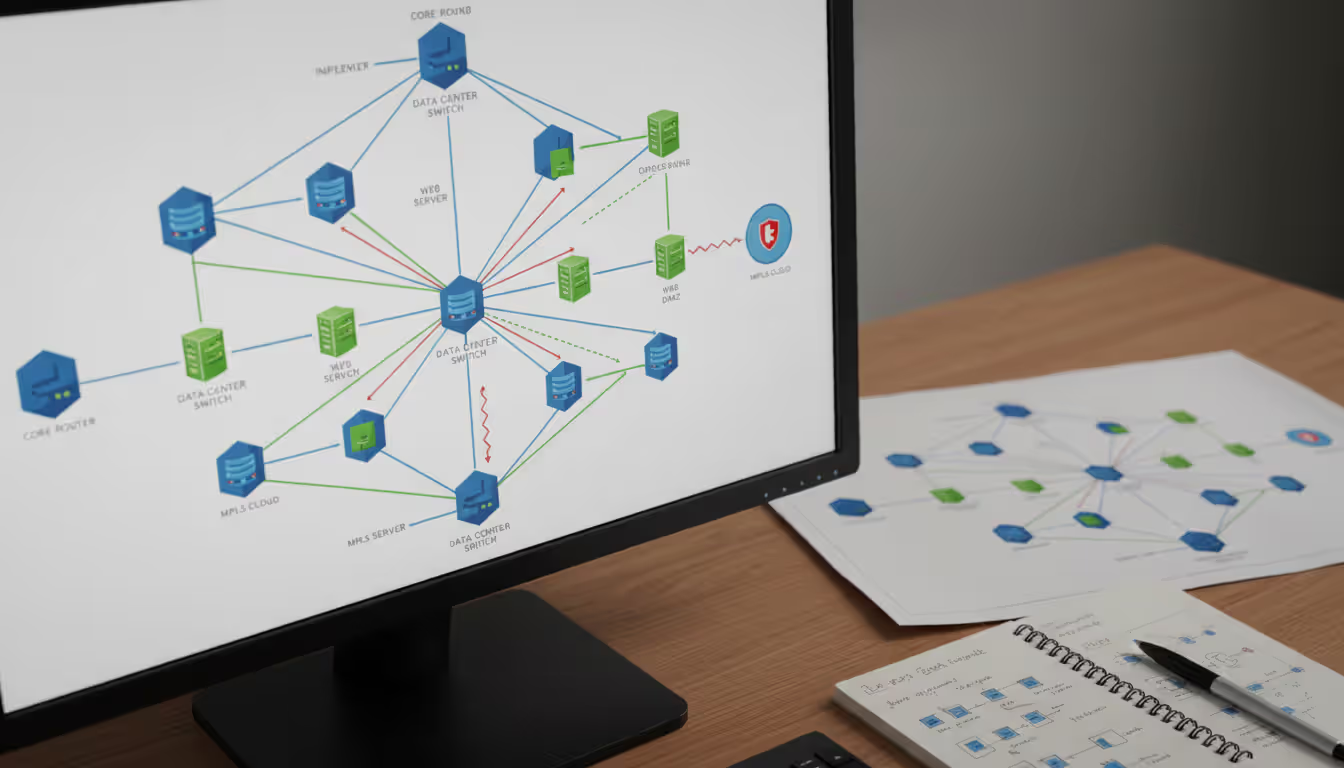
Pick a topology that matches your needs. Star topology puts a switch in the middle with everything connecting to it. Simple to manage. Single point of failure though—that central switch dies, everyone's offline. Mesh topology connects everything to everything else. Super resilient. Also expensive and complicated.
Most businesses use hierarchical design: access switches in each area connecting to distribution switches on each floor, which connect to core switches in your data closet. This three-tier model balances cost, performance, and manageability. A 200-person company might have 12 access switches, 3 distribution switches, and 2 core switches.
