
IoT fleet management control center with multiple screens showing device telemetry dashboards and network maps
IoT Device Management Tools Guide
Managing thousands of connected sensors, gateways, and endpoints across factories, cities, and supply chains demands more than spreadsheets and manual check-ins. IoT device management tools provide the centralized control plane that keeps fleets of connected hardware secure, updated, and operational at scale. Whether you're deploying smart meters, industrial sensors, or connected vehicles, understanding how these platforms work helps you avoid costly downtime and security gaps.
What Are IoT Device Management Tools
IoT device management tools are software platforms that centralize the provisioning, monitoring, configuration, and maintenance of connected devices throughout their operational life. Instead of logging into individual devices or relying on fragmented scripts, an iot device manager gives operators a unified interface to track device health, push updates, enforce security policies, and collect telemetry from hundreds or millions of endpoints.
These platforms sit between your device fleet and backend applications, acting as the control layer that authenticates new devices, manages credentials, monitors connectivity, and orchestrates firmware rollouts. They handle the operational complexity that emerges when you scale beyond a handful of prototypes into production deployments where devices run unattended in remote locations for years.
Core functions include device registration and identity management, remote configuration changes, diagnostic log collection, and coordinated software updates. Many platforms also provide rule engines that trigger alerts when devices go offline, consume abnormal power, or report sensor values outside expected ranges. This centralized visibility prevents small issues from cascading into fleet-wide failures.
For example, a utility company managing 500,000 smart meters needs to rotate encryption keys annually, patch vulnerabilities within days of disclosure, and detect tampering attempts in real time. Manual intervention at that scale is impossible. An iot device manager automates key rotation, stages firmware updates by region to limit risk, and flags anomalous behavior patterns that suggest physical interference.

Author: Adrian Keller;
Source: clatsopcountygensoc.com
Key Features of IoT Device Management Platforms
Modern platforms bundle capabilities that address the full operational lifecycle, from initial deployment through eventual decommissioning. The most critical features fall into three categories: provisioning and onboarding, security controls, and software maintenance.
Device Provisioning and Onboarding
Provisioning establishes a device's identity and grants it network access. Platforms typically support zero-touch provisioning, where devices authenticate using pre-installed certificates or hardware security modules, eliminating manual configuration steps. When a new sensor powers on, it contacts the management platform, proves its identity, downloads its configuration profile, and begins reporting data—all without human intervention.
Bulk provisioning workflows let operators upload manifests of device serial numbers and assign them to logical groups (by geography, firmware version, or customer account). This grouping simplifies policy application: all devices in the "North America manufacturing" group inherit the same update schedule and security rules. Platforms also maintain device twins—cloud-side representations of device state—so operators can query current configurations without polling every endpoint.
Security and Authentication Controls
Security features span identity verification, encrypted communication, and access policies. Certificate-based mutual TLS ensures both device and server authenticate each other, preventing rogue endpoints from joining the network. Platforms manage certificate lifecycles, issuing renewals before expiration and revoking credentials for decommissioned or compromised devices.
Role-based access control (RBAC) limits which users and applications can issue commands to specific device groups. A field technician might view diagnostics but lack permission to push firmware, while automated systems can trigger reboots but not delete devices. Audit logs track every configuration change and command execution, providing forensic trails when incidents occur.
Secure boot and attestation features verify that devices run unmodified firmware. Before accepting data or commands, the platform checks cryptographic signatures proving the device hasn't been tampered with. This matters in high-stakes environments like medical devices or industrial control systems, where unauthorized code could endanger safety.
