
Secure server room with glowing encrypted VPN tunnel connections between network equipment racks in dark blue lighting
What Is a Site to Site VPN?
When your company operates from multiple physical locations, connecting those offices securely becomes a critical infrastructure challenge. A site-to-site VPN solves this problem by creating encrypted tunnels between entire networks, allowing branch offices, data centers, and headquarters to communicate as if they were on the same local network.
Unlike the VPN service you might use on your laptop to protect your browsing, a site-to-site VPN operates at the network level. It connects routers, firewalls, or VPN gateways at different locations, making the connection transparent to end users. Employees don't need to launch VPN clients or remember to connect—the infrastructure handles everything automatically.
Site to Site VPN Explained
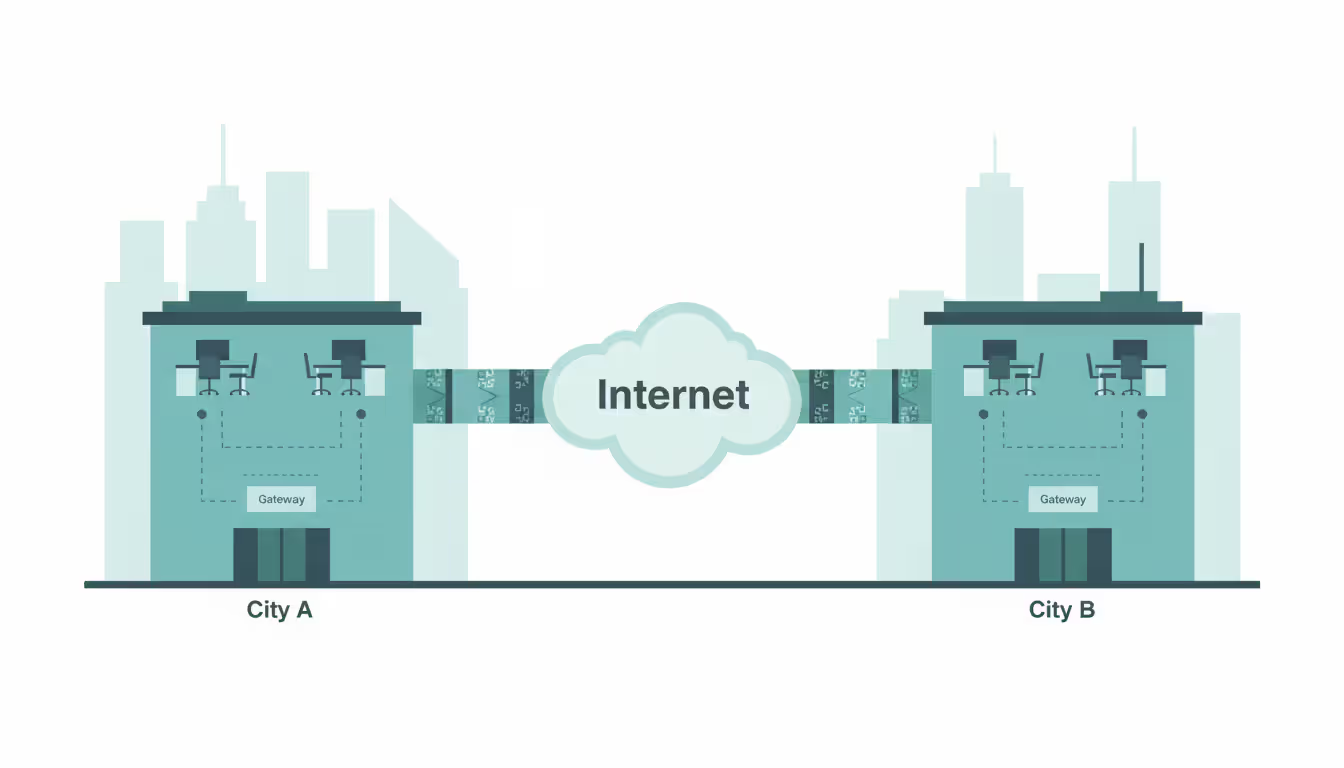
A site-to-site VPN creates a secure connection between two or more networks in different physical locations. Think of it as a private highway between your offices that runs over the public internet but keeps all traffic encrypted and isolated from prying eyes.
The core function centers on connecting entire networks rather than individual devices. When your Chicago office needs to access a database server in your New York headquarters, the VPN gateway in Chicago establishes an encrypted tunnel to the gateway in New York. Every device on the Chicago network can then communicate with resources in New York without additional configuration.
