
Modern data center with server racks surrounded by a glowing blue protective shield dome symbolizing cloud database security
Secure Cloud Database Guide
Content
Content
Moving critical business data to cloud infrastructure creates real stakes. One misconfiguration, one weak password, one overlooked permission setting—any of these can hand attackers the keys to your kingdom. American businesses now store exabytes of customer records, financial transactions, and proprietary information in cloud environments. When breaches happen, they don't just cost money. They destroy relationships with customers who trusted you.
Protecting databases in the cloud means wrestling with encryption algorithms, identity systems, compliance frameworks, and choosing between providers who all claim to be the most secure. This guide cuts through the marketing fluff to show you what actually matters when your data lives on someone else's servers.
What Is a Secure Cloud Database
A secure cloud database runs on remote infrastructure managed by a hosting company, wrapping your data in multiple protection mechanisms that guard against unauthorized viewing, tampering, and deletion. The big shift from traditional databases? You no longer own the physical servers, network hardware, or even the underlying operating system that runs your database software.
Here's how it breaks down in practice. With on-premises databases, your team secures everything—the locked server room, the firewall appliances, the hypervisor layer, the OS patches, and the database configuration. Cloud databases flip this equation. The provider handles infrastructure security while you configure who can access what, manage user passwords, decide which data gets encrypted, and watch for suspicious behavior.
Three fundamental principles drive cloud database security: blocking unauthorized users, shielding information from prying eyes, and keeping systems running when someone attacks them. Strong identity verification stops intruders at the gate. Encryption turns stolen data into gibberish. Thoughtful system design isolates different workloads so one breach doesn't compromise everything.

Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Securing cloud data reaches far beyond the database engine itself. Think about the whole picture—API endpoints that applications use to query data, backup files stored in object storage, replication streams copying data between regions, and admin consoles where you make configuration changes. An exposed API can leak as much information as a compromised database password. Each component needs protection.
How Cloud Database Security Works
Picture security as layers of an onion. The outer layers catch obvious attacks. Inner layers protect against sophisticated threats that slip through initial defenses. Cloud providers build security into their infrastructure foundation, but you're the one who flips switches to activate protections and configures them correctly for your situation. That shared responsibility model trips up many organizations—even the toughest platform becomes vulnerable when you set permissions too broadly or pick weak passwords.
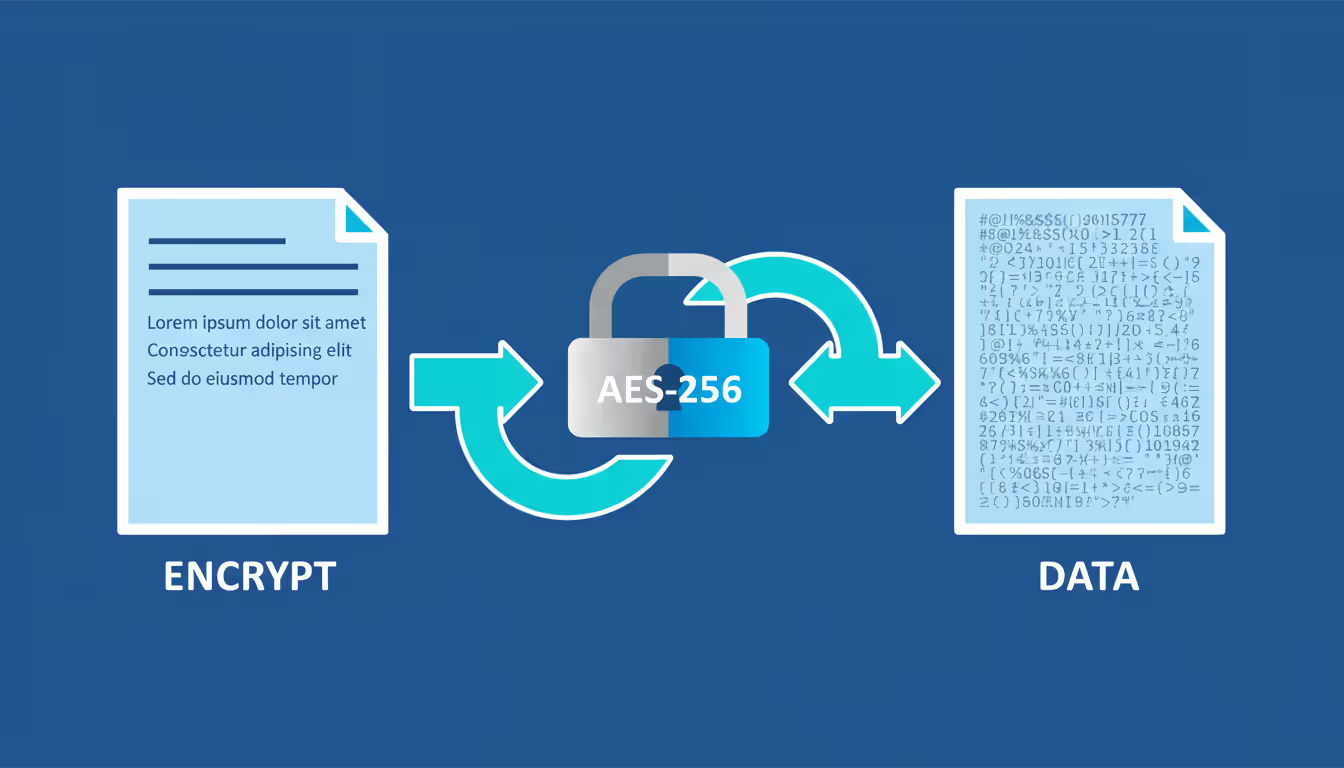
Encryption at Rest and in Transit
Encryption transforms readable data into scrambled nonsense that requires the correct decryption key to decode. When information sits on storage drives—what security folks call "at rest"—encryption stops thieves who steal physical hardware or gain unauthorized file system access from reading your customer records. Today's secure cloud providers typically use AES-256 encryption, the same specification that protects classified documents at government agencies like the NSA.
Information traveling between your application servers and the database, or copying between primary and replica databases, needs its own protection. Network-level encryption blocks interception attacks where criminals capture data packets flowing across the internet. Most modern providers now mandate TLS 1.3 for database connections, having retired older protocols with documented security flaws.