Firmware and Software Updates
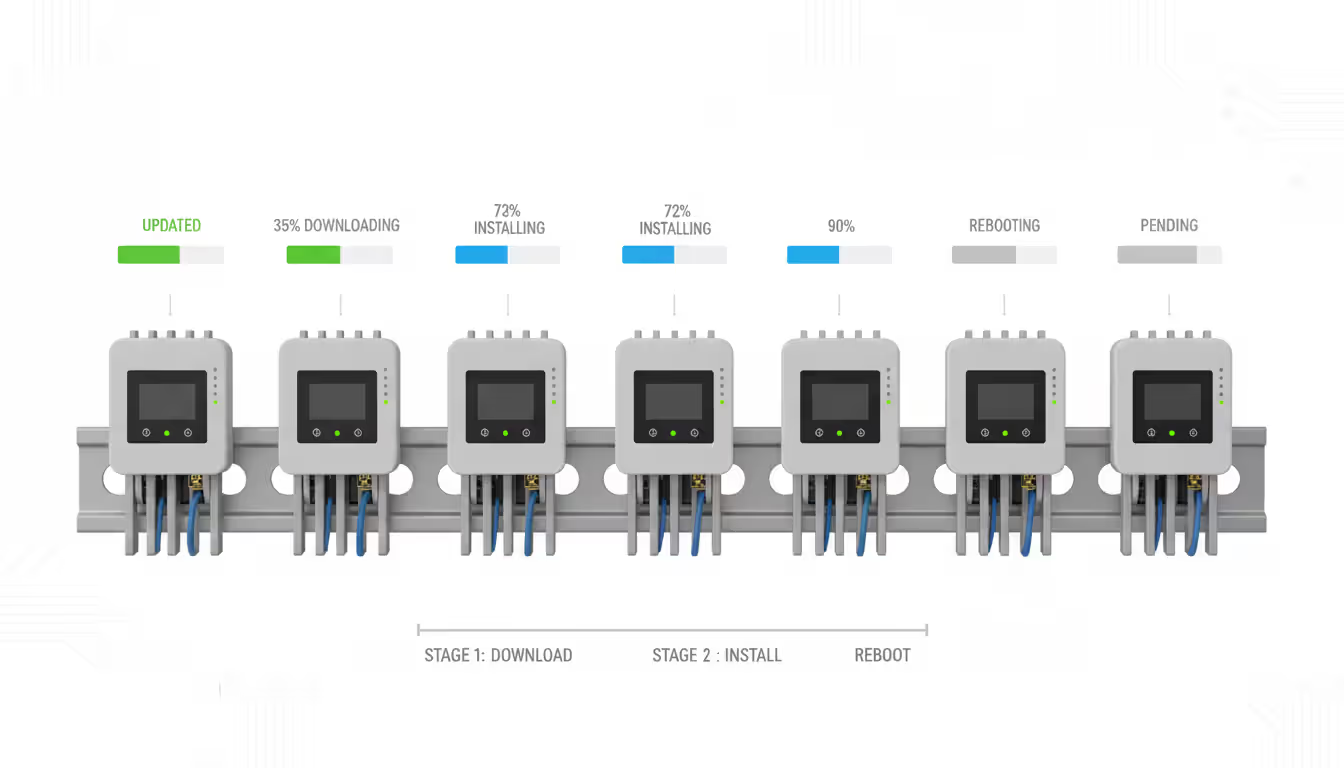
Over-the-air (OTA) update capabilities let operators patch vulnerabilities and add features without physical access. Platforms stage updates in phases: deploy to a small canary group, monitor for failures, then gradually roll out to the full fleet. If devices in the canary group fail health checks or report increased error rates, the rollout pauses automatically.
Delta updates reduce bandwidth consumption by transmitting only changed code blocks rather than full firmware images. For battery-powered sensors on cellular connections, this difference can extend operational life by months. Platforms also support rollback mechanisms, reverting devices to previous firmware versions if new code causes instability.