Plan for growth, but don't overbuild. If you're at 50 employees today and growing 20% yearly, you'll hit 75 in two years. Size your network for 90-100 users. Building capacity for 500 "just in case" wastes money on gear that's obsolete before you need it.
Oversubscription ratios matter here. If 48 employees connect at 1 Gbps each (48 Gbps total) and your uplink handles 10 Gbps, you've got 4.8:1 oversubscription. That's fine for typical office work. Video editors sharing files? You need 1:1—no oversubscription at all.
Redundancy determines your uptime. N+1 redundancy means one backup. You need one internet circuit, you buy two. 2N means complete duplication—two of everything. Geographic redundancy spreads equipment across multiple buildings or cities. Each level roughly doubles your cost while cutting failure risk by 90%.
A regional hospital we worked with went full 2N redundancy. Two independent internet providers. Dual core switches from different vendors. Redundant power from separate substations. Overkill for most businesses, but when lives depend on your network staying up, you spend the money.
Document everything. Network diagrams showing physical connections. Logical diagrams showing VLANs and subnets. IP address spreadsheets. VLAN assignments. Equipment inventory with serial numbers and firmware versions. When something breaks at 2 AM, documentation is the difference between a 20-minute fix and a 4-hour nightmare.
Companies with current documentation resolve outages 50-70% faster. We've done post-mortems where half the troubleshooting time was just figuring out what was connected where. That's preventable.
Author: Vanessa Norwood;
Source: clatsopcountygensoc.com
Network Infrastructure Management Best Practices
Daily operations determine whether your carefully designed network stays reliable or gradually decays into chaos.
Configuration management keeps things consistent. Save your baseline switch and router configs in Git or another version control system. When you make changes, do it during designated maintenance windows—Tuesday through Thursday works for most businesses. Avoid Monday (weekend changes cause unexpected Monday morning fires). Definitely avoid Friday (do you really want to work all weekend fixing what you broke?).
Configuration drift happens when someone makes a "quick fix" without documenting it. Six months later, nobody knows why that port is configured differently. Automated tools catch drift by comparing current configs against your baseline. One healthcare network we audit quarterly typically finds 15-20 undocumented changes per quarter. Half of them introduced security holes.
Patch management addresses vulnerabilities and bugs. Cisco releases major IOS updates quarterly with security patches arriving as needed. Test patches in your lab before production. Apply them to redundant devices in sequence, not simultaneously—if a patch bricks your backup router, you'll appreciate still having the primary running.
Organizations staying 95%+ current on patches within 30 days of release see 60% fewer security incidents. The companies getting breached? They're often running firmware 2-3 years old with known exploits freely available online.
Baseline your performance during normal times. Capture link utilization, CPU usage, memory consumption, packet loss, and latency when everything's working well. Baselines let you distinguish between "Tuesday afternoon load" and "actively being attacked."
We caught a data exfiltration attempt because outbound traffic jumped to 300% of baseline at 3 AM. Turned out an employee was uploading customer records to a personal Dropbox before giving notice. Without baseline data, that traffic might have looked normal.
Coordinate with vendors proactively. Maintain current support contracts with appropriate SLAs. Document escalation procedures. For strategic vendors, establish technical account manager relationships. When you call support as a stranger, you get tier-1 reading from scripts. When you call as a known contact with a TAM relationship, you get the senior engineer's cell number.
Monitor capacity before it becomes a problem. Set alerts at 70% utilization for investigation. At 85%, you're planning urgent upgrades. Above 80% sustained utilization, performance degrades even if you're not technically at capacity. TCP windowing issues, increased packet loss, and queueing delays all creep in.
Network Infrastructure Monitoring Tools and Techniques
You can't manage what you can't see. Monitoring transforms your network from a black box into something you actually understand.
The difference between 5-minute problem detection and 2-hour detection often determines whether an issue affects three people or three hundred. Real-time monitoring catches problems before your CEO's email stops working and they're standing at your desk asking what's wrong.