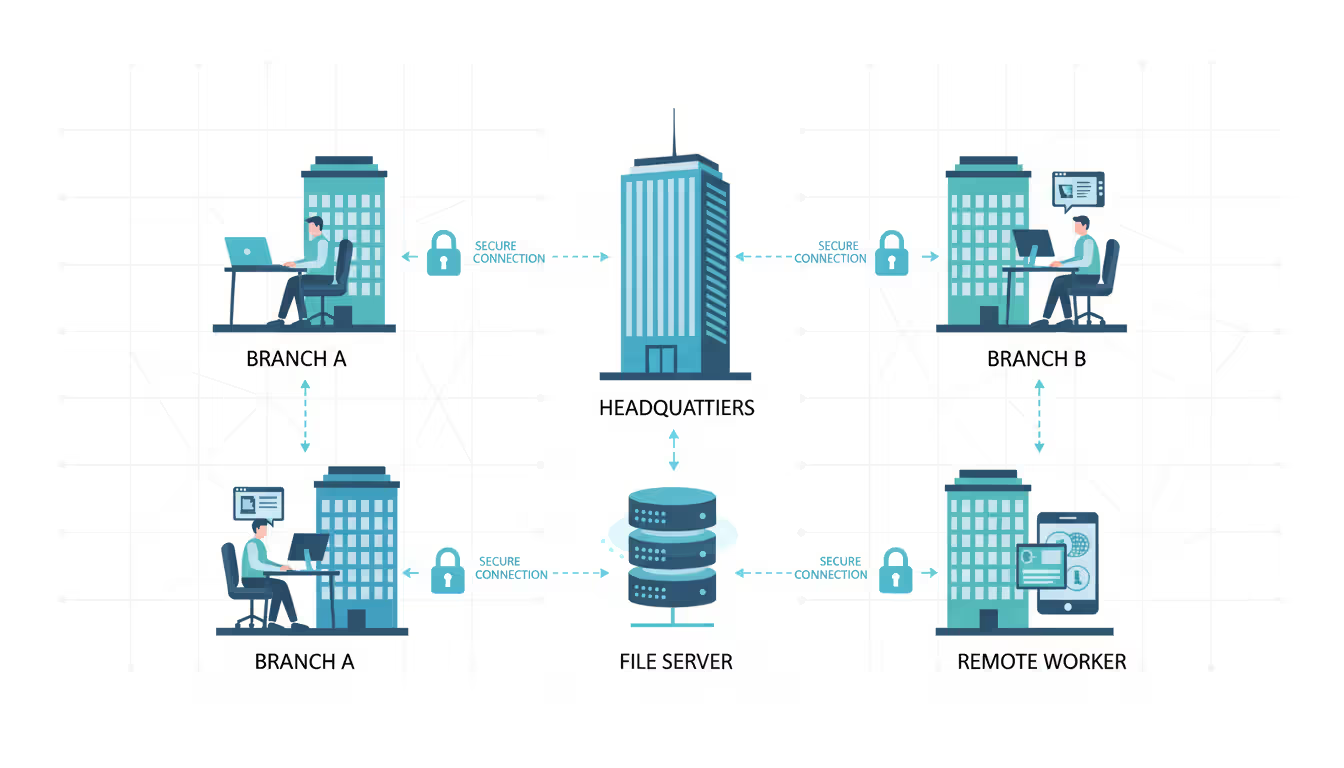
This differs fundamentally from a remote access VPN, where individual users connect their devices to a corporate network. Remote access VPNs require client software on each device and authenticate individual users. Site-to-site configurations authenticate networks themselves, with the VPN gateways handling all encryption and routing decisions. Your accounting team in Branch Office B doesn't need to know a VPN exists—they simply access the file server as if it were down the hall.
The distinction matters for administration too. Managing 200 remote workers means dealing with 200 different devices, operating systems, and potential configuration issues. A site-to-site VPN between three offices means managing three gateway devices with consistent configurations.