Managing encryption keys often becomes the weakest link that undermines everything else. Someone who steals your keys bypasses all the encryption you've implemented. Major providers lock keys inside hardware security modules (HSMs)—specialized devices that record every key access and physically resist tampering. Some companies go further with BYOK (Bring Your Own Key), maintaining complete control so the provider literally cannot decrypt their data even under court order.
Watch out for a trap that catches many teams: encrypting the production database while leaving backup files exposed. Backups contain the same sensitive information as your live database and deserve identical protection—encryption plus strict access controls.
Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Identity and Access Management
IAM systems determine which people and applications can perform specific actions on your database. Cloud platforms in 2025 commonly use permission schemes where you create roles with defined capabilities, then assign users to those roles instead of granting permissions person by person. Maybe you create an "analyst" role with read-only access to customer tables, while "DBA" roles can alter table structures and create new users.
Two-factor authentication inserts a second proof-of-identity beyond passwords. That might be a time-based code from an authenticator app, biometric verification like a fingerprint, or a physical USB security key. Passwords get compromised constantly through phishing emails and data breaches on other services. But attackers can't access your database without that second factor. For admin accounts with elevated privileges? Make MFA mandatory, not optional.
Application credentials create a particular headache. Your applications need database passwords to function, but hardcoding them into source code or configuration files creates obvious risk. Better secure cloud provider platforms offer automated credential rotation that generates fresh passwords on a schedule you define, plus secrets vaults that inject credentials at application runtime without ever writing them to disk.
Network access rules restrict which IP addresses can even attempt connections to your database. Private endpoints route all traffic through your provider's internal network, never touching the public internet. When you must accept connections from outside—maybe from a partner's data center or a mobile application—IP allowlists restrict access to known, trusted addresses.
Key Security Features to Look For
Shopping for a cloud provider? Ignore the marketing brochures. Instead, verify what they actually deliver when paying customers encounter real security incidents. Certifications demonstrate that outside auditors checked their controls, but you also need practical features that help your team manage security day-to-day.
Compliance certifications show a provider meets recognized standards. SOC 2 Type II reports document security controls that functioned consistently across six or twelve months, not just during a one-day audit. Healthcare organizations need HIPAA compliance for protected health information. Anyone storing credit cards must meet PCI-DSS requirements. Government agencies require FedRAMP authorization at appropriate impact levels. Without third-party verification, you're trusting a provider's self-assessment.
Backup and disaster recovery determine whether you survive ransomware, accidental deletions, or infrastructure failures. Look for automated backups on configurable schedules, point-in-time recovery that lets you restore to any moment within your retention window, and geographic redundancy that copies backups across multiple data centers. Test your recovery process quarterly—backups you've never actually restored are just expensive storage.