Track the right metrics for each component. Network links: bandwidth utilization, packet loss, latency, jitter. Switches: port errors, spanning tree changes, MAC table capacity, broadcast percentage. Routers: CPU during routing updates, BGP neighbor flaps, routing table size. Wireless: client counts per AP, channel utilization, signal-to-noise ratio per band.
Alert strategically or drown in noise. Threshold alerts trigger when metrics cross predefined values—bandwidth above 90% for five consecutive minutes. Anomaly alerts detect statistical outliers—traffic volume three standard deviations above your 30-day average.
Alert fatigue kills monitoring programs. If your team gets 80 alerts daily, they'll ignore everything including the critical ones. We worked with one IT team that received 200+ daily alerts, mostly false positives. After tuning, they got it down to 5-10 actionable alerts per day. Suddenly people started responding to alerts within minutes instead of hours.
Choose monitoring tools matching your environment:
| Tool | Key Features | Pricing Tier | Best Use Case | Deployment Type |
| PRTG Network Monitor | Auto-discovers devices, 200+ sensor types, customizable maps | $1,750-$15,500 one-time purchase | Small to mid-size networks under 5,000 sensors | Install on your own server or their cloud |
| SolarWinds NPM | Deep packet inspection, visualizes network paths, intelligent baselining | Starts around $2,995 per installation | Enterprise networks needing detailed troubleshooting | Your own servers |
| Datadog Network Monitoring | Built for cloud, monitors traffic flows, integrates with application monitoring | $15 per host monthly | Cloud-heavy or hybrid infrastructure | SaaS platform |
| Zabbix | Open-source, infinitely customizable, distributed monitoring architecture | Free with open-source license | Budget-conscious teams with strong technical skills | Your choice of hosting |
| Cisco ThousandEyes | Maps internet paths, monitors BGP routing, tracks cloud service performance | Custom pricing for enterprise | Multi-cloud environments dependent on SaaS apps | Vendor-hosted SaaS |
Build performance baselines over 30+ days. A CPU spike to 60% might be catastrophic or completely normal depending on context. Retail networks spike during holidays. University networks follow academic calendars with predictable quiet periods during breaks. Baseline across full business cycles or your "normal" data is meaningless.
Network Infrastructure and Security Integration
Security isn't something you bolt onto network infrastructure afterward. It's baked into every design decision from day one.
The 2025 threat landscape shifted toward attacking network infrastructure directly. Ransomware groups encrypt router configurations. Nation-state actors compromise switches as persistent footholds. The average breach we investigate involves 3-4 compromised network devices before attackers even touch endpoint systems.
Layer multiple security controls—defense in depth. Perimeter firewalls block external attacks. Internal network segmentation limits damage when perimeter defenses fail. Endpoint protection catches threats that bypass network controls. No single control works 100% of the time. Overlapping defenses compensate for individual failures.
Lock down administrative access. Network devices should require multi-factor authentication—password plus physical token or mobile app confirmation. Role-based access limits privileges to minimum necessary. Junior techs view configurations without modification rights. Senior engineers make changes but everything logs to your SIEM.
Privileged access management systems auto-rotate admin passwords and record privileged sessions. We reviewed logs after one security incident and watched the exact commands an attacker typed. That evidence made prosecution straightforward.

Author: Vanessa Norwood;
Source: clatsopcountygensoc.com
Encrypt data moving across your network. TLS 1.3 protects application traffic. MACsec encrypts traffic between network devices, stopping eavesdropping on internal segments. IPsec VPNs secure site-to-site connections. Modern hardware handles encryption with minimal overhead—typically under 5% throughput impact.
Deploy intrusion detection and prevention. Signature-based systems recognize known attack patterns from a database. Behavioral analysis catches zero-day exploits by identifying unusual traffic flows. Inline prevention blocks threats automatically. Passive detection alerts staff for investigation.
Should you block automatically or alert first? Depends on your risk tolerance. Financial services typically auto-blocks everything suspicious—false positives are annoying, but breaches cost millions. Manufacturing might alert-only because false positives could halt production.