Scheduling features coordinate updates during maintenance windows or low-traffic periods. A fleet of connected streetlights might receive updates between 2 AM and 4 AM when failures cause minimal disruption. Operators set maximum concurrent update counts to prevent network saturation or simultaneous failures across critical infrastructure.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
How IoT Device Lifecycle Management Works
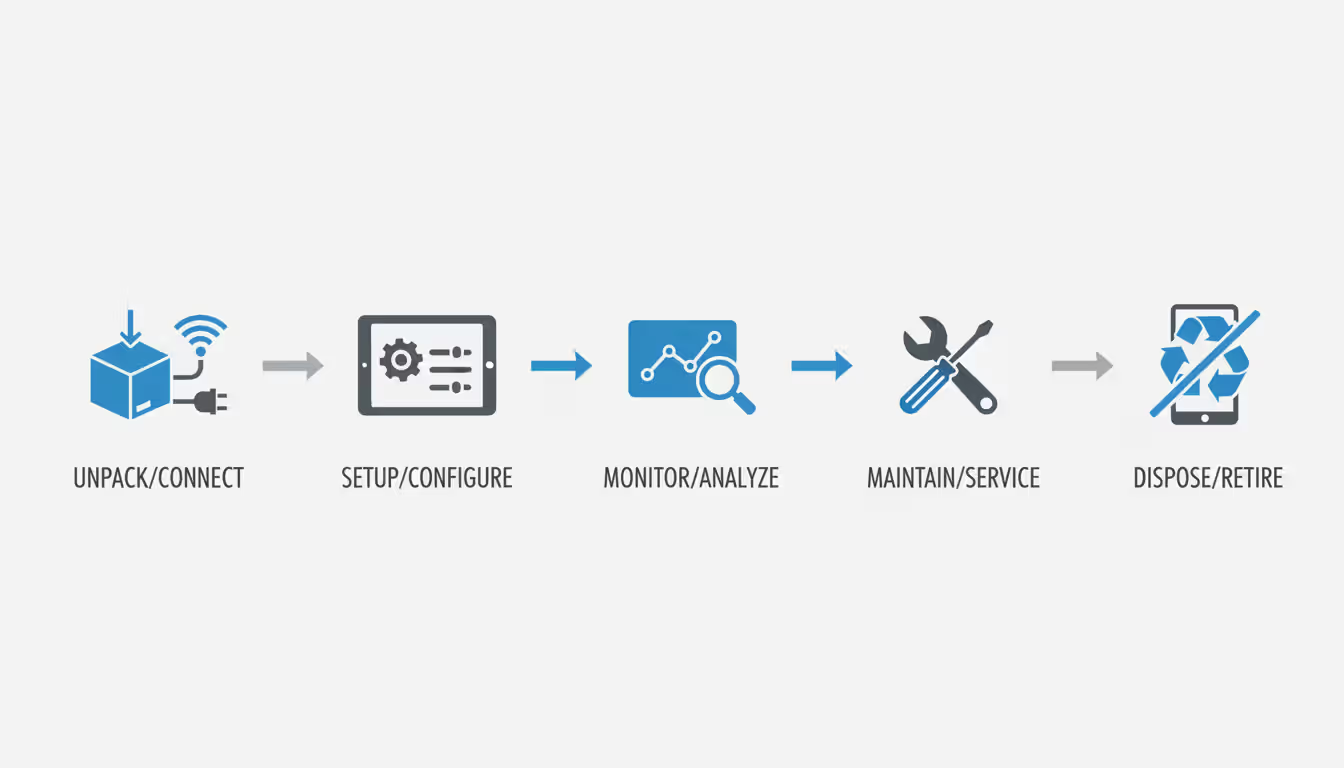
IoT device lifecycle management encompasses every stage from initial deployment through end-of-life decommissioning. The lifecycle typically divides into five phases: provisioning, configuration, monitoring, maintenance, and retirement.
During provisioning, devices receive credentials and join the network. Configuration assigns operational parameters—polling intervals, threshold values, communication protocols—tailored to each device's role. Monitoring tracks health metrics: uptime, battery voltage, memory usage, connectivity quality. Platforms correlate these signals to predict failures before they occur, triggering maintenance actions like battery replacement or antenna realignment.
