
Laptop with code editor open in front of illuminated server room racks in a modern data center
Infrastructure as Code Guide
Content
Content
Most IT teams have been there: it's 2 AM, your production database crashed, and you're scrambling through old Confluence pages trying to remember how the original server was configured. Was it the 16GB instance or the 32GB one? Which security groups were attached? What backup schedule did we set?
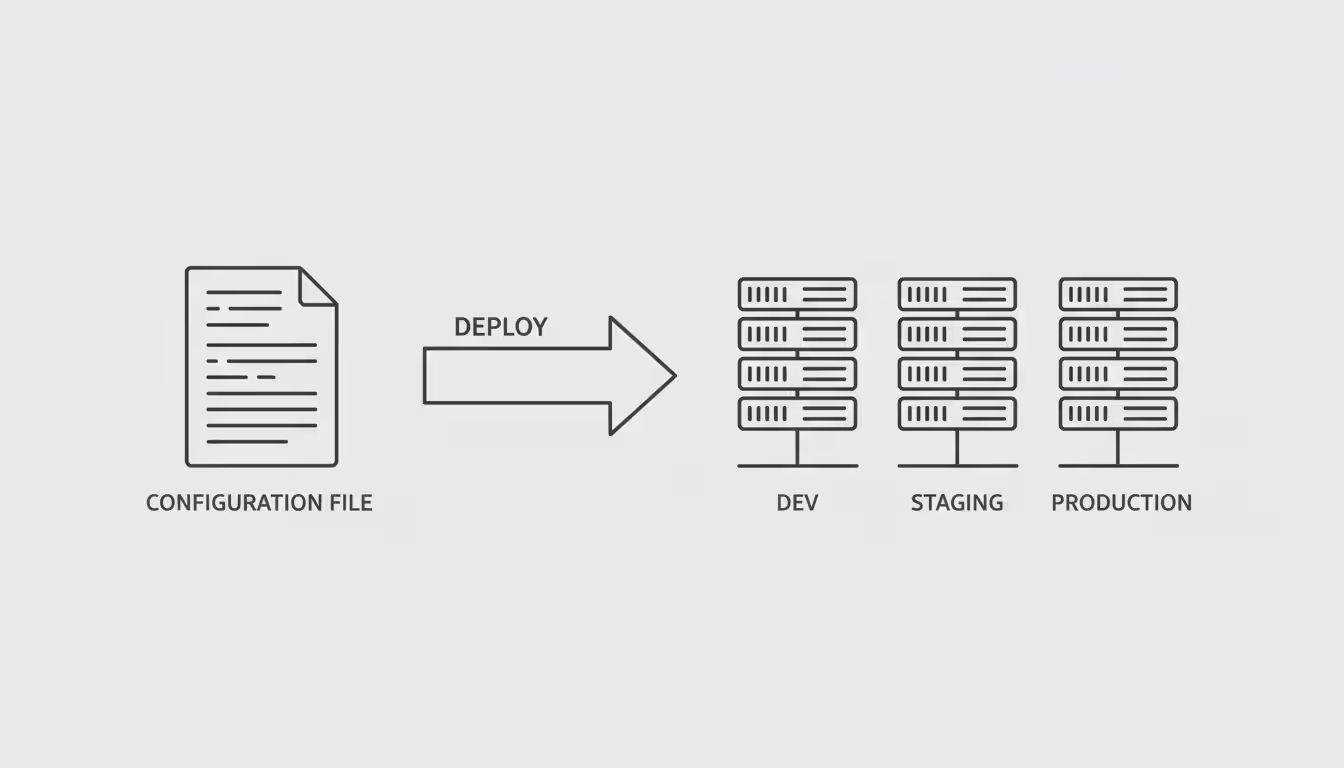
Infrastructure as Code eliminates these nightmare scenarios. Instead of managing servers through point-and-click dashboards or memorizing terminal commands, you'll define everything in plain text files—the same files you can store in Git, review during standup meetings, and run whenever you need an identical environment.
Think about it: developers wouldn't dream of tracking application changes in a Word document. Why should infrastructure be any different? When your infrastructure exists as code, spinning up a complete testing environment takes five minutes instead of two days. No more "works on my machine" excuses when dev and prod are built from identical specifications.