Author: Derek Hollowell;
Source: clatsopcountygensoc.com
How Site to Site VPN Connections Work
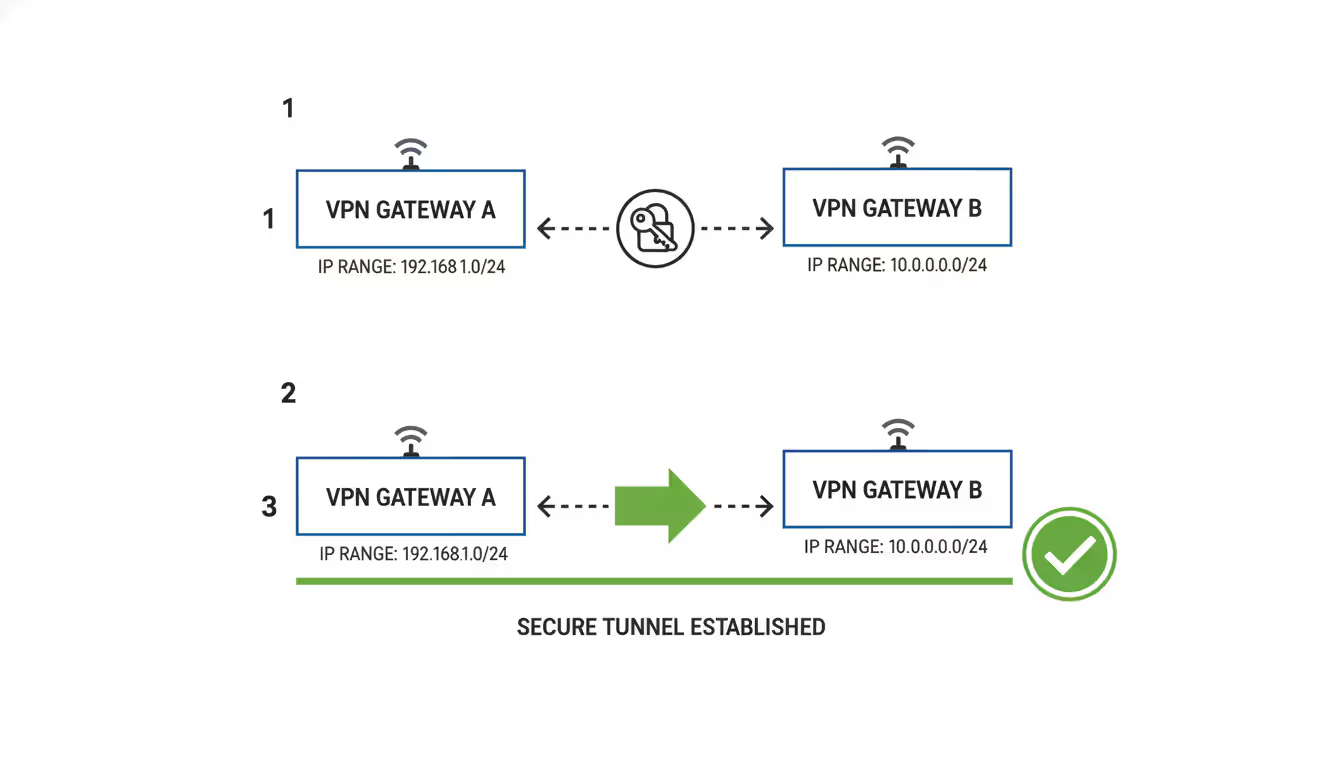
The connection process begins when a device at Site A attempts to reach a resource at Site B. The router or firewall at Site A recognizes that the destination IP address belongs to the remote network and forwards the packet to the VPN gateway instead of the regular internet route.
Gateway-to-gateway communication forms the backbone of the system. The VPN gateway at Site A encapsulates the original data packet inside a new packet with encryption applied. This outer packet has the gateway's public IP address as its source and the remote gateway's public IP address as its destination. The encrypted payload travels across the internet where anyone monitoring traffic sees only encrypted data flowing between two IP addresses—no visibility into the actual contents or even the true source and destination of the internal traffic.
When the packet arrives at Site B's gateway, the device authenticates the source, decrypts the payload, and forwards the original packet to its intended destination on the local network. The receiving server sees a request from Site A's internal IP address and responds normally. The return traffic follows the same process in reverse.
Encryption and tunneling protocols used in 2026 typically include IPsec (Internet Protocol Security), which remains the industry standard for site-to-site implementations. IPsec operates at the network layer and provides both encryption and authentication. Most enterprise deployments use AES-256 encryption with SHA-256 or SHA-384 for authentication. Some organizations have begun implementing IKEv2 (Internet Key Exchange version 2) for improved performance and automatic reconnection capabilities.