Maintenance includes both reactive troubleshooting and proactive updates. When a device reports errors, operators can remotely access logs, adjust settings, or reboot without dispatching technicians. Scheduled maintenance applies firmware patches, rotates credentials, and refreshes configuration profiles to align with evolving security policies.
Scaling considerations grow critical as fleets expand. A deployment of 100 devices might tolerate manual provisioning, but 100,000 devices demand automation. Platforms must handle burst provisioning when factories ship large batches, distribute update traffic to avoid network bottlenecks, and maintain sub-second query response times across millions of device records.
Retirement involves credential revocation, data export, and decommissioning workflows. Devices removed from service must have their certificates invalidated immediately to prevent reuse by attackers. Platforms archive historical telemetry for compliance purposes while purging active records to free storage.
A common mistake is neglecting lifecycle planning during procurement. Devices with hardcoded credentials or no update mechanism become unmanageable liabilities. Evaluating lifecycle support before deployment—checking for secure provisioning APIs, OTA update capabilities, and vendor commitment to long-term patches—prevents expensive retrofits or premature replacements.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
IoT Device Gateway vs. Management Platform
Confusion often arises between iot device gateway hardware and management platforms. Gateways are physical or virtual appliances deployed at the network edge, translating between device protocols (Zigbee, Modbus, BACnet) and IP-based networks. They aggregate data from low-power sensors, perform local processing, and forward results to cloud services.
Management platforms are centralized software systems that control and monitor devices across all locations. While a gateway handles protocol conversion and local data aggregation, the platform manages device identities, configurations, and software versions fleet-wide.
These components work together: gateways connect devices that can't directly reach the internet, while the platform manages both the gateways and the devices behind them. A factory might deploy ten gateways, each connecting 500 sensors. The management platform treats each gateway as a managed device, pushing updates and collecting diagnostics, while also maintaining visibility into the sensors each gateway serves.
| Feature | Gateway | Management Platform |
| Protocol translation | Converts device protocols (Zigbee, Modbus) to IP | Communicates via standard protocols (MQTT, HTTPS) |
| Device provisioning | Registers locally connected devices | Centrally provisions and authenticates all devices |
| Data analytics | Performs edge processing and filtering | Aggregates fleet-wide data for analysis |