What Is Infrastructure as Code?
Here's the straightforward definition: infrastructure as code treats your servers, databases, networks, and related resources as text-based configurations rather than things you set up by hand or through graphical interfaces.
Picture a restaurant recipe. A skilled chef could describe their signature dish verbally, but every time a different cook prepares it, the result varies slightly. Write down the exact recipe—measurements, temperatures, timing—and you get consistency. That's what infrastructure-as-code does for your tech stack.
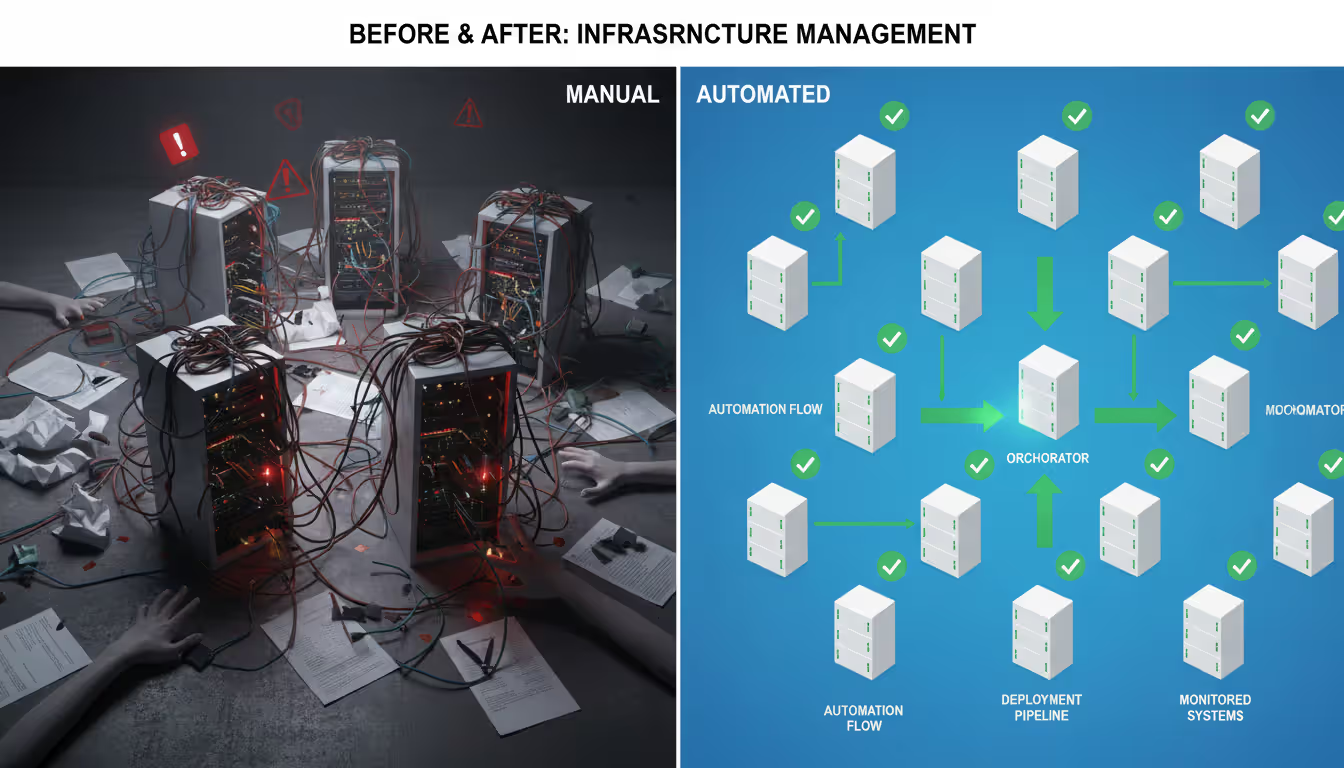
The old way meant logging into each server individually, clicking through AWS or Azure consoles, running commands one at a time, then documenting what you did in a wiki (that probably got outdated within a week). Two engineers configuring "identical" systems would make different choices about disk sizes, network rules, or software versions. Good luck rebuilding a crashed server from those notes six months later.