Audit logging captures every database interaction: successful and failed login attempts, the queries users executed, which records they viewed, configuration changes they made. Detailed logs enable forensic investigation after security incidents and prove compliance during regulatory audits. Critical detail: logs themselves must resist tampering, stored separately so attackers can't erase evidence of their break-in.
Vulnerability scanning and automated patching protect against published exploits. Managed database services handle patches without your involvement, though you'll want clarity on their patching schedule and whether you can delay updates during critical business periods. Self-managed databases running on cloud virtual machines? That patching responsibility falls on you.
Anomaly detection applies machine learning to spot unusual access patterns suggesting compromise. Picture a database account that normally runs read queries during business hours suddenly executing bulk exports at 3 AM. That deserves investigation. Advanced platforms correlate database activity with network traffic and authentication logs to identify sophisticated, multi-stage attacks.
Comparing Secure Cloud Database Providers
Picking a provider means matching what they offer against your specific requirements. The major platforms provide similar core capabilities but diverge in how they implement features, structure pricing, and integrate with other tools.
| Provider | Encryption Options | Compliance Certifications | Backup Frequency | Pricing Model | Support Tiers |
| AWS RDS | At-rest AES-256, in-transit TLS 1.3, customer-managed keys through KMS | SOC 2, HIPAA, PCI-DSS, FedRAMP High | Daily automated backups with transaction log point-in-time restore | Hourly instance charges plus separate storage and I/O fees | Developer, Business, Enterprise |
| Google Cloud SQL | At-rest AES-256, in-transit TLS 1.3, customer-managed encryption keys | SOC 2, HIPAA, PCI-DSS, ISO 27001 | Daily automated with additional on-demand snapshots | Per-second instance billing with storage fees | Basic, Production, Enterprise |
| Azure SQL Database | TDE encryption AES-256, Always Encrypted feature, BYOK support | SOC 2, HIPAA, PCI-DSS, FedRAMP High | Continuous automated with 7-35 day retention | DTU-based or vCore pricing plus storage | Basic, Standard, Premier |
| Oracle Cloud | TDE encryption AES-256, Data Safe features, customer-controlled keys | SOC 2, HIPAA, PCI-DSS, FedRAMP Moderate | Daily automated backups with point-in-time restore | OCPU-based charges plus storage | Basic, Advanced, Premier |
Certifications establish baseline credibility, but dig into specifics. A provider might hold HIPAA certification for certain regions or service tiers while other configurations lack approval. Confirm that your exact planned setup meets your compliance obligations.
Uptime SLAs quantify reliability promises. A 99.95% guarantee allows roughly four hours of annual downtime. Jump to 99.99% and you get only 52 minutes. Higher availability costs more, which matters less for revenue-generating databases than for internal tools. Read the fine print—most SLAs exclude downtime from maintenance windows you approved or problems with your own network connectivity.
Support tiers control response speed during crises. Basic support might respond to technical questions within 24 hours. Enterprise support promises 15-minute response for production outages plus a dedicated account manager who knows your environment. For databases running critical operations, premium support costs less than downtime.
Pricing models vary dramatically between providers. Hourly rates charge for compute capacity whether you're using it or not. Per-second billing (available from some vendors) reduces waste for variable workloads. Storage, I/O operations, and data transfer typically carry separate charges, making total cost hard to predict upfront. Request detailed cost estimates based on your projected workload.
Secure cloud interconnect matters when connecting databases across multiple providers or linking cloud databases back to on-premises systems. Dedicated network connections provide better throughput and security compared to VPN tunnels over the public internet, though they add complexity and monthly costs.
Common Security Risks and How to Avoid Them
Here's what nobody wants to admit: most database breaches result from embarrassingly simple mistakes rather than sophisticated hacking operations. Understanding these common pitfalls beats learning them from a breach notification letter.
Misconfiguration causes more cloud data exposure than any other factor. Databases accidentally set to allow public access. IAM roles granting excessive permissions. Encryption features disabled. These preventable errors have exposed billions of records over the past five years. Use infrastructure-as-code that defines security settings in version-controlled templates. Require peer review for all configuration changes. Run automated scanning tools that detect misconfigurations before deployment.
Weak passwords remain an attacker's favorite entry point. Default credentials left unchanged, common dictionary words, passwords reused from other breached services—all grant easy access. Implement password policies requiring minimum length (12+ characters), complexity mixing character types, and periodic rotation. Better approach? Eliminate passwords where feasible using certificate authentication or federated identity systems.