WireGuard has gained traction for site-to-site deployments due to its simpler codebase and faster performance, though IPsec still dominates in environments with strict compliance requirements or existing infrastructure investments.
Network topology considerations affect both performance and reliability. A hub-and-spoke design connects all branch offices to a central headquarters, which works well when most traffic flows between branches and the data center. However, if Branch A frequently communicates with Branch B, their traffic must traverse headquarters first, adding latency. A full mesh topology where every site connects directly to every other site eliminates this bottleneck but increases configuration complexity—five sites require ten separate tunnels, while ten sites need forty-five tunnels.
Types of Site to Site VPN Configurations
Site-to-site VPNs fall into two primary categories based on who owns the networks being connected.
Intranet-based site-to-site VPN connects multiple locations within the same organization. Your company owns and controls all networks on both ends of the tunnel. This configuration suits businesses with branch offices, remote data centers, or distributed facilities that need to share resources securely. A manufacturing company might connect its production facility, administrative office, and warehouse using intranet VPNs to share inventory databases, financial systems, and employee directories.
Extranet-based site-to-site VPN connects your organization's network to a partner, vendor, or customer's network. Each organization maintains control over its own network, but the VPN provides controlled access to specific resources. A hospital system might establish an extranet VPN with a medical billing company, allowing the billing service to access patient records without exposing the entire hospital network. Similarly, a manufacturer might connect to a supplier's inventory system to automate parts ordering.
When to use each type depends on trust boundaries and control requirements. Intranet VPNs assume both sides operate under the same security policies and administrative control. You can implement more permissive firewall rules because you trust both networks. Extranet VPNs require stricter access controls since you're connecting to an external entity with different security standards and potentially conflicting interests.
| Feature | Intranet-Based Site-to-Site VPN | Extranet-Based Site-to-Site VPN |
| Primary Use Case | Connecting branch offices, data centers, and facilities within one organization | Connecting to partner, vendor, or customer networks |
| Network Ownership | Single organization controls all connected networks | Multiple organizations, each controlling their own network |
| Trust Level | High—all sites operate under unified security policies | Limited—external organization has different policies and priorities |
| Access Control | Broader access typical; entire networks may communicate freely | Strict segmentation required; access limited to specific resources |
| Security Requirements | Standard encryption and authentication | Enhanced monitoring, stricter firewall rules, and audit logging |
| Typical Scenarios | Multi-location retail chains, distributed manufacturing, regional offices | Supply chain integration, outsourced services, B2B data exchange |
| Cost Considerations | Predictable; scales with number of company locations | May involve contractual agreements and shared infrastructure costs |
Benefits of Using a Site to Site Network
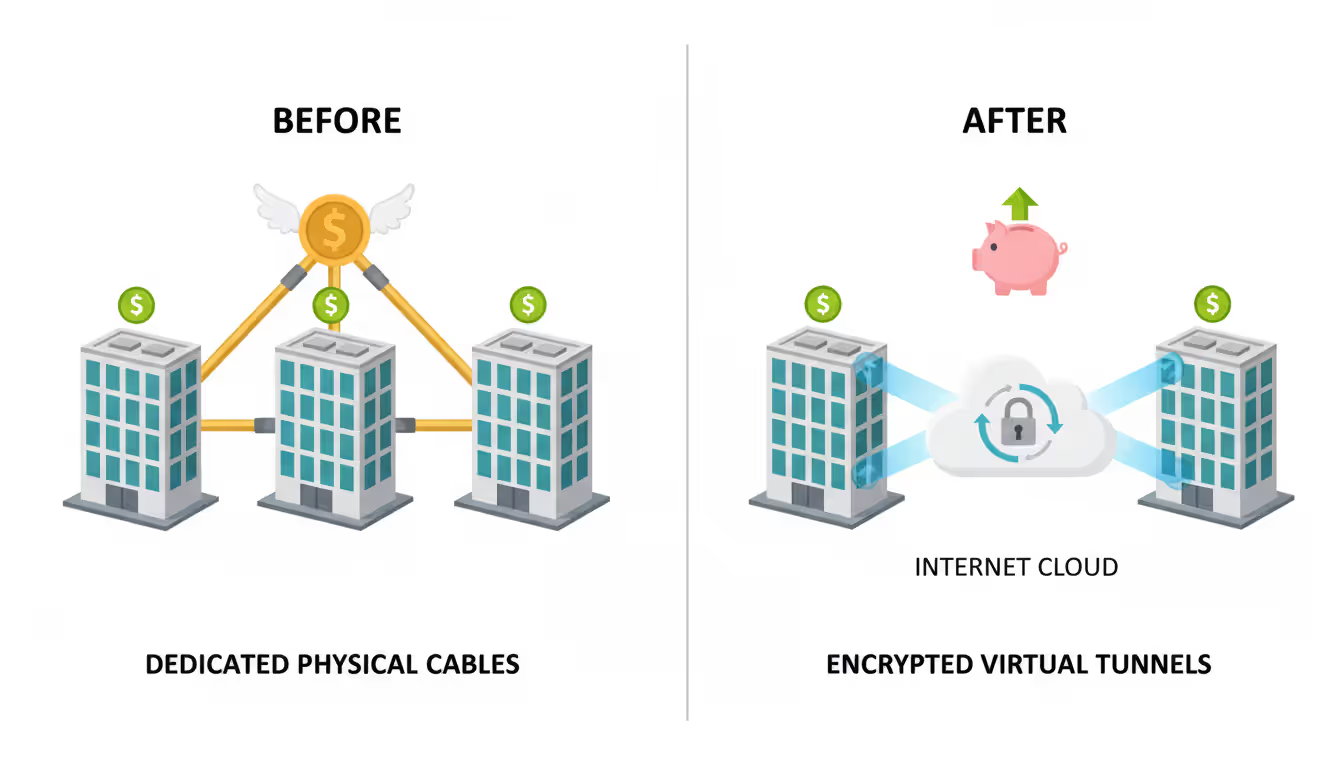