With infrastructure as a code, you write down your desired configuration once. That file goes into version control alongside your application code. Need to review what changed? Check the Git history. Want to deploy the same setup in a different region? Run the same file against new credentials. Spot a security issue? Fix it in one place, then roll out the correction everywhere.
Real companies use this daily. An e-commerce site provisions 50 extra application servers every Black Friday, then tears them down on December 1st. A healthcare provider maintains an exact replica of production in a compliance-testing environment. A startup gives every developer their own isolated sandbox that matches production perfectly—no more debugging issues that only appear in prod.
Author: Derek Hollowell;
Source: clatsopcountygensoc.com
How Infrastructure as Code Works
You start by writing config files that describe what you want your infrastructure to look like. Depending on which tool you pick, you might write in a specialized language like HCL, use YAML markup, or even stick with Python or TypeScript if that's more comfortable.
These files sit in your Git repository right next to application code. Every change gets tracked—who modified what, when, and why.
Now, there are two philosophies here: declarative and imperative. They're different enough that you should understand both.
Declarative style: You specify the end result. "I want three Ubuntu servers with 8GB RAM behind a load balancer." The tool figures out whether it needs to create new resources, update existing ones, or leave things alone. Terraform works this way. So does CloudFormation. You describe the destination; the software plans the journey.
Imperative style: You write out the steps. "Create a VM. Install these packages. Copy this config file. Restart that service." You control the sequence. Ansible follows this pattern. Sometimes you need that granular control, especially for complex configuration tasks.
When you execute your infrastructure code, the tool talks to your cloud provider's API. For AWS, it calls the AWS API. For on-premises VMware infrastructure, it uses vSphere APIs. The tool compares your current state against your desired state, calculates what needs to change, then makes those changes happen.
Here's where version control transforms everything. Infrastructure changes flow through the same review process as code changes:
Sarah needs to add a database. She edits the Terraform file and opens a pull request. Automated checks validate syntax and scan for security issues (did she accidentally expose port 3306 to the internet?). The system calculates the cost impact. Mark reviews the change and suggests increasing backup retention from 7 to 30 days. Sarah updates the file. After approval, the change merges, and CI/CD automatically applies it to staging. Integration tests run. Everything passes. Sarah clicks the production deployment button, and five minutes later, the database is live.
Nobody manually clicked through the AWS console. Everything got reviewed. The change is documented forever in Git. If there's a problem, reverting means running the previous version of the file.

Author: Derek Hollowell;
Source: clatsopcountygensoc.com
Infrastructure as Code Examples and Tools
Looking at actual infrastructure as code examples shows you how different tools approach the same problems. Each has sweet spots that make it perfect for certain situations.
Terraform Example
Terraform uses HashiCorp Configuration Language (HCL), which reads almost like English but stays machine-parseable. Here's how you'd provision an AWS web server:
provider "aws" { region = "us-east-1"
} resource "aws_instance" "web_server" { ami = "ami-0c55b159cbfafe1f0" instance_type = "t3.medium" tags = { Name = "production-web-01" Environment = "production" } vpc_security_group_ids = [aws_security_group.web_sg.id]
} resource "aws_security_group" "web_sg" { name = "web-server-sg" description = "Allow HTTP and HTTPS traffic" ingress { from_port = 80 to_port = 80 protocol = "tcp" cidr_blocks = } ingress { from_port = 443 to_port = 443 protocol = "tcp" cidr_blocks = }
}
Terraform maintains a state file tracking which cloud resources belong to which code. Run terraform plan and you'll see exactly what will change before anything actually happens. No surprises.
The killer feature? Terraform works across practically any provider. Same workflow for AWS, Azure, Google Cloud, even services like DataDog or PagerDuty. If you're avoiding vendor lock-in or managing multiple clouds, Terraform makes sense.