| Remote updates | May support local firmware caching | Orchestrates OTA updates across entire fleet |
| Scalability | Supports dozens to hundreds of local devices | Manages millions of devices globally |
| Primary use case | Connect legacy or low-power devices | Centralized control and lifecycle management |
Architecturally, gateways reduce latency for time-sensitive decisions. A manufacturing gateway can trigger emergency shutdowns based on sensor readings without waiting for cloud round-trips. The management platform then receives event logs and adjusts thresholds across all gateways to prevent future incidents.
Common IoT Device Testing Methods
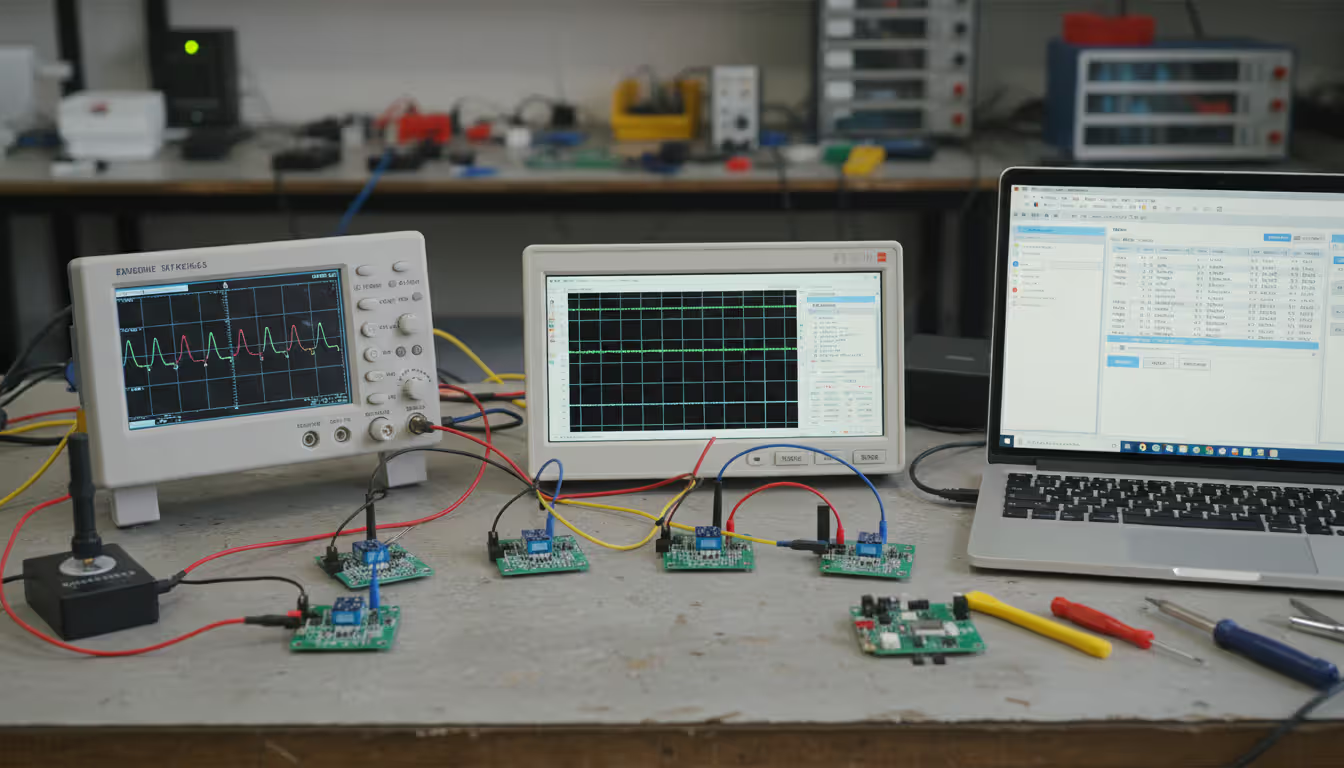
Testing validates that devices meet functional, security, and performance requirements before and during deployment. Four categories cover most validation needs: connectivity testing, security assessments, performance benchmarks, and compliance validation.
Connectivity testing verifies devices can establish and maintain network connections under real-world conditions. Tests include roaming between cellular towers, recovering from intermittent packet loss, and reconnecting after power cycles. Automated test suites simulate network failures—dropping 10% of packets, injecting 200ms latency spikes—to confirm devices retry connections appropriately and don't flood networks with reconnection attempts.
Security assessments probe for vulnerabilities in device firmware, communication protocols, and authentication mechanisms. Penetration testers attempt to extract credentials from device memory, intercept unencrypted traffic, and exploit known CVEs in third-party libraries. Fuzzing tools send malformed packets to uncover parsing bugs that could enable remote code execution.
Performance benchmarks measure throughput, power consumption, and response times under load. Battery-powered sensors undergo endurance testing, operating continuously while logging power draw to validate manufacturer claims. High-throughput devices like video cameras undergo stress tests, streaming maximum bitrate for 72 hours to identify memory leaks or thermal throttling.
Compliance validation confirms devices meet regulatory standards (FCC, CE, UL) and industry specifications (MQTT 5.0, LwM2M 1.1). Certification labs run standardized test suites, verifying electromagnetic compatibility, safety under fault conditions, and protocol conformance. Failing these tests delays market entry and risks recalls.
Continuous testing extends beyond pre-deployment validation. Management platforms enable remote iot device testing in production, running diagnostics that measure connectivity quality, verify cryptographic operations, and benchmark response times. Operators schedule periodic tests—weekly connectivity checks, monthly security scans—to detect degradation before it impacts operations.