Meet compliance requirements or face consequences. PCI DSS mandates network segmentation isolating cardholder data. HIPAA requires encryption for health information in transit. CMMC levels impose increasingly strict controls for defense contractors. Non-compliance means fines, contract losses, and potentially criminal liability.
One medical practice we worked with failed a HIPAA audit because their wireless network didn't isolate patient data properly. Their fine? $85,000 plus mandatory remediation and two years of quarterly audits. Fixing it properly upfront would've cost maybe $12,000.
When to Hire Network Infrastructure Consulting Services
Bringing in outside expertise makes sense for specific situations, not as a default answer to every challenge.
Your team is completely slammed. Three IT staff can't simultaneously handle daily operations, execute a five-site WAN upgrade, and implement zero-trust architecture. Consultants provide surge capacity for projects while your people keep the lights on. One client brought us in for a six-month data center migration—their internal team simply didn't have the hours.
You need specialized knowledge you'll rarely use again. Migrating from MPLS to SD-WAN requires skills your team might never need after initial deployment. Training staff for one-time projects often costs more than hiring consultants who already know the material. A three-month consulting engagement might run $60,000. Training plus opportunity cost of your team's time learning? Easily $80,000-$100,000.
You're locked into one vendor's ecosystem and want objective assessment. Internal teams develop unconscious bias toward familiar technologies. You've run Cisco for 15 years—of course every new project looks like a Cisco problem. External consultants evaluate Juniper, Arista, Fortinet, and others without vendor loyalty clouding judgment.
Compliance requirements demand specialized expertise. PCI DSS network segmentation requirements fill 40+ pages of technical specifications. Your team probably hasn't memorized them. Consultants specializing in payment card compliance know exactly what auditors expect and how to document it properly.
Calculate ROI before signing contracts. A $75,000 consulting project that cuts outages by 80% pays for itself in 6-12 months through avoided downtime. At $15,000 per hour of outage cost, preventing 40 hours of downtime annually saves $600,000. That's an 8x return.
Conversely, hiring consultants for routine tasks your team handles competently wastes money. We've seen companies pay consultants $200/hour to configure VLANs their own staff could do in their sleep. That's poor budget allocation.
Choose consultants carefully. Ask for references from similar organizations—same industry, comparable size, similar technical environment. A consultant who redesigned networks for Fortune 500 enterprises might struggle understanding a 75-person company's budget constraints.
Evaluate specific proposed staff, not generic promises. "We'll assign someone qualified" means you might get their best architect or a recent hire learning on your dime. Insist on meeting proposed team members before signing.
Intent-based networking changes everything about how we design enterprise networks. Instead of configuring thousands of individual device commands, you declare business intent—'guest users should get internet access but not internal resources'—and the system translates that into device configurations. Organizations still treating networks as static infrastructure they configure once and forget will struggle supporting cloud applications that spin up and down dynamically
— Jennifer Martinez
Frequently Asked Questions About Network Infrastructure
Your network infrastructure is either enabling business growth or limiting it. There's not much middle ground.
The components, design choices, management practices, and monitoring strategies covered here collectively determine which side you're on. Companies succeeding with network infrastructure share common patterns: deliberate design aligned with actual business needs, proactive monitoring catching problems before users notice, security integrated from initial planning rather than bolted on later, and management processes maintaining consistency across locations.
You've got a fundamental choice to make. Treat network infrastructure as a commodity expense minimized through lowest-cost procurement. Or recognize it as strategic investment multiplying the value of everything else you're trying to accomplish with technology. The performance gap between these approaches widens every year as business operations depend increasingly on reliable, secure, high-performance connectivity.
Network infrastructure decisions you make in 2026 shape organizational capabilities through 2031 and beyond. Invest time for thorough planning. Resist corner-cutting temptations on foundational elements. Build operational practices preserving infrastructure value across entire lifecycles.
Your network won't make customers choose your company over competitors. But it absolutely can drive them away if it's unreliable. Get this right once, maintain it properly, and you'll forget it exists—which is exactly the point.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