AWS CloudFormation Example
CloudFormation templates use JSON or YAML to define AWS resources specifically. Here's that same web server:
AWSTemplateFormatVersion: '2010-09-09'
Description: 'Web server with security group' Resources: WebServerSecurityGroup: Type: AWS::EC2::SecurityGroup Properties: GroupDescription: Allow HTTP and HTTPS traffic SecurityGroupIngress: - IpProtocol: tcp FromPort: 80 ToPort: 80 CidrIp: 0.0.0.0/0 - IpProtocol: tcp FromPort: 443 ToPort: 443 CidrIp: 0.0.0.0/0 WebServer: Type: AWS::EC2::Instance Properties: ImageId: ami-0c55b159cbfafe1f0 InstanceType: t3.medium SecurityGroupIds: - !Ref WebServerSecurityGroup Tags: - Key: Name Value: production-web-01 - Key: Environment Value: production
CloudFormation shines if you're all-in on AWS. It understands resource dependencies automatically, creates things in the right order, and rolls back failed deployments. AWS manages state tracking for you—no separate files to worry about.
The downside? It only works with AWS. Multi-cloud setups need a different solution.
Ansible Example
Ansible takes the imperative route with YAML playbooks that spell out each step:
---
- name: Configure web server hosts: web_servers become: yes tasks: - name: Update package cache apt: update_cache: yes - name: Install Nginx apt: name: nginx state: present - name: Copy website configuration template: src: templates/nginx.conf.j2 dest: /etc/nginx/sites-available/default notify: Restart Nginx - name: Ensure Nginx is running service: name: nginx state: started enabled: yes handlers: - name: Restart Nginx service: name: nginx state: restarted
Ansible excels at configuration management—installing software, managing config files, controlling services on existing servers. It connects over SSH without requiring agent software on target machines. Many teams use Terraform to provision infrastructure, then Ansible to configure what runs on that infrastructure.
Benefits of Using Infrastructure-as-Code
The speed difference hits you immediately. Manually configuring a server might take two hours—finding the runbook, navigating menus, installing packages, testing connections. Automate it with IaC and it's done in five minutes. Do that across dozens of systems or hundreds of deployments per year, and you've saved literal weeks of engineering time.
Consistency stops being a problem. When every environment comes from the same code, you don't get configuration drift. No more mysteries where code works perfectly in development but crashes in production because prod has a slightly different database version or missing environment variable. Security rules apply everywhere because they're baked into your infrastructure definitions rather than relying on manual checklists.
Disaster recovery transforms from a stressful emergency into a routine operation. You already have every component documented in code. Recovering from a major outage means running your IaC tool against a backup region or different datacenter. I've seen teams lose an entire datacenter and restore production in 40 minutes—something that would've taken days with manual rebuilding.
Author: Derek Hollowell;
Source: clatsopcountygensoc.com
Cost savings come from multiple angles. Automation prevents waste—dev environments accidentally left running all weekend, staging systems consuming resources 24/7 when you only need them during business hours. With IaC, tearing down and rebuilding environments is trivial, so you only pay for what you're actively using. One team I know cut their AWS bill by 60% just by automatically destroying dev environments outside 9-5.
Team collaboration improves dramatically. Infrastructure changes become visible and reviewable. Junior engineers learn from senior team members' configurations. Code review catches mistakes before they hit production. Knowledge stops living only in people's heads—it's captured in executable code that anyone can read and modify.
Infrastructure as Code is not just about automation—it's about making infrastructure a first-class citizen in your software development process. When infrastructure changes go through the same testing, review, and deployment pipelines as application code, reliability improves exponentially
— Kelsey Hightower
Common Mistakes When Implementing IaC
Hardcoding credentials directly into your IaC files is asking for trouble. Once passwords or API keys hit your Git repository, they're compromised—even if you delete them later, they stay in Git history. Use proper secret management (AWS Secrets Manager, HashiCorp Vault, Azure Key Vault) and reference secrets by identifier, never embedding the actual values.
Skipping test environments is like deploying application code straight to production without testing it first. Eventually, something breaks catastrophically. Maintain a staging environment where you can safely validate infrastructure changes. The cost of running a small test environment is nothing compared to the business impact when an untested change takes down production.
Ignoring state management causes chaos with tools like Terraform. When two people run the same configuration simultaneously without proper state locking, you risk corrupting state files, creating orphaned resources, or accidentally deleting things. Set up remote state storage with locking—S3 with DynamoDB for Terraform, or use Terraform Cloud's managed state.