Secure communication between branch offices represents the most obvious advantage. Without a VPN, connecting remote locations requires either sending sensitive data over the public internet unencrypted or investing in expensive dedicated connections. A site-to-site VPN encrypts all inter-office traffic automatically, protecting customer data, financial records, and proprietary information from interception.
Cost savings versus dedicated leased lines can be substantial. A dedicated T1 line or MPLS connection between two offices might cost $500 to $2,000 per month per location. A site-to-site VPN runs over existing internet connections, requiring only the one-time cost of VPN-capable hardware (often already present in enterprise routers) and minimal monthly overhead. A company with five locations might save $30,000 to $100,000 annually compared to dedicated circuits.
Author: Derek Hollowell;
Source: clatsopcountygensoc.com
The trade-off involves sharing bandwidth with regular internet traffic and accepting that performance depends on public internet reliability. For many businesses, this represents an acceptable compromise given the cost differential.
Scalability for growing businesses proves easier with VPN infrastructure. Adding a new office to a dedicated line network requires ordering circuits, waiting for installation, and paying setup fees. Adding a new site to an existing VPN topology means configuring one additional gateway and updating routing tables—work that typically takes hours rather than weeks. A rapidly expanding company can establish new locations without waiting for telecom provisioning.
Centralized resource access simplifies IT management considerably. Your email server, file storage, and business applications can remain at headquarters while employees at any location access them seamlessly. This eliminates the need to replicate infrastructure at each site or manage complex synchronization between distributed servers. Software updates, security patches, and backup procedures happen once at the central location rather than repeatedly at each branch.
Common Use Cases for Site to Site VPN
Multi-location businesses represent the primary use case. Retail chains connect stores to headquarters for inventory management and point-of-sale data. Law firms link offices to share case files and research databases. Healthcare organizations connect clinics to centralized electronic health record systems while maintaining HIPAA compliance through encryption.
A regional accounting firm with offices in three cities uses site-to-site VPNs to maintain a single file server at the main office. Tax preparers at any location access client documents as if working locally, while IT staff manage backups and security from one location. During tax season, staff can work from any office without encountering access issues.
Author: Derek Hollowell;
Source: clatsopcountygensoc.com
Partner and vendor network access enables business process automation. Automotive manufacturers connect to parts suppliers, automatically transmitting production schedules and receiving shipment confirmations. The supplier's inventory system updates in real-time, reducing stockouts and excess inventory. The extranet VPN provides this integration without exposing either company's internal network to the other.
Cloud infrastructure connectivity has become increasingly important as businesses adopt hybrid cloud architectures. A site-to-site VPN connects on-premises data centers to cloud environments like AWS, Azure, or Google Cloud Platform. This allows applications running in the cloud to access on-premises databases securely, or lets on-premises applications leverage cloud computing resources during peak demand. The VPN ensures that traffic between your office and cloud resources doesn't traverse the public internet unencrypted.