A rule of thumb: allocate 20% of your deployment timeline to testing. Rushing devices into production without thorough validation leads to expensive field failures, security breaches, and emergency recalls that dwarf initial testing costs.
Author: Adrian Keller;
Source: clatsopcountygensoc.com
How to Choose an IoT Device Manager for Your Business
Selecting the right platform requires evaluating technical capabilities, vendor ecosystem, and total cost of ownership. Five criteria drive most decisions: scalability, protocol support, integration capabilities, vendor ecosystem, and pricing models.
Scalability determines whether the platform handles your current fleet and future growth. Platforms designed for thousands of devices often struggle at millions due to database bottlenecks or API rate limits. Ask vendors for reference customers at 10× your planned deployment size and request load testing results showing query latency and update throughput at scale.
Protocol support matters when devices use diverse communication standards. Platforms with native MQTT, CoAP, LwM2M, and HTTP support simplify integration, while proprietary protocols require custom adapters. Check whether the platform supports both IPv4 and IPv6, and whether it handles constrained devices that sleep between transmissions, requiring store-and-forward message delivery.
Integration capabilities determine how easily the platform connects to your existing infrastructure. Look for pre-built connectors to enterprise systems (ERP, CRM, SCADA), cloud data warehouses, and analytics tools. REST APIs and SDKs in your preferred languages (Python, Java, Go) enable custom integrations. Platforms that support industry standards like OPC UA or AMQP reduce vendor lock-in.
Vendor ecosystem strength affects long-term viability. Established vendors offer extensive documentation, active user communities, and third-party tools (monitoring dashboards, security scanners). Newer vendors may provide cutting-edge features but carry higher risk of acquisition, pivot, or shutdown. Evaluate vendor financial stability, customer retention rates, and roadmap transparency.
Pricing models vary widely. Some vendors charge per device per month, others by data volume or API calls. Calculate total cost at your three-year projected scale, including bandwidth charges, support tiers, and fees for advanced features (machine learning analytics, custom integrations). Watch for hidden costs: data egress fees, per-user licensing, or mandatory professional services.
Security and compliance requirements narrow options significantly. Regulated industries (healthcare, finance, utilities) demand platforms with SOC 2 Type II attestation, HIPAA compliance, or NERC CIP certification. Multi-tenancy features ensure customer data isolation in shared deployments, while private deployment options satisfy data sovereignty requirements.
Proof-of-concept deployments reduce selection risk. Deploy 50–100 devices on two finalist platforms, running them in parallel for 60 days. Measure operational overhead, troubleshooting ease, and update success rates. Involve the teams who'll use the platform daily—field technicians, security analysts, application developers—and gather their feedback before committing.
The difference between a successful IoT deployment and a failed one often comes down to lifecycle management. Organizations that treat device management as an afterthought face spiraling operational costs and security incidents that erode ROI. A robust management platform isn't optional infrastructure—it's the foundation that determines whether your IoT initiative scales or stalls
— Dr. Sarah Chen
Frequently Asked Questions
IoT device management tools transform unmanageable device sprawl into controlled, secure fleets that scale reliably. Platforms that centralize provisioning, monitoring, and updates reduce operational overhead while improving security posture and uptime. The key is matching platform capabilities—scalability, protocol support, integration depth—to your deployment's specific requirements.
Start by mapping your device lifecycle: how devices provision, what maintenance they'll need, and how you'll handle retirement. Evaluate platforms against these workflows, prioritizing features that address your biggest operational pain points. Run proof-of-concept deployments with real devices in production-like conditions before committing to a vendor.
Remember that device management isn't a one-time implementation but an ongoing operational discipline. Platforms evolve, device fleets grow, and security threats change. Choose vendors committed to long-term support, regular feature updates, and transparent security practices. The investment in robust device management infrastructure pays dividends in reduced downtime, faster incident response, and the confidence to scale your IoT deployments without losing control.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