Bypassing code review wastes IaC's collaborative benefits. Infrastructure affects everyone—developers, operations, security, finance. Requiring pull request reviews catches errors early, spreads knowledge across the team, and ensures changes align with organizational policies. One person accidentally deleting a production database without oversight can destroy months of work.
Over-engineering your initial setup makes IaC harder to maintain than the manual process it replaced. Teams new to infrastructure as code iac often try handling every possible scenario with complex conditionals and loops. Start simple. Build basic configurations for immediate needs. Only refactor toward reusability after you've seen actual patterns emerge from real usage.

Author: Derek Hollowell;
Source: clatsopcountygensoc.com
Infrastructure as Code vs Infrastructure as a Service
People constantly confuse IaC and IaaS because the acronyms look similar and both involve infrastructure. They're actually complementary technologies, not alternatives.
Infrastructure as a Service refers to cloud computing where vendors rent you computing power over the internet. Think AWS EC2, Azure Virtual Machines, Google Compute Engine. Instead of buying physical servers, you rent virtual ones from cloud providers. You control the OS, applications, and settings; the provider handles physical hardware, networking gear, and datacenter operations.
Infrastructure as code is a methodology for managing infrastructure—whether cloud-based, physical hardware, or platform services—through automated configuration. IaC answers "how do I configure and deploy my infrastructure?" while IaaS answers "where will my workloads actually run?"
They work beautifully together. Most modern organizations use IaC to provision and manage IaaS resources. You might write Terraform that creates AWS EC2 instances (that's the IaaS part), sets up networking, attaches storage, and configures load balancers. The IaaS provider supplies virtualized resources; your IaC tools automate how they're configured and orchestrated.
| Feature | Infrastructure as Code | Infrastructure as a Service |
| What it is | Methodology for managing infrastructure through version-controlled configuration files | Cloud service model providing on-demand virtual computing resources |
| Main goal | Automate infrastructure provisioning and ensure consistency | Provide computing capacity without buying physical hardware |
| Common tools | Terraform, Ansible, CloudFormation, Pulumi | AWS EC2, Microsoft Azure VMs, Google Compute Engine, DigitalOcean Droplets |
| Control level | Full control over infrastructure definitions and deployment automation | Control OS, apps, and configurations; provider manages physical infrastructure |
| Cost structure | Tools are mostly free or low-cost (fees for enterprise features/support) | Pay-per-use billing based on compute hours, storage, bandwidth |
| Best used for | Standardizing deployments and eliminating manual configuration | Running workloads without capital expenses for data center equipment |
You can absolutely use IaC without IaaS—like running Ansible against physical servers in your own datacenter. You can use IaaS without IaC—manually creating cloud resources through web consoles. But the combination delivers the best results: IaaS gives you flexibility and scalability, while IaC adds consistency and automation on top.
Frequently Asked Questions About Infrastructure as Code
Infrastructure as code represents a fundamental shift in how organizations approach technology infrastructure. By applying code-based practices to infrastructure management, teams gain the same advantages that transformed software development decades ago: version control, automated testing, peer review, and continuous deployment.
The transition requires investment—learning new tools, changing established workflows, developing different skills. But organizations making this investment consistently report massive improvements in deployment speed, system reliability, and team productivity. Managing infrastructure manually increasingly resembles writing software without version control or automated testing—something that once seemed reasonable but has clearly been superseded.
Start small. Pick one piece of infrastructure that frequently causes problems or consumes too much time. Automate it with IaC. Measure the improvement. Expand to other components. Gradually, you'll build a library of tested, reusable infrastructure configurations that become your organization's living infrastructure knowledge base—executable, always current, and available to everyone who needs it.
Related Stories

Read more

Read more

The content on this website is provided for general informational and educational purposes related to cloud computing, network infrastructure, and IT solutions. It is not intended to constitute professional technical, engineering, or consulting advice.
All information, tools, and explanations presented on this website are for general reference only. Network environments, system configurations, and business requirements may vary, and results may differ depending on specific use cases and infrastructure.
This website is not responsible for any errors or omissions, or for actions taken based on the information, tools, or technical recommendations presented.