Monitoring gaps let breaches continue for months undetected. In 2024, the average detection time for data breaches reached 204 days—nearly seven months for attackers to copy files and establish persistence. Configure real-time alerts for suspicious activities: repeated failed logins, privilege escalations, unusual query patterns, abnormally large data exports. Crucially, assign someone to actually respond to alerts. Unmonitored alerts provide zero protection.

Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Insider threats involve employees, contractors, or business partners with legitimate access who abuse their privileges. A fired administrator deletes databases out of spite. A curious analyst exports customer records. A compromised contractor account gives attackers a foothold inside your security perimeter. Implement least-privilege access granting only necessary permissions. Separate duties so no individual controls all security aspects. Maintain detailed audit logs that survive account deletion.
Unpatched vulnerabilities hand attackers published exploits on a silver platter. Managed services handle database engine patches automatically, but you still need to update application libraries, database drivers, and any components you manage directly. Subscribe to security bulletins from your database vendor and cloud provider to learn about emerging threats.
Insecure sharing practices expose data when you need to collaborate with external partners or analytics platforms. Rather than duplicating entire databases, create views exposing only required fields. Implement data masking to redact sensitive values. Use secure cloud analytics platforms with built-in access controls and comprehensive audit trails.
Secure Cloud Database Use Cases by Industry
Different industries face distinct security requirements shaped by regulatory frameworks and the sensitivity of information they handle.
Healthcare organizations must satisfy HIPAA regulations mandating specific controls over protected health information (PHI). Cloud databases for healthcare implement encryption, comprehensive access logging, and breach notification workflows. Electronic health record systems, patient portals, and medical imaging platforms depend on cloud databases offering automatic backup, disaster recovery, and high availability guarantees—patient care can't wait for IT recovery. Secure cloud fax services integrated with databases must also meet HIPAA standards, maintaining audit trails documenting all transmitted records.

Author: Caleb Merrick;
Source: clatsopcountygensoc.com
Financial services face PCI-DSS requirements for payment card data plus regulations governing customer financial information. Banks, investment firms, and payment processors rely on cloud databases with tokenization replacing sensitive card numbers with non-sensitive substitutes, field-level encryption for personal identification data, and real-time fraud detection using secure cloud analytics. Regulatory reporting demands immutable audit logs resistant to after-the-fact modification.
Government agencies need FedRAMP-authorized services delivering enhanced security controls appropriate to data sensitivity. Law enforcement databases, citizen service portals, and inter-agency sharing platforms must enforce strict access controls, maintain geographic data residency keeping information within US borders, and provide detailed logging supporting Freedom of Information Act requests. Secure cloud interconnect capabilities let agencies share information while preserving security boundaries between departments.
E-commerce platforms store customer profiles, purchase histories, and payment details requiring PCI-DSS compliance and protection against credential stuffing attacks. Product catalogs, inventory management, and recommendation engines leverage analytics platforms to process customer behavior data while respecting privacy. During peak shopping periods like Black Friday, auto-scaling must preserve security controls even as database capacity increases to handle traffic spikes.
I've watched supposedly hardened cloud databases crumble the moment someone misconfigured access permissions or recycled a weak password from another service. Proper configuration and operational discipline drive roughly 80% of security outcomes, while selecting the right technology accounts for maybe 20%. Organizations that treat cloud security as an ongoing discipline rather than a one-time checkbox project consistently achieve stronger security postures and respond faster to incidents
— Sarah Chen
Frequently Asked Questions
Securing cloud databases demands more than selecting a reputable provider and hoping everything works out. The shared responsibility model requires you to actively configure encryption, implement strict access controls, monitor for suspicious activity, and maintain compliance with relevant regulations. Minor configuration errors expose sensitive data, while robust security practices protect against external attacks and insider threats alike.
Begin by identifying your specific compliance obligations and sensitivity levels for different data types. Select a provider offering relevant certifications and features matching your requirements. Implement defense in depth with multiple overlapping security layers rather than depending on any single control. Test backup and recovery procedures before emergencies strike.
Security isn't a one-time project you complete and forget. Review access permissions monthly to remove unnecessary privileges. Adjust defenses as the threat landscape evolves. Train your team on security best practices and explain why these practices matter. Done right, cloud database security prevents costly breaches, preserves customer trust, and allows you to leverage cloud capabilities without compromising data protection.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