Disaster recovery and backup scenarios rely on site-to-site VPNs to replicate data between primary and backup locations. A company might maintain its production environment at headquarters while continuously replicating critical data to a disaster recovery site across the country. The VPN ensures that backup traffic remains encrypted and isolated from other internet traffic, meeting compliance requirements for data protection.
How to Set Up a Site to Site VPN Connection
Prerequisites and planning steps determine success before you touch any configuration screens. Document the IP address ranges used at each location—overlapping subnets cause routing conflicts that prevent the VPN from functioning. If both offices use 192.168.1.0/24, you'll need to renumber one network before proceeding. Map out which resources at each site need to be accessible from other locations, as this informs firewall rules and access policies.
Verify that your internet connections at each site have static IP addresses or reliable dynamic DNS services. The VPN gateways need consistent addresses to establish tunnels. Confirm that your internet service doesn't block VPN protocols—some residential ISPs restrict IPsec or other VPN traffic.
Hardware and software requirements vary by network size and performance needs. Small offices might use VPN-capable routers costing $200 to $500, while larger deployments require dedicated VPN appliances or next-generation firewalls with VPN capabilities. Check that your existing network equipment supports the encryption standards and throughput you need. A router rated for 100 Mbps VPN throughput will bottleneck a 500 Mbps internet connection.
Author: Derek Hollowell;
Source: clatsopcountygensoc.com
For software-based solutions, both commercial options like Cisco AnyConnect and open-source alternatives like pfSense or OpenVPN can handle site-to-site configurations. Cloud-based SD-WAN solutions have simplified deployment by managing much of the configuration through centralized controllers.
Basic configuration steps follow a similar pattern across vendors, though specific menu locations and terminology differ. On each VPN gateway, you'll define the local network range, the remote network range, and the remote gateway's IP address. Configure the encryption protocol (typically IPsec), select encryption algorithms (AES-256 recommended), and establish a pre-shared key or certificate-based authentication.
Create firewall rules that permit VPN traffic between gateways—usually UDP port 500 for IKE and UDP port 4500 for NAT traversal. Configure routing so that traffic destined for remote networks gets directed through the VPN tunnel rather than the default internet gateway.
A common mistake involves forgetting to configure the return route. Site A might successfully send traffic to Site B, but if Site B's gateway doesn't know to route responses through the VPN tunnel, the connection fails. Both sides need complete, symmetrical configuration.
Testing and troubleshooting tips start with verifying basic connectivity. Can each gateway ping the other's public IP address? If not, firewall rules or ISP restrictions may be blocking traffic. Check that the VPN tunnel establishes successfully—most gateway interfaces show tunnel status. If the tunnel won't establish, verify that pre-shared keys match exactly (they're case-sensitive) and that both sides agree on encryption parameters.
Once the tunnel establishes, test actual traffic flow by pinging a device on the remote network from a device on the local network. If pings fail, check firewall rules on both gateways and verify that routing tables include the remote network. Use packet capture tools to determine where traffic stops—at the local gateway, in transit, or at the remote gateway.
Performance issues often stem from insufficient gateway hardware. If throughput is lower than expected, check CPU utilization on the VPN gateways during transfers. Encryption is CPU-intensive, and underpowered devices become bottlenecks. Latency increases are normal with VPN encryption—expect 5-15ms of additional latency from the encryption/decryption process.
The shift toward site-to-site VPNs reflects a broader recognition that network security must be built into infrastructure rather than bolted on afterward. Organizations that implement proper site-to-site connectivity establish a foundation for secure growth while maintaining the flexibility to adapt as their business evolves
— Marcus Chen
Frequently Asked Questions About Site to Site VPN
Site-to-site VPNs provide the secure connectivity infrastructure that multi-location businesses need without the cost and complexity of dedicated circuits. By encrypting traffic between network gateways, they extend your trusted network across geographic boundaries while maintaining security standards that protect sensitive business data.
The technology has matured to the point where implementation is straightforward for organizations with basic networking knowledge, though proper planning remains essential. Taking time to design your network topology, select appropriate hardware, and configure security policies correctly pays dividends in reliability and performance.
Whether you're connecting branch offices, integrating with business partners, or establishing hybrid cloud connectivity, site-to-site VPNs offer the flexibility to grow your network infrastructure as your organization evolves. The key lies in understanding your specific requirements and implementing a solution that balances security, performance, and cost-effectiveness for your particular situation.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




